The Future of CIAM: Why Legacy Identity Systems Are Dead (And What Replaces Them)
The post The Future of CIAM: Why Legacy Identity Systems Are Dead (And What Replaces Them) appeared first on Deepak Gupta | AI & Cybersecurity Innovation Leader | Founder’s Journey from Code to Scale.

The Future of CIAM: Why Legacy Identity Systems Are Dead (And What Replaces Them)
The post The Future of CIAM: Why Legacy Identity Systems Are Dead (And What Replaces Them) appeared first on Deepak Gupta | AI & Cybersecurity Innovation Leader | Founder’s Journey from Code to Scale.
The CIAM infrastructure powering most digital products today was architected for a world that no longer exists.
It assumed humans were the only actors requiring authentication. It assumed passwords could be secured through complexity requirements and MFA. It assumed quantum computers capable of breaking RSA-2048 were decades away. It assumed attackers were working at human speed.
Every one of those assumptions is now demonstrably false.
After building and scaling a CIAM platform to serve over a billion users, I watched the authentication landscape transform faster in the past 18 months than it did in the previous decade combined. The changes aren’t incremental improvements to existing patterns. They represent a fundamental break from how identity management has worked since we first started building digital products.
The numbers tell a stark story about legacy CIAM’s end game.
The CIAM market is projected to surge from $12.6 billion in 2026 to $40.2 billion by 2036, but that growth masks a massive platform migration happening underneath. 87% of enterprises are deploying passkeys in 2026, rendering password-based CIAM infrastructure obsolete. By January 1, 2027, all new US National Security System acquisitions must be compliant with CNSA 2.0, the NSA’s post-quantum algorithm suite, forcing authentication protocol rewrites across government and regulated industries.
And AI is accelerating the timeline for all of it.
CrowdStrike’s 2026 Global Threat Report documents a 65% faster average eCrime breakout time and 89% year-over-year surge in AI-augmented cyberattacks. When adversaries move faster than human investigation cycles, authentication systems built for manual security review simply cannot keep up.
This article breaks down exactly what’s coming for CIAM, why legacy platforms can’t adapt fast enough, and what architecture patterns actually work when AI agents outnumber human users and attacks happen at machine speed.
The Collapse of Legacy CIAM: Why AI Broke Authentication at Scale
Legacy CIAM was never designed for the threat environment we’re operating in now.
Password-based authentication assumes attackers need to brute-force credentials one at a time. AI-powered attack tools now automatically identify legacy systems on networks and match them against vulnerability databases in real-time. What took skilled hackers days of reconnaissance happens in minutes.
Traditional MFA assumes phishing attacks are human-recognizable. Deepfakes and AI-generated social engineering have eliminated the tells that security awareness training relied on. When synthetic voices sound indistinguishable from executives and AI can generate convincing context in real-time video calls, traditional biometric markers like static facial scans and voiceprints become unreliable for high-stakes authentication.
Session-based security assumes human behavior patterns. AI agents don’t browse like humans. They don’t take breaks. They execute hundreds of API calls per second across multiple services simultaneously. Legacy CIAM’s rate limiting and behavioral analytics trigger false positives constantly or get tuned down so low they miss actual attacks.
The breaking point comes when you try to layer AI functionality onto CIAM platforms designed before machine identities mattered.
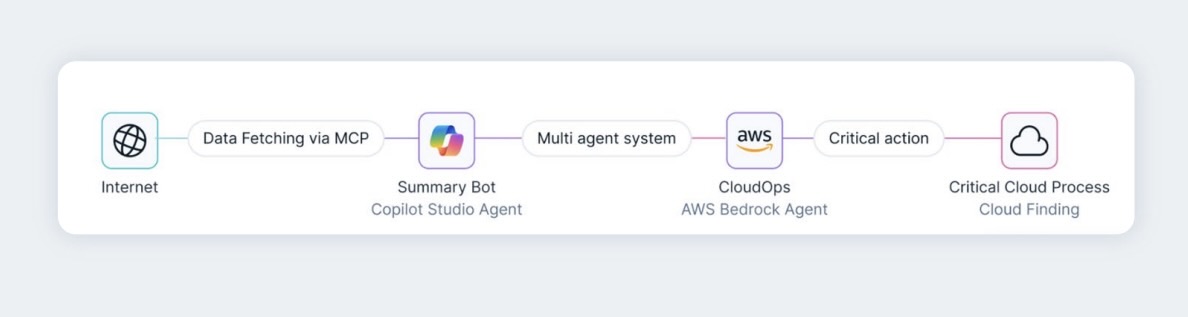
AI agents are what we call composite identities – they combine the blast radius of service accounts with the unpredictability of human decision-making at machine speed. Register an AI agent in traditional IAM, and you’re immediately in uncharted territory. It needs credentials but shouldn’t store them statically. It acts on behalf of humans but makes independent decisions. It accesses resources across trust boundaries but doesn’t fit role-based access control models.
