Why Vulnerabilities Are Increasing in the AI Era?
The cybersecurity landscape is undergoing a fundamental transformation. Over the past few years, organizations have witnessed a sharp increase in reported vulnerabilities, with global disclosures crossing 20,000+ annually.
Why Vulnerabilities Are Increasing in the AI Era?
The cybersecurity landscape is undergoing a fundamental transformation. Over the past few years, organizations have witnessed a sharp increase in reported vulnerabilities, with global disclosures crossing 20,000+ annually. While this surge may appear alarming, it does not necessarily indicate that systems are becoming inherently insecure.
Instead, the rise of flaws reflects a deeper shift in how modern technology is built, deployed, and attacked. The rapid adoption of Artificial Intelligence (AI), cloud computing, and interconnected digital ecosystems has fundamentally changed both the scale and speed of cybersecurity risks.
Today, the challenge is no longer just about identifying vulnerabilities; it is about understanding how quickly they can be exploited and how effectively organizations can respond.
Why the Numbers Keep Climbing?
One of the primary reasons behind the increasing number of vulnerabilities is the rapid evolution of modern IT environments. Organizations are embracing cloud-native architectures, SaaS platforms, microservices, and API-driven systems. While these technologies enable scalability and innovation, they also introduce multiple layers of complexity. Each integration point, API endpoint, and third-party dependency becomes a potential entry point for attackers.
Additionally, the software supply chain has expanded significantly. Modern applications rely heavily on open-source components and external libraries. While this accelerates development, it also increases exposure to inherited vulnerabilities that may go unnoticed.
AI has further amplified vulnerability discovery. Advanced tools can now scan massive codebases, identify patterns, and detect anomalies at a scale that was previously impossible. As a result, more vulnerabilities are being uncovered, not because they are newly created, but because they are now easier to find.
This shift highlights an important reality: the increase in vulnerabilities is driven as much by improved visibility as it is by growing complexity.
AI in Cybersecurity: A Double-Edged Advantage
Artificial Intelligence is playing a dual role in the cybersecurity ecosystem, influencing both attackers and defenders.
Offensive Use of AI
Threat actors are increasingly leveraging AI to exploit vulnerabilities more efficiently. AI enables:
Automated scanning for weaknesses across large attack surfaces
Rapid analysis of newly disclosed flaws
Generation of exploit code with minimal manual effort
Scalable reconnaissance across systems and networks
This significantly reduces the technical expertise required to launch sophisticated attacks. As a result, even less experienced attackers can identify and exploit vulnerabilities effectively.
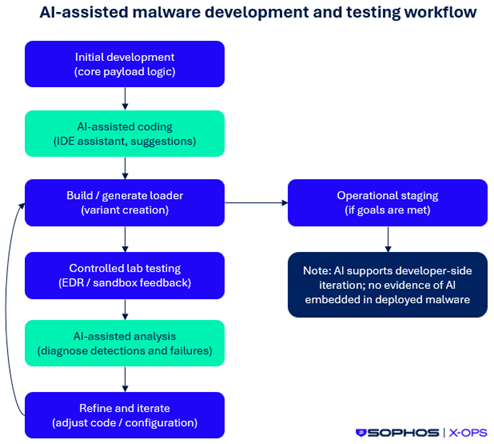
Beyond automation, AI is also enabling attackers to refine their strategies. Machine learning models can analyze past attack patterns, identify the most successful exploitation techniques, and optimize future attacks. AI-driven phishing campaigns, deepfake-based social engineering, and adaptive malware are further accelerating the exploitation of flaws.
In many cases, attackers are now able to move from vulnerability discovery to exploitation in a matter of hours, compressing timelines that once took weeks or months.
Defensive Use of AI
On the defensive side, organizations are using AI to strengthen their security posture. AI-driven tools help:
Detect hidden vulnerabilities in complex systems
Perform intelligent code reviews
Enhance threat detection and monitoring
Improve incident response times
AI also enables predictive security capabilities. By analyzing historical data and behavioral patterns, security systems can anticipate potential flaws and flag high-risk areas before they are exploited. This allows organizations to shift from reactive to proactive security strategies.
