The Instagram API Scraping Crisis: When ‘Public’ Data Becomes a 17.5 Million User Breach
On January 7, 2026, a dataset containing 17.5 million Instagram user records appeared on BreachForums – a notorious dark web marketplace.
Full names. Email addresses. Phone numbers. Partial location data. All structured, formatted, ready to exploit.

The Instagram API Scraping Crisis: When ‘Public’ Data Becomes a 17.5 Million User Breach
On January 7, 2026, a dataset containing 17.5 million Instagram user records appeared on BreachForums – a notorious dark web marketplace.
Full names. Email addresses. Phone numbers. Partial location data. All structured, formatted, ready to exploit.
The hacker posted it for free. No paywall. No restrictions. Just 17.5 million people’s personal information, available to anyone.
Meta’s response? “There was no breach.”
Technically, they’re right. But functionally? 17.5 million users just had their data compromised, and the distinction between “breach” and “API scraping” is meaningless when your information is on the dark web.
After building identity and access management (IAM) systems that had to defend against exactly this type of attack, I can tell you: this is a failure of API security architecture, and it’s happening across every major platform.
Let me break down what actually happened, why Meta’s denial is technically accurate but practically dishonest, and what this reveals about the broken economics of social media data protection.
What Actually Happened
Here’s the timeline:
January 7, 2026: Dataset posted to BreachForums by user “Solonik”
Title: “INSTAGRAM.COM 17M GLOBAL USERS – 2024 API LEAK”
Format: JSON and TXT files, well-structured
Data: 17.5 million records total, 6.2 million with email addresses
Cost: Free (alarming – usually means mass distribution intended)
January 8-9, 2026: Instagram users worldwide report:
Unsolicited password reset emails (legitimate Instagram addresses)
Automated attempts to access accounts
Phishing attempts using leaked data
January 10, 2026: Cybersecurity firms investigate:
Malwarebytes confirms dataset authenticity
Have I Been Pwned adds Instagram to breach database
Multiple security researchers verify sample records
January 11, 2026: Meta’s official response:
“The reports circulating in parts of the media are false. Instagram users’ account data remains safe and secure.”
What Meta ISN’T saying: The data exists, it’s real, and it came from Instagram. Whether you call it a “breach” or “scraping,” the result for users is identical.
What Data Was Exposed
The leaked dataset contains:
Definite for all 17.5M records:
Instagram usernames
Display names
Account IDs
In some cases: partial geolocation data
Additionally for 6.2M records:
Email addresses
Phone numbers (subset)
What was NOT exposed:
Passwords (thankfully)
Direct messages
Private photos/videos
Payment information
Full addresses
Why this still matters:
Even without passwords, this data enables:
1. Targeted phishing
“Hi [Real Name], your Instagram account [Real Username] has been…”
Using real details makes scams convincing
2. SIM swapping attacks
Phone number + name + DOB (from other breaches) = ability to port numbers
Once they have your number, they can bypass 2FA
3. Credential stuffing
Email addresses tested against password databases from other breaches
People reuse passwords; leaked emails help attackers guess which accounts exist
4. Social engineering
Profile information combined with public posts reveals:
Where you live (from location tags)
Who you know (from tagged photos)
What you do (from posts and stories)
When you’re away (from vacation posts)
5. Identity verification bypass
Many services use email + name + phone for “forgot password” flows
This data provides 2 of 3 verification factors
As I’ve written extensively about in my guide to identity and access management, the value of leaked data compounds when combined with other breaches.
Your Instagram data alone is annoying. Combined with AT&T’s leaked SSNs or LinkedIn’s professional data? That’s a complete identity theft toolkit.
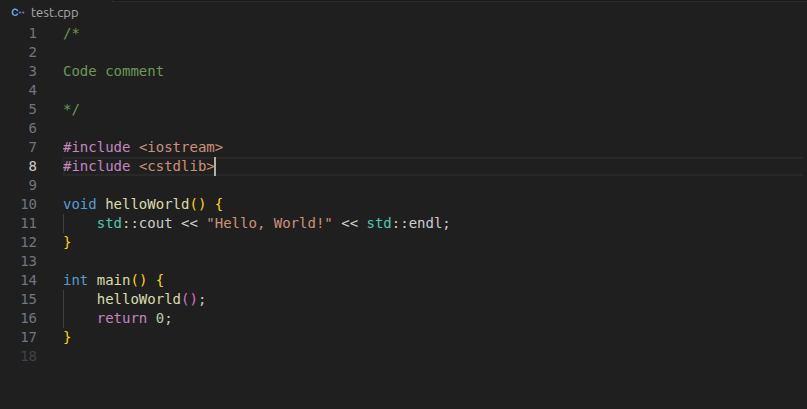
How API Scraping Actually Works
Meta claims “no breach” because their internal systems weren’t hacked. Technically true.