Legacy CIAM platforms handle this by treating agents as service accounts with expanded permissions. That approach creates exactly the security nightmare you’d expect: agents with standing access to everything they might theoretically need, credential sprawl as teams create new API keys for each agent variation, and zero runtime enforcement of what agents actually do versus what they were authorized to do.
The vulnerability window is massive and growing.
CVE-2025-53773 revealed that hidden prompt injection in pull request descriptions enabled remote code execution with GitHub Copilot, with a CVSS score of 9.6. When your authentication system can’t differentiate between a legitimate AI agent acting on delegated authority and a compromised agent executing malicious instructions, you don’t have identity management. You have identity theater.
The Passkey Inflection Point: When Passwordless Became Mandatory
March 2026 marked the moment passwordless authentication stopped being a nice-to-have and became baseline security.
Microsoft began auto-enabling passkey profiles across all Microsoft Entra ID tenants, forcing the largest enterprise migration to passwordless authentication in history. Organizations that haven’t configured custom settings are having passkey defaults applied automatically, affecting millions of enterprise users.
This wasn’t Microsoft acting unilaterally. It was Microsoft responding to regulatory and market pressure that made passwords indefensible.
The UAE Central Bank issued a directive requiring all licensed financial institutions to eliminate SMS and email OTPs by March 2026. NIST SP 800-63-4 now requires phishing-resistant MFA for AAL2 compliance, and explicitly recognizes synced passkeys as meeting that requirement. Passwordless authentication is becoming the enterprise baseline for workforce access across many enterprises by the end of 2026.
The adoption numbers reflect this shift.
69% of consumers now have at least one passkey, up from 39% just two years ago. But consumer adoption was never the bottleneck. Enterprise deployment was. Enterprises managing passwordless deployments report an average annual savings of $594,000 from eliminated authentication overhead, with support ticket volumes falling between 60% and 80% post-deployment.
When the ROI case closes within 12-18 months and regulatory mandates remove the option to stay on passwords, migration becomes inevitable.
The authentication pattern that emerges looks nothing like traditional CIAM.
Device-bound passkeys stored in secure enclaves replace passwords and SMS codes. Passkeys use public-key cryptography to prove identity without ever sending sensitive information across the network. The private key never leaves the device. Authentication happens through cryptographic challenge-response, not shared secrets.
This eliminates entire classes of attacks. No phishing-vulnerable credentials to steal. No password databases to breach. No SMS intercepts to execute. The attack surface shrinks to compromising the device itself, which brings its own challenges but represents a fundamentally more defensible position than password-based authentication ever offered.
For CIAM platforms, passkey support is no longer optional.
At 500k monthly active users, passkey adoption cutting SMS OTP costs 60-90% translates to $50k-100k or more in annual savings. But cost savings matter less than the security baseline. By mid-2026, SMS OTP was officially on its way out across financial services, healthcare, and government systems.
CIAM platforms that treat passkeys as an add-on feature rather than the primary authentication method are already obsolete. The migration timeline is compressed, and legacy password infrastructure is being deprecated faster than most engineering teams planned for.
Post-Quantum Authentication: The 2027 Deadline No One Is Ready For
While everyone focused on passkeys, a quieter but more fundamental shift began: the migration to post-quantum cryptography.
NIST finalized the first three post-quantum cryptographic standards on August 14, 2024 – the first approved alternatives to RSA and ECC in authentication and encryption. The compliance timeline is unforgiving. By January 1, 2027, all new US National Security System acquisitions must be compliant with CNSA 2.0, with full mandatory compliance across most NSS system types required by 2033.
The threat driving this timeline is “harvest now, decrypt later” attacks.
