N8N: Shared Credentials and Account Takeover
Executive Summary
We identified a security weakness in n8n’s credential management layer that could have completely compromised the application’s security.
N8N: Shared Credentials and Account Takeover
Executive Summary
We identified a security weakness in n8n’s credential management layer that could have completely compromised the application’s security. This finding highlights the core risks of centralized authentication in workflow automation platforms.
As n8n serves as the central hub connecting critical systems and orchestrating business processes across teams, any gap in credential handling can potentially cascade across connected systems, disrupting operations, compromising data flows, and credentials.
While this issue was fixed in v2.6.4, it reminds us about the unique security challenges of AI automation platforms.
Introduction
We are in a moment where AI and automation platforms are rapidly becoming embedded in everyday operations, allowing teams to connect models, APIs, SaaS tools, and internal systems with minimal friction.
Platforms like n8n promise powerful automation through visual workflows and reusable credentials, lowering the barrier to orchestrating complex tasks across services. But this convenience comes with structural risk: these tools centralize highly sensitive tokens, OAuth flows, and API keys, effectively concentrating trust in a single automation layer.
When that layer fails to enforce basic security controls, the impact is not limited to one workflow, it can extend across every connected system. In this research, we examine how a Stored XSS vulnerability in n8n’s OAuth credential handling can lead to account takeover and broader instance compromise.
The Vulnerability
The vulnerability lies in how n8n handles the “Authorization URL” within the OAuth credential setup. OAuth (Open Authorization) is an authorization framework that allows an application to access a user’s data on another service without exposing the user’s password.
In a standard workflow, users configure OAuth credentials to authenticate n8n with an external provider. When a user clicks “Connect my account,” n8n opens a popup window pointing to the service’s authorization page.
However, we discovered that the frontend function responsible for opening this window did not validate the protocol of the provided URL (see below). This allowed an attacker to bypass the expected scheme and inject JavaScript code.
The Attack Flow
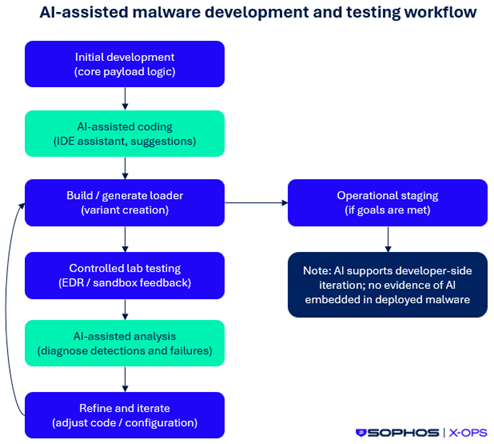
Because n8n allows credentials to be shared between users in the same instance (collaborative features), a threat actor can weaponize this weakness, see Fig 1.
Fig. 1: High level view of the attack flow
The steps are the following:
Preparation: The attacker creates a new credential using the “OAuth2 API” type.
Injection: In the “Authorization URL” field, instead of a valid URL, the attacker inserts a malicious JavaScript payload.
Trap: The attacker shares this credential with the victim (e.g., an administrator or a user with higher privileges).
Execution: The victim, seeing a shared credential, opens it and clicks “Connect my account.” The browser immediately executes the injected JavaScript in the context of the victim’s session instead of navigating to the remote authorization URL.
Demonstration Video
The following video demonstrates the exploitation chain: sharing the malicious credential with a victim account and triggering the XSS payload.
Root Cause
During the OAuth flow, the browser initiates a top-level navigation to the authorization URL in the oAuthCredentialAuthorize function of the credential service. However, this segment of the program missed sanitation of the Authorization URL.
Fig. 2: Vulnerable source code
Impact: Application Compromise
This is a stored XSS, meaning the payload is saved permanently in the database and served to any user who interacts with the credential. The impact of executing arbitrary JavaScript in the context of an n8n session is significant:
Account Takeover: The attacker can impersonate the victim’s in his session and force actions on their behalf, effectively taking over the account.
Credential Exfiltration: The attacker can then use the XSS to query the internal n8n API and retrieve other credentials stored in the instance.
Instance Control: With admin access gained via the XSS, the attacker can access more credentials, escalate privileges, and gain full control of the n8n instance.
Conclusion
Workflow automation tools like n8n are becoming the backbone of modern IT infrastructure. While they offer immense power and speed, they also centralize trust. A vulnerability in this layer can often be more damaging than a vulnerability in a single isolated application.
We recommend organizations treat their automation platforms as Tier-0 assets, enforce strict access controls, and ensure they are patched promptly.
Timeline
Jan 29 : Disclosure of the issue
Feb 6 : Issue fixed in v2.6.4
The post N8N: Shared Credentials and Account Takeover appeared first on Blog.
*** This is a Security Bloggers Network syndicated blog from Blog authored by Yohann Sillam. Read the original post at: https://www.imperva.com/blog/n8n-shared-credentials-and-account-takeover/