The
stakes
could
not
be
higher
for
cyber
defenders.
With
the
vast
amounts
of
sensitive
information,
intellectual
property,
and
financial
data
at
risk,
the
consequences
of
a
data
breach
can
be
devastating.
According
to
a
report
released
by
Ponemon
institute,
the
cost
of
data
breaches
has
reached
an
all-time
high,
averaging
$4.35
million
in
2022.
Vulnerabilities
in
web
applications
are
often
the
primary
gateway
for
attackers.
According
to
a
World
Economic
Forum
report,
just
one
week
after
discovering
a
critical
security
flaw
in
a
widely
used
software
library
(Log4j),
more
than
100
attempts
at
exploiting
the
vulnerability
were
detected
every
minute.
This
illustrates
how
quickly
malicious
actors
can
take
advantage
of
vulnerabilities,
highlighting
the
urgency
of
regularly
assessing
and
monitoring
your
system
for
any
vulnerabilities
or
weak
points.
The
complexity
of
addressing
security
challenges
in
today’s
digital
world
is
further
compounded
by
the
rising
use
of
open-source
components,
accelerating
software
delivery
cycles,
and
rapidly
expanding
attack
surface.
One
key
way
organizations
can
protect
themselves
from
cyber
threats
is
by
conducting
penetration
tests.
Pen
testing
is
a
proactive
security
measure
that
involves
simulating
real-life
cyber-attacks
on
networks,
servers,
applications,
and
other
systems
to
discover
and
address
any
potential
weaknesses
or
vulnerabilities
before
they
can
be
exploited.
Which
type
of
pen
testing
does
my
organization
need?
Penetration
testing
is
an
essential
tool
for
identifying,
analyzing,
and
mitigating
security
risks.
It
enables
cyber
defense
teams
to
assess
their
environment’s
susceptibility
to
attack
and
determine
the
effectiveness
of
existing
security
measures.
Pen
tests
range
from
simple
assessments
to
more
complex,
multi-stage
engagements.
Here
are
some
of
the
more
common
types
of
pen
testing:
-
Network
penetration
testing:
examines
the
organization’s
external
and
internal
networks,
as
well
as
its
software
infrastructure,
and
wireless
networks
to
identify
potential
weaknesses
and
vulnerabilities. -
Web
application
and
API
penetration
testing:
focuses
on
web
applications
and
looks
for
technical
and
business
logic
flaws
in
their
design,
code,
or
implementation
against
OWASP
Top
10
that
could
be
exploited
by
malicious
attackers. -
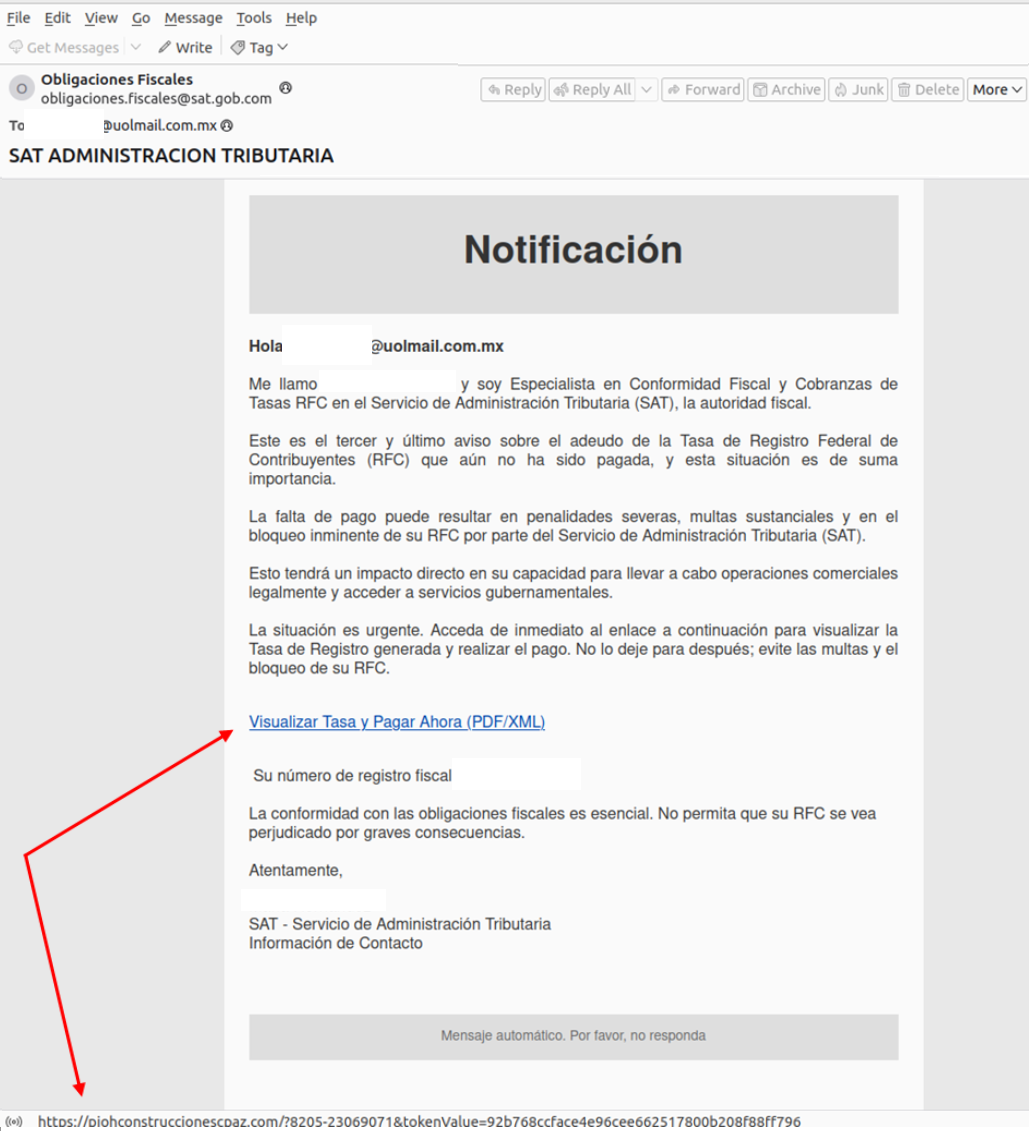
Social
engineering
penetration
testing:
simulates
a
cyber-attack
using
social
engineering
techniques,
such
as
phishing
emails
or
phone
calls,
to
gain
access
to
an
organization’s
confidential
information. -
Physical
penetration
testing:
evaluates
physical
security
measures,
such
as
access
controls
and
CCTV
systems,
to
identify
vulnerabilities
that
could
potentially
be
exploited
by
attackers. -
Cloud
penetration
testing:
evaluates
the
security
of
an
organization’s
cloud
infrastructure
and
applications. -
Mobile
app
penetration
testing:
analyzes
the
security
of
an
organization’s
mobile
applications,
looking
for
mobile-specific
security
issues
that
could
be
used
by
attackers.
