What It Costs to Hire a Hacker on the Dark Web in 2026
The dark web continues to fuel a growing underground economy where cybercriminals buy and sell stolen data, malicious tools, and hacking services.
In 2026, the barrier to entry for cybercrime is lower than ever, allowing threat actors with limited technical skill to purchase ransomware kits, stolen credentials, or even hire malicious hackers for targeted attacks.
Key Takeaways from the Dark Web Findings
- Cybercrime services on the dark web have become highly commercialized, making hacking tools and stolen data widely accessible in 2026.
- Ransomware-as-a-Service (RaaS) allows criminals with little technical skill to launch sophisticated ransomware attacks.
- Stolen financial accounts, corporate access credentials, and medical records command some of the highest prices on underground markets.
- Initial Access Brokers (IABs) sell verified access to corporate networks, with high-level administrative access sometimes worth tens of thousands of dollars.
- Individuals and organizations can reduce overall risk through MFA, password managers, dark web monitoring, identity theft protection, and employee security awareness training.
Dark Web Price Snapshot
Please note the pricing below is from Deepstrike’s findings. Dark Web pricing varies based on the marketplace and on external factors (e.g., law enforcement takedowns).
| US Social Security Number | $1–$6 |
| Full Identity Package (“Fullz”) | $20–$100+ |
| US Credit Card with CVV | $10–$40 |
| High-Limit Credit Card | $110–$120 |
| Online Bank Login | $200–$1,000+ |
| Verified Coinbase Account | $120–$250 |
| Verified Kraken Account | Up to $1,170 |
| Gmail Account | $60–$65 |
| Driver’s License Scan | $70–$165 |
| Complete Medical Record | $500+ |
| Infostealer Malware Subscription | $1,024 |
| DDoS Attack Service (24 Hours) | $45 |
| Corporate Domain Admin Access | Potentially Tens of Thousands |
| Premium Zero-Day Exploit | $10,000–$200,000+ |
What Is the Dark Web?
The dark web is a hidden portion of the internet that cannot be accessed through traditional search engines like Google or Bing. Users typically access it through anonymity-focused browsers such as Tor.
While parts of the dark web support privacy-focused communications and legitimate anonymity needs, it is also widely used for cybercrime, illegal marketplaces, ransomware operations, and data trafficking.
The dark web ecosystem includes underground forums, encrypted messaging channels, ransomware affiliate programs, and illicit marketplaces where stolen information and hacking services are openly traded.
These marketplaces operate similarly to legitimate e-commerce platforms by using escrow systems, vendor ratings, customer reviews, and cryptocurrency payments.
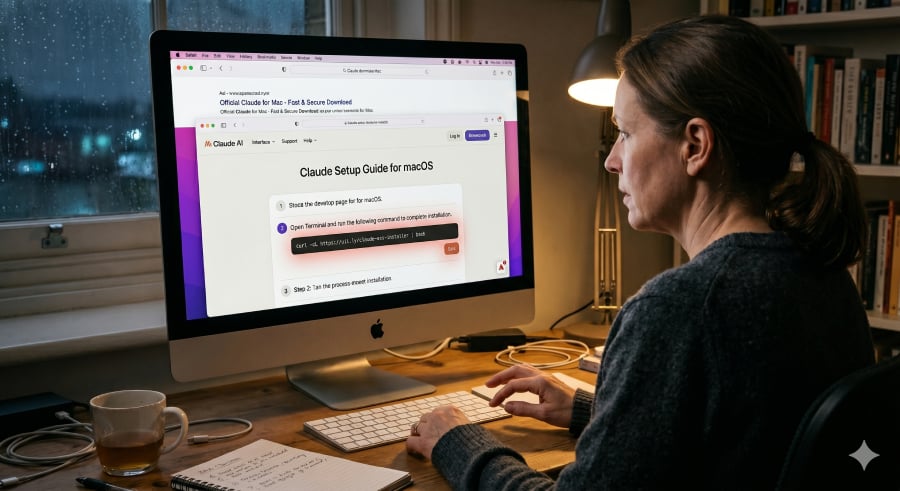
How Easy Is It to Find a Hacker on the Dark Web?
Unfortunately, finding malicious hacking services has become increasingly easy. Threat actors advertise services through underground forums, Telegram channels, marketplace listings,and on clear web channels (e.g., the “normal” internet most people see).