But here’s what actually happened:
The API Vulnerability
Instagram has public APIs that let applications:
Fetch user profile information
Display public posts
Show follower counts
Access basic account data
These APIs are necessary for:
Third-party apps integrating with Instagram
Business analytics tools
Content management platforms
Marketing automation
The problem: APIs have rate limits to prevent abuse. But those limits can be bypassed through:
1. Distributed scraping
Use thousands of different IP addresses
Each makes “acceptable” number of requests
Collectively: millions of requests
2. Account rotation
Create thousands of fake Instagram accounts
Each account gets its own rate limit
Rotate through accounts to avoid detection
3. Exploiting legitimate access
Compromise business accounts with API access
Use their elevated permissions
Harder to detect because traffic looks “normal”
4. API endpoint vulnerabilities
Some endpoints expose more data than intended
Unpatched or legacy endpoints with weaker protections
Public endpoints that should require authentication
According to Meta, attackers likely exploited a 2024 API vulnerability that:
Allowed access to profile data without proper authentication
Had insufficient rate limiting
Wasn’t properly secured before discovery
Meta fixed the vulnerability (eventually). But not before attackers scraped 17.5 million records.
Why “It’s Public Data” Isn’t a Valid Defense
Meta’s implicit argument: “This data is publicly visible on profiles anyway, so it’s not really a breach.”
Here’s why that’s nonsense:
1. Aggregation changes everything
Visiting one profile manually = acceptableProgrammatically collecting 17.5 million = surveillance
The scale transforms “public” into “weaponizable.”
2. Consent matters
Users consent to profiles being viewed by humans.Users don’t consent to mass automated scraping and dark web distribution.
That’s like saying “you walked outside today, so you consent to being followed everywhere by a private investigator.”
3. Platform responsibility
Instagram built APIs. Instagram profits from those APIs (business integrations).Instagram has responsibility to prevent API abuse.
Claiming “it’s public data” abdicates that responsibility.
4. Context collapse
Information appropriate in one context (Instagram profile) becomes dangerous in another (dark web marketplace).
The same data that’s fine for followers to see becomes a security risk when aggregated and distributed to criminals.
While building and scaling CIAM Platform, I built API security controls specifically to prevent this type of abuse. Rate limiting, authentication requirements, anomaly detection, IP reputation scoring – these aren’t optional for platforms handling millions of users.
Meta’s position: “No breach occurred. Our systems weren’t compromised. This is scraped public data.”
User reality: “My personal information is on the dark web. I’m getting phishing attempts. I didn’t authorize mass collection of my data.”
Both can be technically true. But one matters more than the other.
The Legal Gray Area
Under GDPR (Europe):
Users have right to know when data is collected
Automated scraping without consent may violate regulations
Meta could face fines for inadequate API protection
Under CCPA (California):
Users have right to know what data is collected and how it’s used
“Public” doesn’t mean “consent to mass scraping and redistribution”
Unclear if API scraping triggers disclosure requirements
Under existing breach notification laws:
Most define “breach” as unauthorized access to systems
API scraping often doesn’t qualify
But users still get notified if data is compromised in ways that create risk
The gap: Laws written before mass API scraping became widespread don’t adequately address this attack vector.
Until regulations catch up, platforms can claim “no breach” while users suffer consequences identical to actual breaches.
Why This Keeps Happening
Instagram isn’t unique. API scraping affects:
LinkedIn: 700 million users scraped (2021)Facebook: Hundreds of millions across multiple incidentsTwitter/X: Multiple scraping incidentsTikTok: Various scraping operationsClubhouse: 1.3 million users (2021)
Why platforms don’t fix it:
1. APIs Are Revenue Sources
Platforms make money from:
Business API access (marketing tools, analytics platforms)
Developer ecosystem (third-party apps drive engagement)
Enterprise integrations (CRM systems, customer service tools)
Locking down APIs = less revenue, smaller ecosystem.
2. Detection Is Hard
Legitimate heavy usage vs. malicious scraping looks similar:
Marketing tools make millions of API calls (legitimate)
Business analytics platforms scrape public profiles (legitimate)
Attackers using same patterns (malicious but indistinguishable)
Aggressive rate limiting breaks legitimate use cases. Weak rate limiting enables abuse.
Finding the balance is difficult at scale.