Stages
of
the
Pen
Testing
process
No
matter
the
type
of
pen
testing
conducted,
there
are
typically
several
stages
to
go
through:
-
Planning
and
scoping:
involves
defining
the
test
objectives,
determining
the
scope,
and
setting
a
timeline. -
Reconnaissance
and
foot
printing:
gathering
information
about
the
target
systems
and
networks,
such
as
open
ports
and
services. -
Scanning
and
enumeration:
gaining
a
better
understanding
of
the
target
system,
such
as
user
accounts
and
services
running. -
Exploiting
any
identified
weaknesses:
attempting
to
exploit
any
identified
vulnerabilities. -
Post-testing
analysis
and
reporting:
analyzing
the
results,
documenting
any
findings,
and
creating
a
report
about
the
engagement.
Pen
testing
is
an
essential
part
of
any
organization’s
security
strategy,
and
by
understanding
the
different
types
of
testing
available
as
well
as
the
stages
of
the
process,
organizations
can
ensure
their
systems
are
adequately
protected
against
cyber
threats.
Why
organizations
should
use
PTaaS
to
prevent
cyber-attacks
Traditional
pen
testing
is
a
lengthy
and
labor-intensive
process.
It
requires
specialized
and
often
laser-focused
expertise
to
identify
and
exploit
security
flaws.
Hiring,
training,
and
retaining
security
professionals
is
costly,
time-consuming,
and
challenging.
Moreover,
point-in-time
remediation
does
not
ensure
protection
against
future
threats,
leaving
organizations
exposed
to
risks.
The
key
lies
in
combining
the
power
of
automation
with
the
hands-on
involvement
of
expert
security
professionals.
Penetration
Testing
as
a
Service
(PTaaS)
solutions
combine
automation
tools
that
continuously
monitor
networks
and
applications
for
potential
vulnerabilities
with
expert
consulting
services.
Penetration
Testing
as
a
Service
(PTaaS)
by
Outpost24
provides
organizations
an
end-to-end
solution
to
identify,
assess,
and
remediate
security
risks
on
an
ongoing
basis:
-
Hands-on
Expertise:
Outpost24’s
team
of
certified
security
experts
uses
the
latest
techniques
and
tools
to
deliver
accurate
and
thorough
pen
testing
results. -
Convenience:
Fully
managed
pen
testing
service
so
that
organizations
can
focus
on
their
core
business
without
allocating
resources
to
manage
the
testing
process. -
Cost-effectiveness:
By
outsourcing
pen
testing
to
Outpost24,
organizations
can
save
on
hiring
and
training
a
dedicated
in-house
team. -
Frequent
testing:
With
regular
testing
cycles,
organizations
can
stay
ahead
of
the
ever-evolving
threat
landscape
and
continuously
improve
their
cybersecurity
posture. -
Compliance:
Regular
pen
testing
is
often
a
requirement
for
industry
regulations
and
standards
such
as
PCI
DSS,
HIPAA,
and
ISO
27001.
Outpost24’s
solution
helps
organizations
meet
these
requirements
with
ease.
With
the
cost
of
breaches
reaching
an
all-time
high,
organizations
must
continuously
assess
and
monitor
their
system
for
any
vulnerabilities
or
weak
points.
Doing
so
will
help
them
stay
one
step
ahead
of
cybercriminals,
ensuring
their
digital
assets
are
adequately
protected.
PTaaS
by
Outpost24
provides
a
comprehensive
solution
that
helps
organizations
identify,
assess,
and
remediate
security
risks
on
an
ongoing
basis.
By
leveraging
the
power
of
automation
combined
with
the
expertise
of
seasoned
security
professionals,
PTaaS
helps
organizations
to
stay
secure
and
compliant.
For
more
information
about
how
Outpost24’s
penetration
testing
solutions
can
help
your
organization,
visit
Outpost24.com.