Additionally, AI-powered security platforms can prioritize vulnerabilities based on risk, exploitability, and potential business impact. This helps security teams focus their efforts where it matters most, especially in environments with thousands of flaws.
Blog Form
Book Your Free Cybersecurity Consultation Today!
Expanding Attack Surfaces, Bigger Consequences
The nature of vulnerabilities is evolving as attackers shift their focus toward high-impact systems.
Earlier, most flaws were concentrated in web browsers and consumer applications. Today, attackers are targeting:
Cloud infrastructure
Network appliances like VPNs and firewalls
Enterprise SaaS platforms
APIs and backend systems
These systems are deeply integrated into business operations. A single exploited vulnerability can lead to large-scale consequences, including data breaches, operational disruption, and lateral movement across networks. As attack surfaces expand, the potential damage caused by vulnerabilities increases significantly.
What Makes AI-Driven Cyberattacks Different?
There are five defining traits of AI-powered cyberattacks:
Attack Automation: Cyberattacks that once required heavy human involvement can now be automated using AI and generative AI tools, enabling faster research and execution.
Faster Data Gathering: Reconnaissance, the first stage of any attack, is now accelerated with AI. It helps attackers quickly identify targets, flaws, and valuable assets with greater accuracy.
Personalization at Scale: AI can collect and analyze publicly available data from sources like social media and websites, allowing attackers to craft highly targeted and convincing phishing or social engineering attacks.Adaptive Learning: With reinforcement learning, AI continuously evolves in real time, helping attackers refine their methods, improve success rates, and evade detection more effectively.
Cyber Security Squad – Newsletter Signup
.newsletterwrap .containerWrap {
width: 100%;
max-width: 800px;
margin: 25px auto;
}
/* Card styles */
.newsletterwrap .signup-card {
background-color: white;
border-radius: 10px;
overflow: hidden;
box-shadow: 0 4px 12px rgba(0, 0, 0, 0.1);
border: 8px solid #e85d0f;
}
.newsletterwrap .content {
padding: 30px;
display: flex;
justify-content: space-between;
align-items: center;
flex-wrap: wrap;
}
/* Text content */
.newsletterwrap .text-content {
flex: 1;
min-width: 250px;
margin-right: 20px;
}
.newsletterwrap .main-heading {
font-size: 26px;
color: #333;
font-weight: 900;
margin-bottom: 0px;
}
.newsletterwrap .highlight {
color: #e85d0f;
font-weight: 500;
margin-bottom: 15px;
}
.newsletterwrap .para {
color: #666;
line-height: 1.5;
margin-bottom: 10px;
}
.newsletterwrap .bold {
font-weight: 700;
}
/* Logo */
.newsletterwrap .rightlogo {
display: flex;
flex-direction: column;
align-items: center;
margin-top: 10px;
}
.newsletterwrap .logo-icon {
position: relative;
width: 80px;
height: 80px;
margin-bottom: 10px;
}
.newsletterwrap .c-outer, .c-middle, .c-inner {
position: absolute;
border-radius: 50%;
border: 6px solid #e85d0f;
border-right-color: transparent;
}
.newsletterwrap .c-outer {
width: 80px;
height: 80px;
top: 0;
left: 0;
}
.newsletterwrap .c-middle {
width: 60px;
height: 60px;
top: 10px;
left: 10px;
}
.newsletterwrap .c-inner {
width: 40px;
height: 40px;
top: 20px;
left: 20px;
}
.newsletterwrap .logo-text {
color: #e85d0f;
font-weight: 700;
font-size: 0.9rem;
text-align: center;
}
/* Form */
.newsletterwrap .signup-form {
display: flex;
padding: 0 30px 30px;
}
.newsletterwrap input[type=”email”] {
flex: 1;
padding: 12px 15px;
border: 1px solid #ddd;
border-radius: 4px 0 0 4px;
font-size: 1rem;
outline: none;
}
.newsletterwrap input[type=”email”]:focus {
border-color: #e85d0f;
}
.newsletterwrap .submitBtn {
background-color: #e85d0f;
color: white;
border: none;
padding: 12px 20px;
border-radius: 0 4px 4px 0;
font-size: 1rem;
cursor: pointer;
transition: background-color 0.3s;
white-space: nowrap;
}
.newsletterwrap button:hover {
background-color: #d45000;
}
/* Responsive styles */
@media (max-width: 768px) {
.newsletterwrap .content {
flex-direction: column;
text-align: center;
}
.newsletterwrap .text-content {
margin-right: 0;
margin-bottom: 20px;
}
.newsletterwrap .rightlogo {
margin-top: 20px;
}
}
@media (max-width: 480px) {
.newsletterwrap .signup-form {
flex-direction: column;
}
.newsletterwrap input[type=”email”] {
border-radius: 4px;
margin-bottom: 10px;
}
.newsletterwrap .submitBtn {
border-radius: 4px;
width: 100%;
}
}
]]>
Join our weekly newsletter and stay updated
CYBER SECURITY SQUAD
Strategies to Counter AI-Powered Cyberattacks?