3. Economics Don’t Justify Investment
Cost of preventing scraping:
Advanced bot detection: $$$
Manual review of suspicious patterns: $$
Machine learning anomaly detection: $$$
Dedicated API security team: $$$$
Cost of scraping incident to Meta:
User trust damage: Hard to quantify
Regulatory fines: Maybe, but historically small
Lawsuit settlements: Usually minimal
User churn: Negligible (where else will they go?)
The math: Investing millions to prevent scraping isn’t economically justified when consequences are minimal.
Until regulators impose meaningful penalties or users actually leave platforms over this, the economics favor weak protection.
4. Privacy Isn’t the Business Model
Social media platforms make money by:
Showing ads (requires user data and engagement)
Selling data insights to advertisers
Keeping users on platform as long as possible
Privacy is antithetical to the business model.
More data collection = better targeting = more revenue.
“Protecting” data too aggressively reduces the platform’s own ability to monetize it.
This creates perverse incentives where platforms:
Collect maximum data themselves (for revenue)
Provide weak protection against third-party collection (doesn’t affect revenue)
Claim to care about privacy (marketing)
As I’ve written about extensively regarding data privacy for enterprises, when privacy conflicts with profit, profit usually wins.
What Users Should Do Right Now
If you use Instagram (or any social media), here’s your action plan:
Immediate Actions
1. Check if you’re affected
Visit: haveibeenpwned.comEnter your email addressLook for “Instagram” in the breach list
If you’re affected, assume attackers have:
Your name
Your username
Your email address
Possibly your phone number
2. Enable two-factor authentication (2FA)
Critical: Use authenticator app, NOT SMS
Instagram → Settings → Security → Two-Factor Authentication
Preferred: Authenticator apps (Google Authenticator, Authy, 1Password)
Backup: SMS (better than nothing, but vulnerable to SIM swapping)
Best: Hardware keys (YubiKey, Titan)
Why not SMS? Because this leak included phone numbers. SIM swapping attacks use your leaked phone number to port it to the attacker’s device.
3. Review recent login activity
Instagram → Settings → Security → Login Activity
Look for:
Unknown devices
Suspicious locations
Unexpected login times
Revoke access for anything you don’t recognize.
4. Change your password (if you reuse it)
If you use the same password on Instagram and other services:
Change it immediately
Use unique passwords per service
Use a password manager (1Password, Bitwarden, LastPass)
5. Watch for phishing
Expect:
Emails claiming “urgent Instagram security issue”
Messages with “verify your account” links
Requests to confirm personal information
Red flags:
Urgency (“act now or account deleted”)
Suspicious links (instagram-verify-account-2026.sketchy.com)
Requests for password or 2FA code
Verify first: Don’t click links in emails. Go directly to instagram.com and check notifications there.
Ongoing Protection
6. Audit what your profile reveals
Review your Instagram profile as a stranger would see it:
Bio information (do you need your email/location listed?)
Public posts (what do they reveal about you?)
Tagged locations (do these show your home/work?)
Tagged people (do these reveal relationships?)
Make private anything you wouldn’t want criminals to have.
7. Limit what’s public
Settings → Privacy → Account Privacy → Private Account
Tradeoffs:
Pro: Only approved followers see your content
Con: Less discoverability, smaller audience
For personal accounts (not business): strongly consider going private.
8. Review connected apps
Settings → Security → Apps and Websites
Third-party apps with Instagram access:
Remove any you don’t actively use
Check permissions for ones you keep
Be suspicious of apps requesting excessive access
Many “Instagram analytics” tools are data collection fronts.
9. Monitor your email for spam
If your email was in the leak, expect:
Increased spam
Targeted phishing (using your real name/username)
Account takeover attempts on other services
Use spam filters aggressively. Report phishing to your email provider.
10. Consider email aliases
For future social media accounts:
Use unique email addresses per service (Gmail supports aliases: [email protected])
Makes it easier to identify which service leaked your data
Allows you to shut down compromised addresses without affecting others
As someone who built identity systems handling billions of authentications, here’s what Meta should implement:
1. Proper API Security Architecture
Rate limiting that actually works:
Per-user limits (not just per-IP)
Per-endpoint limits (different endpoints have different sensitivity)
Per-token limits (API keys have consumption caps)
Behavioral analysis (unusual patterns trigger blocks)
Authentication requirements:
No unauthenticated access to user data APIs
OAuth for third-party applications
Short-lived tokens (reduce damage if compromised)
Granular permissions (apps only get what they need)
Anomaly detection:
Machine learning models detecting scraping patterns
Geographic anomalies (same account from 100 countries simultaneously)
Volume anomalies (sudden spike in requests)
Time-series analysis (patterns inconsistent with human behavior)
I implemented all of this for our CIAM platform. It’s not theoretical. It’s achievable.