Cybercriminals can purchase many things on the Dark Web, including:
- Distributed denial-of-service (DDoS) attacks
- Phishing kits
- Credential stuffing tools
- Malware subscriptions
- Initial corporate network access
- Social engineering services
- Ransomware kits
- Zero-day exploits
Many platforms now function as “cybercrime-as-a-service” ecosystems, where technical expertise is no longer required.
Similar to legitimate SaaS business models, attackers can subscribe to malware platforms and receive customer support, updates, dashboards, training, and even profit-sharing opportunities.
Common Hacking Services for Hire
DDoS Attacks
DDoS-for-hire services, commonly called “booters” or “stressers,” allow attackers to overwhelm websites or services with traffic. According to 2025 underground pricing data, a 24-hour DDoS attack against an unprotected website can cost as little as $45.
Credential Theft and Phishing
Cybercriminals sell phishing kits that imitate banking portals, cloud services, and login pages. These kits often include hosting instructions, automated credential collection, and evasion features designed to bypass detection.
Malware and Infostealers
Infostealer malware remains one of the most popular tools sold on underground markets. These malware families steal browser credentials, cookies, cryptocurrency wallets, and authentication tokens.
A malware subscription can cost roughly $1,024 annually or less, depending on capabilities and support.
Corporate Network Access
Initial Access Brokers (IABs) specialize in selling verified access to corporate environments. Prices vary significantly based on privilege level:
- Basic VPN access: Hundreds to thousands of dollars
- Local administrator access: Several thousand dollars
- Domain or cloud administrator access: Tens of thousands of dollars
Access that includes multi-factor authentication (MFA) bypass capabilities commands significantly higher prices.
Zero-Day Exploits
Premium zero-day vulnerabilities targeting enterprise software or operating systems can sell for $10,000 to more than $200,000 depending on exclusivity and exploit reliability.
Ransomware-as-a-Service (RaaS)
Ransomware-as-a-Service has transformed cybercrime into a scalable business model. RaaS operators develop ransomware platforms and lease them to affiliates who conduct attacks.
Affiliates typically share a percentage of ransom payments with the developers.
Modern RaaS operations provide:
- Encryption payloads
- Victim negotiation portals
- Cryptocurrency payment infrastructure
- Technical support
- Leak sites for extortion campaigns
This model has significantly increased ransomware activity because attackers no longer need advanced coding/technical skills to launch attacks.
Dark Web Data Prices in August 2025
Stolen data pricing varies based on freshness, quality, rarity, and monetization potential. August 2025 pricing data from Deepstrike shows the following averages:
| US Social Security Number | $1–$6 |
| Full Identity Package (“Fullz”) | $20–$100+ |
| US Credit Card with CVV | $10–$40 |
| High-Limit Credit Card | $110–$120 |
| Online Bank Login | $200–$1,000+ |
| Coinbase Verified Account | $120–$250 |
| Kraken Verified Account | Up to $1,170 |
| Gmail Account | $60–$65 |
| Facebook Account | $45–$50 |
| Driver’s License Scan | $70–$165 |
| Passport Scan | Around $100 |
| Complete Medical Record | $500+ |
| Infostealer Subscription | Around $1,024 |
Medical records remain highly valuable because they support insurance fraud, identity theft, and blackmail operations.
How Dark Web Markets Operate
Dark web markets function much like traditional online marketplaces. Vendors build reputation scores through successful transactions, while buyers leave reviews and ratings. Most transactions rely on cryptocurrency payments such as Bitcoin or Monero.
Law enforcement takedowns can temporarily disrupt operations, but the ecosystem remains resilient. Following major disruptions, vendors often migrate to replacement markets or decentralized platforms like Telegram.
Pricing also fluctuates after major breaches. Freshly stolen data initially commands premium pricing, but costs rapidly decline once markets become saturated with the same compromised information.
Must-read security coverage
How to Protect Yourself
Individuals and organizations can reduce exposure to dark web threats through proactive security measures:
- Use password managers such as Proton Pass or LastPass
- Enable multi-factor authentication wherever possible
- Monitor accounts with services like Have I Been Pwned
- Use identity theft monitoring services
- Monitor financial accounts regularly
- Deploy dark web monitoring tools
- Use reputable VPN services on public networks
- Keep systems and software updated
- Train employees to recognize phishing attempts
Cybercrime marketplaces continue to evolve, making stolen data and hacking services increasingly accessible.
Understanding how these underground economies operate can help individuals and businesses better defend against modern cyber threats.
As cybercriminal operations become more sophisticated and accessible, many organizations leverage zero trust solutions to help reduce attack surfaces and limit unauthorized access.