AI is transforming the threat landscape, making cyberattacks faster, more scalable, and increasingly sophisticated. As attackers leverage AI to exploit weaknesses, organizations must shift their focus toward proactively identifying and mitigating AI-powered vulnerabilities.
Here are key strategies to strengthen defenses:
Continuously Assess and Monitor Your Environment
Mitigating flaws starts with visibility.
Conduct regular and continuous security assessments to identify weaknesses across systems.
Deploy integrated security platforms with real-time monitoring, intrusion detection, and endpoint protection.
Establish behavioral baselines for users and systems, and implement User and Entity Behavior Analytics (UEBA) to detect anomalies.
Monitor for unusual activity or unexpected system changes that could signal an attack.
Analyze AI/ML system inputs and outputs in real time to detect and prevent adversarial manipulation.
Build a Strong Incident Response Framework
Even with strong defenses, flaws can be exploited; preparedness is critical.
Preparation: Define processes to prevent and respond to AI-driven threats.
Detection & Analysis: Identify incidents quickly and assess their nature and impact.
Containment & Eradication: Limit the spread of attacks and remediate flaws effectively.
Recovery: Strengthen systems post-incident to prevent recurrence and improve resilience.
Adopt AI-Driven Security Solutions
The most effective way to mitigate AI-powered vulnerabilities is to use AI defensively.
Leverage solutions like AutoSecT, an AI-driven pentesting platform, to proactively identify, prioritize, and remediate vulnerabilities before they can be exploited.
Adopt AI-native cybersecurity tools to analyze large volumes of data and detect patterns at scale. Automate critical security operations such as monitoring, threat detection, patching, and remediation to improve efficiency and response time.
Additionally, configure intelligent alerts to highlight high-risk flaws, enabling security teams to focus on what matters most and respond faster to potential threats.
Conclusion
The rise in vulnerabilities is not just a reflection of growing risk; it is a signal of how rapidly the cybersecurity landscape is evolving in the AI era. As digital ecosystems expand and AI accelerates both discovery and exploitation, the window between vulnerability identification and attack execution continues to shrink.
At the same time, AI is not just a challenge; it is also a powerful enabler. Organizations that leverage AI-driven security, continuous monitoring, and proactive risk management can stay ahead of emerging threats. The focus must shift from reactive patching to intelligent prioritization, faster response, and resilience by design.
In this new reality, success depends on how effectively organizations balance innovation with security. Those who embrace AI defensively, strengthen their security foundations, and prioritize visibility across their environments will be better equipped to manage flaws at scale.
FAQs
How can organizations reduce AI-driven vulnerabilities?
By adopting continuous monitoring, strong incident response, and AI-driven security solutions.
What role does AutoSecT play in vulnerability management?
AutoSecT helps identify, prioritize, and remediate vulnerabilities using AI-driven pentesting and insights.
How can organizations prioritize which vulnerabilities to fix first?
Focus on flaws that have high exploitability and potential business impact. AI-driven platforms can help by ranking risks based on real-world threat intelligence.
The post Why Vulnerabilities Are Increasing in the AI Era? appeared first on Kratikal Blogs.
*** This is a Security Bloggers Network syndicated blog from Kratikal Blogs authored by Shikha Dhingra. Read the original post at: https://kratikal.com/blog/why-vulnerabilities-are-increasing-in-the-ai-era/