Hacktivist campaigns increase as United States, Iran, and Israel conflict intensifies
Counter Threat Unit™ (CTU) researchers are monitoring an elevated volume of Iranian hacktivist chatter across Telegram, X, and underground forums following coordinated military strikes that the U.S. and Israel launched across Iran on February 28, 2026. These operations, known as Operation Epic Fury in the U.S. and Operation Roaring Lion in Israel, targeted Iranian military sites and leadership. Some of the hacktivist groups have been active for years, while others are emerging as the conflict intensifies. Historically, many pro-Iran hacktivist attacks have had low sophistication and limited success. It is possible that Iranian state-sponsored groups may conduct high-sophistication retaliatory attacks, but those types of attacks have not been observed as of this publication. Most alleged attacks have been focused on website defacement, distributed denial of service (DDoS), and the doxxing of individuals connected to Israeli government, military, and associated organizations.
Handala Hack Team is an Iranian hacktivist persona that was first observed in 2023 and is operated by COBALT MYSTIQUE. During Operation Rising Lion in June 2025, the Handala Hack Team’s Telegram activity escalated within hours of the strikes. Handala Hack Team has regularly posted on X and Telegram regarding threats to Israeli citizens’ safety and claims of attacks on Israeli infrastructure (see Figure 1).
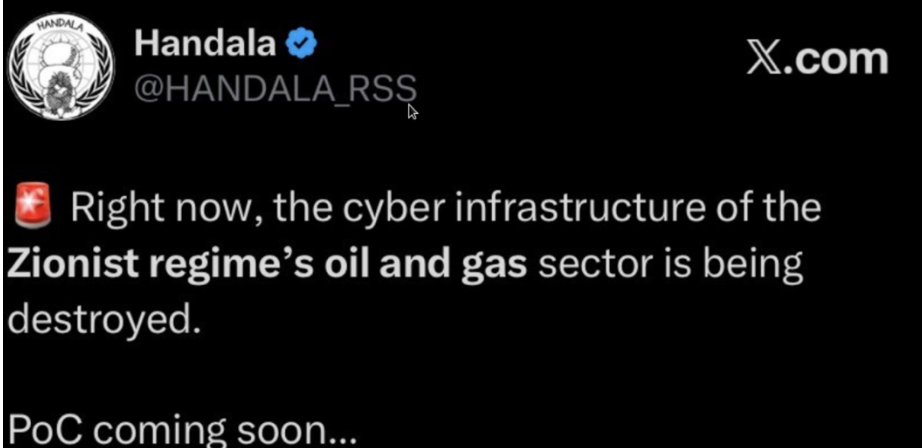
Figure 1: Handala Hack team sharing unverified attack on Israel oil and gas sector
Furthermore, Handala Hack Team launched a “RedWanted” site on March 1 that lists names and summaries of individuals and organizations who have supported Israel (see Figure 2). The threat actors stated they will “hunt” until “justice is served” (see Figure 3).
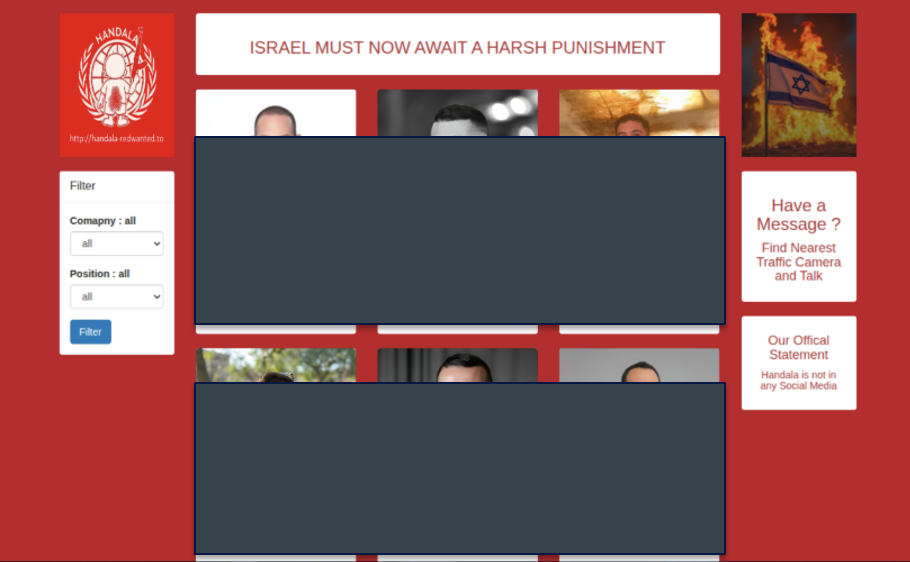
Figure 2: List of Israel supporters on Handala RedWanted site (redacted)
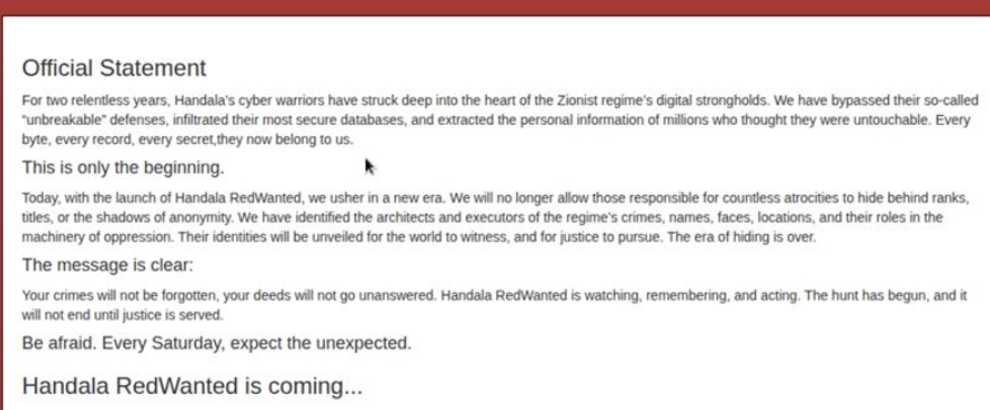