Intelligence agencies in multiple countries are actively warning that adversaries are already exfiltrating encrypted data at scale, banking on quantum decryption capability arriving within a decade. For any data with confidentiality requirements extending beyond approximately 2032-2035, protection decisions must be made now.
Post-quantum migration for authentication is more complex than encryption upgrades.
Migrating to post-quantum authentication requires disabling quantum-vulnerable cryptography to prevent downgrade attacks, and once done, all previously exposed secrets including passwords and access tokens require rotation. This isn’t a library update. It’s a protocol-level rewrite of how authentication happens.
Cloudflare plans to add support for post-quantum authentication using ML-DSA to origin connections by mid-2026, with post-quantum connections from end users to Cloudflare using Merkle Tree Certificates by mid-2027. The migration path exists, but implementation timelines stretch years, not months.
For CIAM platforms, this creates an architectural fork point.
Platforms architected around RSA and ECC for all cryptographic operations face complete rewrites. Platforms designed with cryptographic agility, where algorithms can be swapped without application-layer changes, have clearer migration paths. Most legacy CIAM falls into the first category.
The enterprises operating these platforms face a choice: begin post-quantum migration now while quantum computers are still theoretical, or wait until Q-Day approaches and face emergency migrations under pressure.
Given regulatory deadlines and the harvest-now threat, waiting is not actually an option. The migration timeline just hasn’t hit most organizations’ radar yet.
AI-Native Authentication: When Agents Outnumber Humans
The authentication model that dominated CIAM for two decades – humans logging into applications – is being replaced by a model where AI agents execute most interactions.
Gartner highlights that by 2026, 30% of enterprises will rely on AI agents that act independently, triggering authentication and authorization decisions at machine scale. These aren’t simple service accounts. AI agents reason, delegate, and act across domains and trust zones, which means legacy non-human identity models simply don’t apply.
The authentication requirements are fundamentally different.
Google Cloud introduced Agent Identities to enable agents to operate autonomously with specific authentication flows and scoped human delegation. This represents a new identity primitive: not quite human, not quite machine, but something that blends characteristics of both.
AI-native authentication requires:
Runtime enforcement, not configuration-time permission. Static least privilege assumes predictable behavior – agents break that assumption because they reason, chain tools, and drift from what they were originally authorized to do. Permissions must be validated at every action, not just at provisioning.
Just-in-time identity provisioning. Maverics provisions agent identities on demand with attributes like TTL, purpose, risk, and delegation context attached – when the task is done, the identity is retired. No orphaned credentials, no permission sprawl, no standing access to resources agents don’t currently need.
Subject-actor trust binding. OAuth subject-actor delegation ensures that when an AI agent acts on behalf of a human, that relationship is cryptographically verifiable and scoped to specific permissions. The human grants fine-grained authority, and the system enforces those boundaries in real-time.
Behavioral analytics designed for non-human patterns. Modern IAM systems analyze keystroke dynamics and mouse movements to verify identity – but agents don’t have those signals. Authentication for agents requires analyzing API call patterns, resource access sequences, and decision-making logic to detect anomalies.
95% of organizations cite identity concerns around AI agents, yet most are trying to force agents into human-designed IAM systems rather than building agent-native identity infrastructure.
The platforms getting this right treat AI agents as first-class identity primitives from day one. Google’s Agent Gateway enables policy enforcement for all agent-to-agent and agent-to-tool connections, understanding agent protocols like MCP and Agent2Agent to inspect and secure every interaction.
This is what AI-native CIAM looks like. Not humans logging into applications with agents as background processes, but agents as primary actors with humans providing delegated authority and governance oversight.
Liveness Detection: When Deepfakes Make Biometrics Unreliable
The rise of convincing deepfakes broke an assumption biometric authentication relied on: that you can verify identity by matching against stored biological markers.
The rise of convincing deepfakes renders traditional biometric markers like static facial scans and voiceprints unreliable for high-stakes authentication. When synthetic faces and voices are indistinguishable from real ones, matching against a stored template proves nothing about whether a live human is present.
The authentication industry’s response is liveness detection.
Instead of asking “does this face match the stored image,” systems now ask “is this a live person, not a replay attack or synthetic generation.” Multi-frame facial analysis tracks subtle muscle movements, and voice authentication analyzes unique vocal cord patterns to distinguish between live humans and AI-generated imposters.
