Microsoft linked a series of wiping attacks to a Russia-linked APT group, tracked as Cadet Blizzard, that is under the control of the GRU.
Microsoft attributes the operations carried out by the Russia-linked APT group tracked as Cadet Blizzard to the Russian General Staff Main Intelligence Directorate (GRU). The IT giant pointed out that Cadet Blizzard is distinct from other known APT groups operating under the control of the Russian military intelligence GRU, such as Forest Blizzard (STRONTIUM) and Seashell Blizzard (IRIDIUM).
Unlike other Russia-linked APT group, CadetBlizzard operations are extremely disruptive.

The Microsoft Threat Intelligence Center (MSTIC) initially tracked Cadet Blizzard as DEV-0586, the group was observed conducting destructive malware attacks against multiple organizations in Ukraine in January 2022.
The activity of the group was spotted a month before the invasion of Ukraine, Cadet Blizzard is the group that created and deployed the WhisperGate wiper. The group was also observed defacing the website of several Ukrainian organizations.
Microsoft believes that the group has been active since at least 2020, it focused on government services, law enforcement, non-profit/non-governmental organizations, IT service providers/consulting, and emergency services in Ukraine.
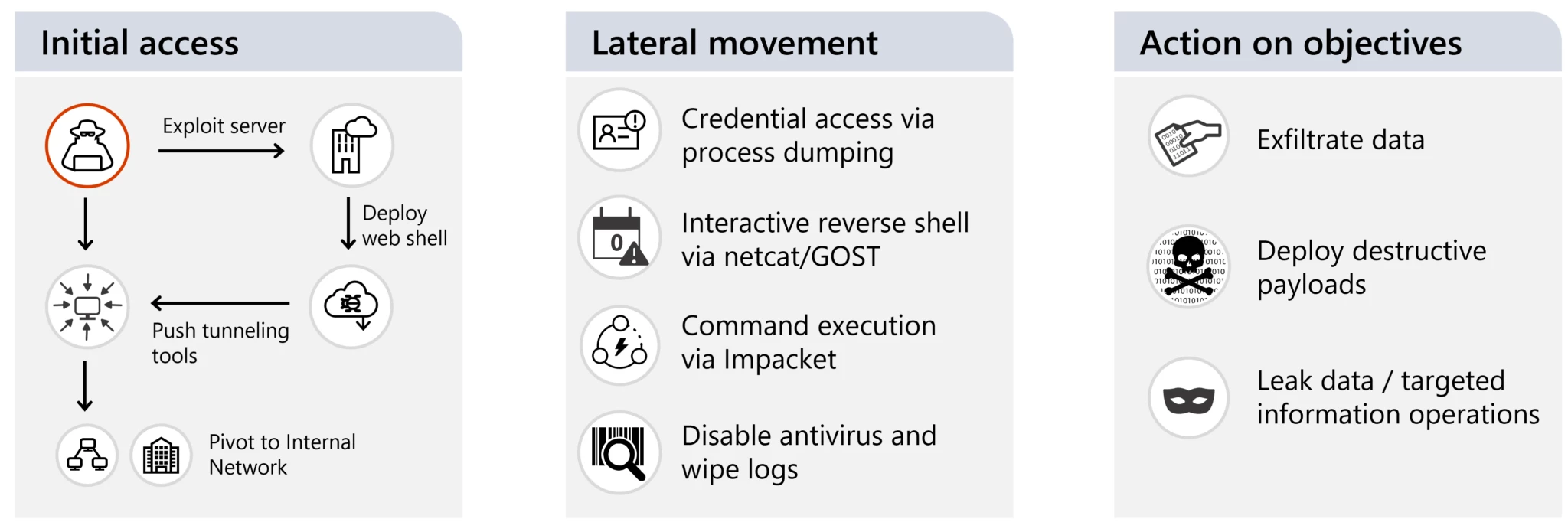
“Cadet Blizzard is a Russian GRU-sponsored threat group that Microsoft began tracking following disruptive and destructive events occurring at multiple government agencies in Ukraine in mid-January 2022.” reads the report published by Microsoft. “Cadet Blizzard compromises and maintains a foothold on affected networks for months, often exfiltrating data prior to disruptive actions. Microsoft observed Cadet Blizzard’s activity peak between January and June 2022, followed by an extended period of reduced activity.”
Micorosft observed a new surge in the activity of the group in January 2023, when the APT conducted multiple operations against entities in Ukraine and in Europe. The researcher noticed that the APT group is active seven days of the week and conducted their operations during their primary European targets’ off-business hours. The researchers warn that the APT group may target NATO member states supporting the military operations of the Ukrainian government.
Microsoft provided indicators of compromise to investigate environments and assess for potential compromise.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, GRU)