Figure 3: Handala RedWanted warning
The APTIran hacktivist group has also ramped up activity on its Telegram site, encouraging pro-Iran hackers to pursue cyberattacks and retaliation. Third-party reporting has attributed APTIran to several major cyber campaigns targeting Israel. Since February 28, the group has shared leaks and compromises via Telegram that allegedly pertain to Israeli critical infrastructure and organizations (see Figure 4).
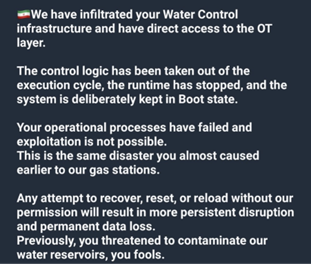
Figure 4: APTIran post about unverified compromise of Israeli water control infrastructure
Other pro-Iran hacktivist groups have re-engaged or emerged in the wake of the conflict, including Cyber Toufan, Cyber Support Front, and Iranian Avenger. CTU researchers have observed several of these groups sharing misinformation and inciting violence. There have also been instances of groups reactivating; for example, Cyb3r Drag0nz claims to have joined a larger team called the ‘Electronic Operations Room of Islamic Resistance Axis’ with aims to disrupt Israeli organizations and infrastructure. CTU researchers have also identified the BaqiyatLock (also known as BQTlock) ransomware-as-a-service (RaaS) group offering free affiliate memberships to any hacktivists who can “target the Zionist entity” (see Figure 5). Many of these emerging or reactivated groups mainly engage in unsophisticated tactics, broad and embellished claims, and narrative amplification, rather than delivering materially significant impacts.
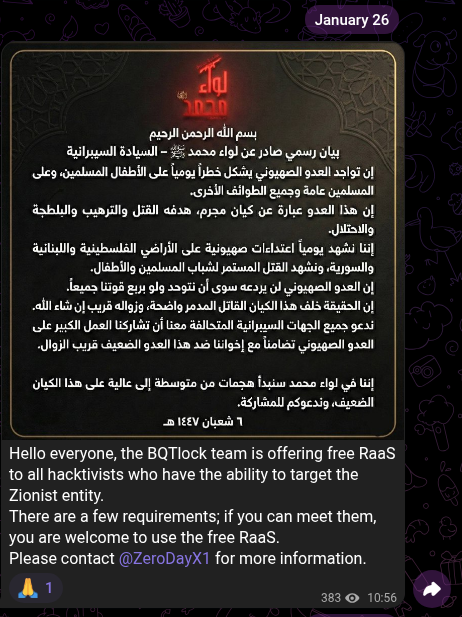
Figure 5: BaqiyatLock Telegram post offering free RaaS usage to Iranian hacktivists
Third parties have reported several cyberattacks to Iranian organizations and systems that CTU researchers have not verified. For example, claims have been shared across social media platforms about the compromise of an Iranian prayer application to directly message Iranian citizens, as well as alleged compromises of media outlets and critical infrastructure organizations.