Rising deepfakes and non-human identities necessitate advanced verification including liveness detection across financial services, government systems, and any high-value authentication scenario.
For CIAM platforms, this introduces a new verification layer.
Traditional authentication asked: Who are you? (Something you know, have, or are) AI-era authentication asks: Who are you, and are you actually present right now as a live human?
Microsoft Entra Verified ID combines government-issued ID validation with biometric matching for both onboarding and account recovery, ensuring no bad actors or AI impersonators gain access.
This verification intensity only makes sense for high-stakes scenarios. You don’t need liveness detection for logging into a social media account. But for accessing financial systems, medical records, or any scenario where impersonation creates material harm, liveness verification becomes mandatory.
The CIAM platforms adapting fastest are those that treat liveness as a continuous verification requirement, not a one-time check. CIAM will integrate with emerging technologies like AI and machine learning to deliver more personalized and context-aware customer experiences, including adaptive liveness checks triggered by risk signals rather than applied universally.
The Machine Identity Explosion: Managing Billions of Non-Human Identities
While enterprises worried about managing thousands of employee identities, machine identities exploded into the millions without anyone noticing.
Every microservice, API, and container in a cloud-native environment has its own identity – managing the lifecycle of these ephemeral, non-human identities requires specialized tools that can handle millions of credentials at scale.
The ratio shift is dramatic.
Traditional IAM was built for enterprises with 10,000 employees and maybe 100,000 customers. Modern digital platforms serve millions of customers, but that’s still manageable with existing CIAM architecture.
But those same platforms now run hundreds of microservices, each with multiple API keys, service accounts, and machine identities. Add AI agents that spawn ephemeral identities for specific tasks, and you’re managing machine identities at scales CIAM was never designed for.
BeyondTrust’s Identity Security Insights data finds enterprise AI agents growing 466.7% year over year, and each agent requires its own identity management, credential rotation, and access governance.
The challenge isn’t just volume. It’s velocity.
Machine identities are ephemeral. A container spins up, authenticates to necessary services, executes its task, and terminates – all in seconds. Traditional identity lifecycle management built for humans who stay employed for years doesn’t map to identities that exist for minutes.
Cloud Infrastructure Entitlement Management (CIEM) and machine identity management tools are required to handle millions of credentials at scale, but these are separate platforms from human-facing CIAM. The architecture is fragmenting into specialized identity management for different identity types rather than one unified system.
For CIAM vendors, the question is whether to expand into machine identity management or stay focused on human and customer identities. Most are choosing specialization, which means enterprises are running multiple identity platforms in parallel.
This creates integration challenges and gaps in policy enforcement, but it’s also more practical than trying to force machine-scale identity management into platforms optimized for human patterns.
What Actually Replaces Legacy CIAM: The Architecture Patterns That Work
After watching the identity landscape transform, a clearer picture emerges of what next-generation CIAM actually looks like.
Passkeys as the primary authentication primitive, not passwords with passkeys as an alternative. The platform assumes phishing-resistant authentication by default. SMS and password fallbacks exist only for legacy migrations, not as permanent options.
Post-quantum ready cryptography from day one. Platforms architected with algorithm agility so migration to ML-DSA and other post-quantum algorithms doesn’t require application rewrites. NIST is standardizing more post-quantum algorithms through round 4 competitions and the signatures onramp, and platforms need to absorb these without breaking existing integrations.
AI agent identity as a first-class primitive. OAuth 2.1, Client ID Metadata Documents, and tool-level scopes to govern AI agents alongside human users are baseline requirements, not advanced features. Agent authentication isn’t bolted onto human IAM patterns – it’s designed natively for machine-speed decision-making and runtime enforcement.
Continuous liveness and behavioral verification. Zero Trust evolves into continuous verification – instead of one-time authentication at the network perimeter, continuous verification of identity, device health, and behavioral patterns throughout the session. Risk-based authentication that adjusts friction dynamically based on context rather than applying uniform policies.
Decentralized identity support for selective disclosure. Self-sovereign identity and decentralized identifiers move beyond the crypto community into enterprise authentication. Users prove attributes without revealing unnecessary personal data, and verification happens without centralized identity databases that become breach targets.
Identity fabric architecture for multi-platform management. The identity fabric approach creates a unified, flexible IAM architecture that manages identity across disparate systems. Rather than trying to replace every legacy system immediately, the fabric orchestrates authentication and authorization across heterogeneous environments.