2. Transparency When Scraping Occurs
Stop claiming “no breach” when:
User data ends up on dark web
Resulted from inadequate security
Users face identical risks to traditional breaches
Instead:
Acknowledge the incident
Explain what happened
Detail what data was exposed
Notify affected users
Describe protective measures taken
Honesty builds trust. “No breach” technicalities destroy it.
3. User Control Over Data Visibility
Granular privacy controls:
Choose what’s visible via API (vs. what’s visible on web)
Opt out of all API access (sacrificing integrations for privacy)
Rate limits on how often your profile can be accessed
Alerts when profile accessed unusually frequently
Default to privacy:
New accounts start private
API access requires explicit opt-in
Business accounts have different defaults (they want visibility)
4. Punish Abusers
Legal action against:
Platforms facilitating scraping
Services built on scraped data
Individuals operating scraping operations
Make examples:
High-profile lawsuits
Public statements about enforcement
Damage awards that actually hurt
Right now, scraping is profitable and low-risk. Change the economics.
5. Advocate for Better Regulations
Platform responsibilities:
Clear liability for inadequate API protection
Mandatory disclosure when scraping reaches certain scale
Penalties that actually matter (% of revenue, not fixed fines)
User rights:
Right to opt out of API access entirely
Right to notification when data is accessed at scale
Right to sue for damages when protections fail
Meta lobbies against these regulations. They should lobby for them if they actually care about user privacy.
The Bigger Picture: API Security Is Broken
Instagram’s 17.5 million user scraping isn’t isolated. It’s systemic failure across the entire social media industry.
The pattern:
Platform builds APIs to enable ecosystem
APIs designed for legitimate use (marketing tools, analytics)
Attackers abuse those same APIs at scale
Platform claims “no breach” because systems weren’t hacked
Users suffer consequences identical to traditional breaches
Platform faces minimal consequences
Pattern repeats
Until something changes:
Economics (make scraping unprofitable through enforcement)
Regulations (mandatory protections and disclosures)
User behavior (mass exodus from platforms with weak protection)
…this will keep happening.
At GrackerAI, when we built our AI-powered marketing platform, we had to make security architecture decisions about API access from day one. Not as an afterthought. Not as a “nice to have.” As foundational infrastructure.
That’s what platforms handling hundreds of millions of users should do. But economic incentives push them toward “move fast, break things” – even when “things” include user privacy.
The Bottom Line
17.5 million Instagram users just learned the hard way: “public” data on social media isn’t safe from mass collection and exploitation.
Meta’s “no breach” defense is technically accurate but practically meaningless. Your data is on the dark web. Criminals have it. The method of theft (API scraping vs. system hack) doesn’t change the risk you face.
For users:
Enable 2FA (authenticator app, not SMS)
Make your account private if possible
Audit what your profile reveals
Assume anything public can and will be scraped
Monitor for phishing and account takeover attempts
For platforms:
API security isn’t optional at scale
“Public data” doesn’t absolve responsibility for protection
Transparency beats technical denials
Users deserve control and notification
For regulators:
Current breach definitions don’t cover API scraping
Platforms need liability for inadequate API protection
Users need rights around mass data collection
Penalties must actually change behavior
The Instagram incident shows what happens when platforms prioritize ecosystem and revenue over user data protection.
Until the economics change – through regulation, enforcement, or user exodus – expect more “not a breach” breaches where millions of users’ data ends up on the dark web while platforms claim everything is fine.
It’s not fine. And users deserve better.
Key Takeaways
17.5M Instagram user records leaked via API scraping (January 2026)
Data includes names, usernames, emails (6.2M), phone numbers, partial locations
Meta claims “no breach” but data is on dark web, users face identical risks
API scraping exploited 2024 vulnerability with inadequate rate limiting
Enable 2FA with authenticator app (NOT SMS), make account private, audit profile
“Public” data aggregated at scale becomes dangerous surveillance tool
Instagram/Meta should: fix API security, be transparent, give users control
Systemic problem across social media: APIs designed for ecosystem enable abuse
Regulations needed: platforms liable for API protection failures, mandatory disclosures
Building platforms that handle user data? Learn from these failures in my Customer Identity Hub, covering CIAM best practices, API security, and data privacy architecture that actually protects users.
*** This is a Security Bloggers Network syndicated blog from Deepak Gupta | AI & Cybersecurity Innovation Leader | Founder's Journey from Code to Scale authored by Deepak Gupta – Tech Entrepreneur, Cybersecurity Author. Read the original post at: https://guptadeepak.com/the-instagram-api-scraping-crisis-when-public-data-becomes-a-17-5-million-user-breach/