CTU researchers have also observed reports of pro-Israel hacktivist personas engaging in cyber operations within this conflict. For example, Troll Hacker Team has claimed to have initiated activities to counter Iranian cyberattacks (see Figure 6).
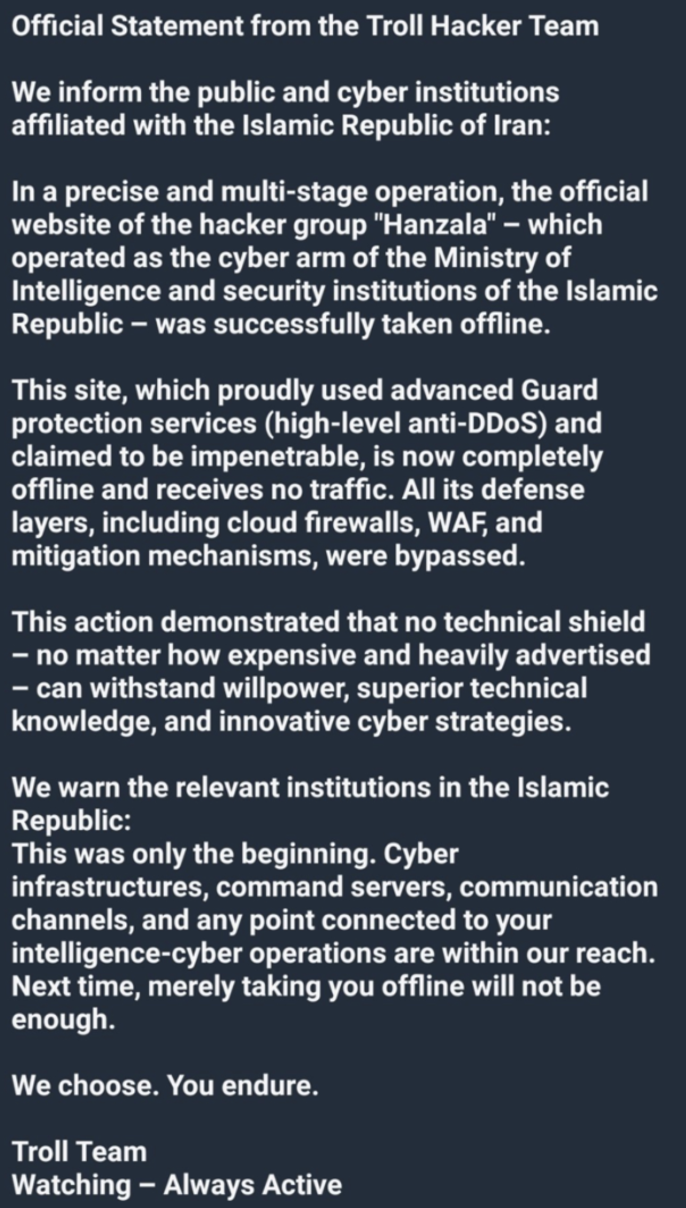
Figure 6: Troll Hacker Team post from Telegram captured on March 1, 2026
While much of the focus of this Iranian hacktivist activity has been directed at Israeli organizations and interests, the U.S. role in strikes could increase the risk of retaliatory attacks against U.S. organizations. In addition, regional military strikes conducted by Iran suggest that organizations in Gulf Cooperation Council (GCC) States are likely to be at elevated risk of reprisal attacks. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has published multiple advisories and warnings about Iranian threats over the years.
CTU researchers recommend that organizations adopt a heightened defensive posture, particularly entities operating in the U.S. and Middle East. The UK National Cyber Security Centre published a list of resources that can help organizations strengthen their defenses. Organizations should maintain awareness for topical phishing campaigns, password-spraying activity, and other credential attacks. Minimizing internet-facing services and expediting patching of internet-facing systems reduces the available attack surface. Iranian groups routinely target publicly disclosed vulnerabilities rather than exploiting zero-days, so organizations should prioritize patching vulnerabilities listed in CISA’s Known Exploited Vulnerabilities Catalog.
Additionally, it is important to maintain a focus on fundamental protective monitoring practices such as implementing and maintaining antivirus solutions and monitoring endpoint detection and response solutions. Organizations should also review their business continuity plans and restoration processes to address ransomware or wiper malware attacks.
Sophos published an advisory on March 1 regarding the cyber threats posed by the conflict among the U.S., Israel, and Iran. This advisory will be updated as the situation develops, so monitor it for the latest information on observed activity and recommendations.