
New Global Scam Uses Fake Meeting Links to Run PowerShell Malware
A fake meeting invite is all it can take to turn a routine video call into a credential-stealing trap.
Security researchers at Arctic Wolf uncovered a BlueNoroff campaign targeting Web3 and cryptocurrency organizations with deepfake impersonation, typosquatted meeting links, and fileless PowerShell malware. BlueNoroff is a financially motivated subgroup of North Korea’s Lazarus Group, long associated with efforts to steal digital assets from high-value targets.
Researchers identified more than 100 targeted victims in more than 20 countries, with founders and CEOs constituting half of their targets.
Initial stages of an attack
Arctic Wolf reports that to launch its attacks, the group requires three things:
- Advanced social engineering techniques
- AI-generated deepfakes
- Unique fileless PowerShell malware
The attack chain begins with spearphishing, which involves impersonating high-profile individuals, typically in the financial technology or legal industries. Masking behind these deepfaked identities, the hackers try to get their targets on a call using a fake meeting link.
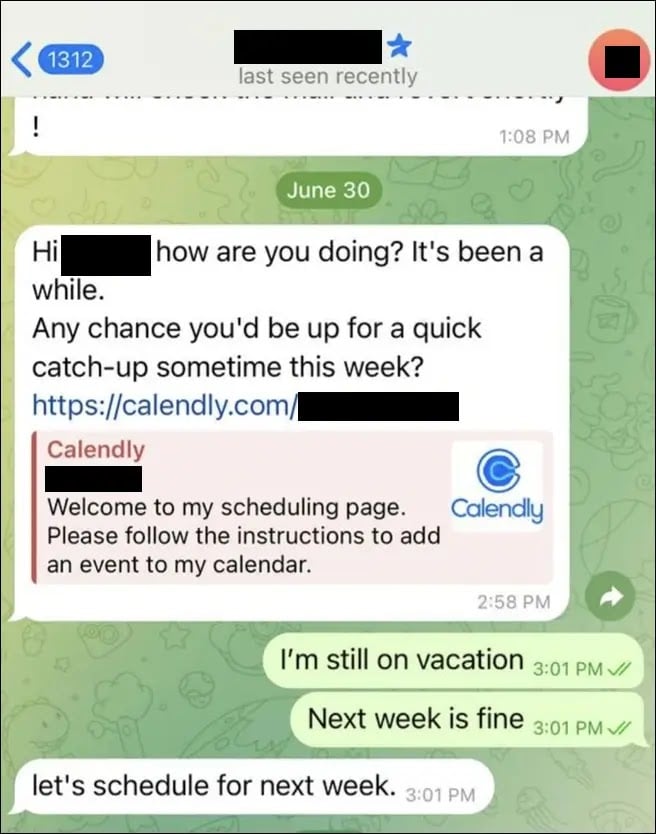
In the observed attack, the victim was sent what looked like a legitimate Calendly link. However, the meeting link in that Calendly invite used a typosquatted domain to redirect recipients to a fake Zoom or Microsoft Teams call.
Once the target joins the call through the malicious call interface, the audio appears to stop working mid-call.
The attacker-controlled call interface will, at this point, display a notification prompting the victim to update their video conferencing software development kit so the audio can continue. This notification is followed by a command disguised as assistance in fixing the problem, instructing the victim to copy and paste it into the terminal.
Doing that triggers script execution, which initiates the download of another payload from the command-and-control (C2) server. While the role of the first script is to establish an entry point, the second payload immediately attempts to establish persistence by living in the system’s live memory rather than in a file. This technique, as Arctic reports, allows it to “evade file-based detection.”
Campaign objectives
To achieve its goal of credential harvesting, after establishing persistence, it enumerates the victim’s device and runs a sequence of exploits, including Telegram sessions and file theft.
A primary target for this stage is Chromium-based browsers. It deploys a payload from its server, which is injected into these Chromium-based browser processes. Doing this allows it to bypass browser-level security checks and exfiltrate data, particularly cryptocurrency wallet keys, login credentials, and browser history.
Aside from credential harvesting, Arctic Wolf also reports that, in a later stage, the malware escalates its privileges in the victim’s system and captures high-resolution screenshots of their desktop.
On top of that, a victim’s report cited by Arctic Wolf reveals that attackers often impersonate their past victims to launch targeted attacks on others.
Advertisement
Targets of the campaign
While the analyzed incident was from a North America-based cryptocurrency firm, the campaign’s demographic and industry-level scope extends beyond cryptocurrency and US-based firms. North America was the hardest-hit region, with targets in the US alone accounting for 41% of the global total.
The table below shows the spread across affected regions.
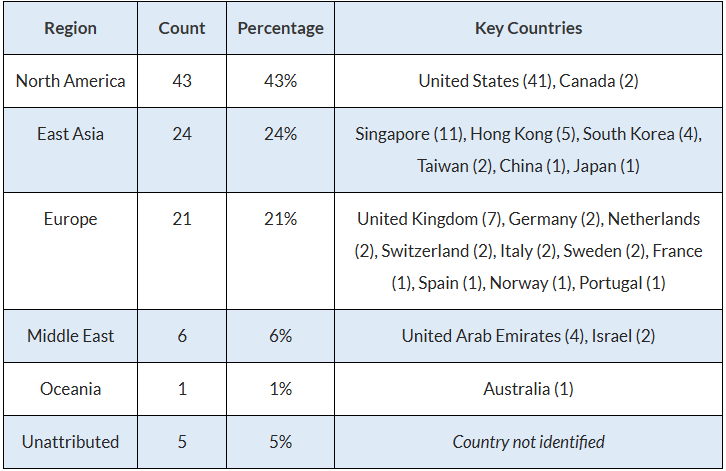
Additionally, 80% of targeted industries are in the finance sector, including blockchain/crypto-based firms, venture capitalists, and investment firms. Others in the minority include artificial intelligence, cybersecurity, media, real estate, and nonprofits.
To stay protected from these kinds of attacks, organizations and individuals must observe preventive, detective, and reactive measures.
- Security awareness training: Phishing and social engineering simulations can help individuals recognize common signs of these attacks.
- Set up Endpoint Detection and Response (EDR) systems: Tune them to monitor for both file-based and fileless activities across systems.
- Implement reputation-based network monitoring: Many C2 servers either have a poor reputation or use newly registered domains. Security teams can block connections to domains that do not match approved criteria.
- Segment critical systems: Crypto assets and sensitive credentials should be isolated from public-facing internet systems whenever possible to reduce exposure to attacks.
- Audit systems and installed extensions regularly: Because fileless malware can persist quietly, regular audits can help detect suspicious processes, extensions, and persistence mechanisms.
Also read: Our 2026 cyberattack roundup tracks major security incidents and software flaws shaping enterprise defenses this year.