This isn’t one platform. It’s an architectural pattern implemented across specialized systems that interoperate through standard protocols.
The enterprises succeeding at this transition aren’t trying to migrate everything to a single next-gen CIAM overnight. They’re building the fabric layer, migrating high-value use cases to passkeys first, ensuring post-quantum readiness in new implementations, and designing AI agent identity governance separately from human authentication.
The Timeline: When Legacy CIAM Actually Becomes Unviable
The question isn’t whether legacy CIAM needs replacement. It’s how fast the migration must happen.
2026: Passkey adoption reaches critical mass. 87% of companies deploying passkeys means password-only CIAM is competitively unviable. Enterprises still using legacy authentication face customer friction, higher support costs, and security incidents that passkey-enabled competitors avoid.
2027: Post-quantum compliance deadlines hit. CNSA 2.0 compliance required for new National Security System acquisitions. Government contractors and regulated industries must demonstrate post-quantum migration plans or lose business opportunities.
2028-2030: AI agent identities outnumber human identities. 30% of enterprises rely on AI agents that act independently by 2026, and that percentage climbs rapidly. CIAM platforms without agent-native identity management can’t support AI-first application architectures.
Beyond 2030: Passwords become historical artifacts. Passwords relegated to legacy fallback status rather than primary authentication methods. The platforms still offering password-based authentication are maintaining compatibility with systems that should have been modernized years earlier.
The migration timeline compresses faster than most organizations expect because these changes compound.
Passkey deployment forces protocol updates. Protocol updates create opportunities to add post-quantum readiness. Post-quantum readiness enables cleaner agent identity architectures. Each step makes the next migration easier – or makes staying on legacy systems harder.
The Strategic Decision: Modernize or Migrate
After building and scaling CIAM infrastructure to massive scale, I can tell you the hardest decision isn’t technical. It’s strategic.
Do you modernize your existing CIAM platform with passkey support, post-quantum readiness, and agent identity capabilities? Or do you accept that the architecture is fundamentally wrong for where identity management is heading and migrate to next-generation platforms?
The answer depends on your starting point.
If you built CIAM on modern protocols, with cryptographic agility and identity primitives designed for extensibility, modernization paths exist. You’re adding features to an architecture that can support them.
If your CIAM is built on password-centric authentication, monolithic identity stores, and protocols designed before machine identities mattered, modernization is rebuilding the platform while it’s running in production. That’s the highest-risk engineering project a team can undertake.
Re-platforming CIAM when you outgrow a solution is one of the most disruptive engineering projects a team can undertake. But running legacy authentication infrastructure when attackers operate at AI speed is arguably more disruptive.
The platforms getting this right aren’t waiting for forced migrations. They’re treating authentication modernization as continuous improvement, migrating use cases progressively, and building toward post-quantum and AI-native patterns before regulatory or security incidents force emergency changes.
For anyone building or operating CIAM infrastructure in 2026, the future is clear. Passkeys replace passwords. Post-quantum crypto replaces RSA and ECC. AI agents become primary identity types. Liveness detection becomes mandatory for high-stakes authentication.
The only question is whether you’re leading that transition or reacting to it.
Deepak Gupta is a serial entrepreneur and cybersecurity expert who co-founded and scaled a CIAM platform to serve over 1 billion users globally. He currently leads GrackerAI, an AI-powered GEO platform helping B2B SaaS and cybersecurity companies achieve visibility in LLM search engines. He writes about AI, cybersecurity, and B2B growth at guptadeepak.com.
For more insights on identity management and authentication, explore our guides on passkeys and passwordless authentication, post-quantum cryptography for authentication, and our cybersecurity resources at guptadeepak.com.
*** This is a Security Bloggers Network syndicated blog from Deepak Gupta | AI & Cybersecurity Innovation Leader | Founder's Journey from Code to Scale authored by Deepak Gupta – Tech Entrepreneur, Cybersecurity Author. Read the original post at: https://guptadeepak.com/the-future-of-ciam-why-legacy-identity-systems-are-dead-and-what-replaces-them/


![[un]prompted 2026 – Total Recon: How We Discovered 1000s Of Open Agents In The Wild](https://securityboulevard.com/wp-content/uploads/2018/01/TwitterLogo-002.jpg)