A
surge
in
TrueBot
activity
was
observed
in
May
2023,
cybersecurity
researchers
disclosed.
“TrueBot
is
a
downloader
trojan
botnet
that
uses
command
and
control
servers
to
collect
information
on
compromised
systems
and
uses
that
compromised
system
as
a
launching
point
for
further
attacks,”
VMware’s
Fae
Carlisle
said.
Active
since
at
least
2017,
TrueBot
is
linked
to
a
group
known
as
Silence
that’s
believed
to
share
overlaps
with
the
notorious
Russian
cybercrime
actor
known
as
Evil
Corp.
Recent
TrueBot
infections
have
leveraged
a
critical
flaw
in
Netwrix
auditor
(CVE-2022-31199,
CVSS
score:
9.8)
as
well
as
Raspberry
Robin
as
delivery
vectors.
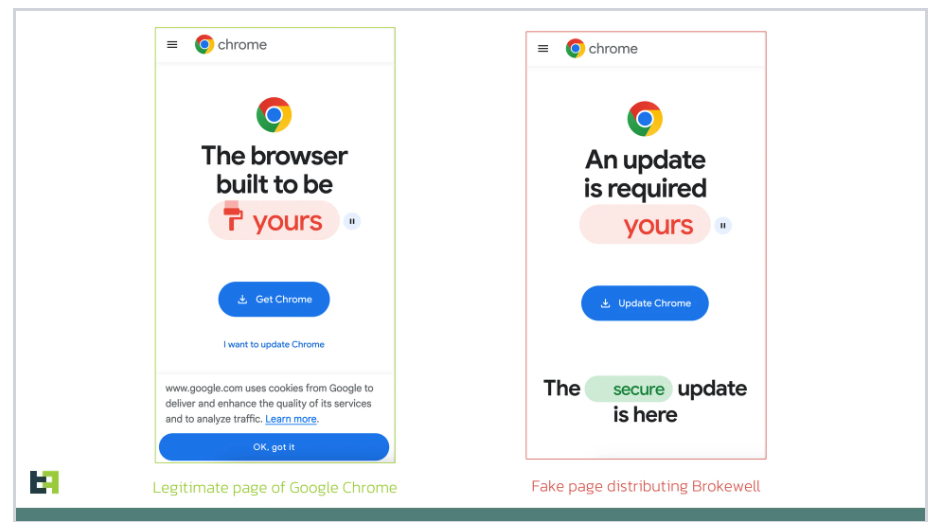
The
attack
chain
documented
by
VMware,
on
the
other
hand,
starts
off
with
a
drive-by-download
of
an
executable
named
“update.exe”
from
Google
Chrome,
suggesting
that
users
are
lured
into
downloading
the
malware
under
the
pretext
of
a
software
update.
Once
run,
update.exe
establishes
connections
with
a
known
TrueBot
IP
address
located
in
Russia
to
retrieve
a
second-stage
executable
(“3ujwy2rz7v.exe”)
that’s
subsequently
launched
using
Windows
Command
Prompt.
The
executable,
for
its
part,
connects
to
a
command-and-control
(C2)
domain
and
exfiltrates
sensitive
information
from
the
host.
It’s
also
capable
of
process
and
system
enumeration.
UPCOMING
WEBINAR
🔐
Mastering
API
Security:
Understanding
Your
True
Attack
Surface
Discover
the
untapped
vulnerabilities
in
your
API
ecosystem
and
take
proactive
steps
towards
ironclad
security.
Join
our
insightful
webinar!
“TrueBot
can
be
a
particularly
nasty
infection
for
any
network,”
Carlisle
said.
“When
an
organization
is
infected
with
this
malware,
it
can
quickly
escalate
to
become
a
bigger
infection,
similar
to
how
ransomware
spreads
throughout
a
network.”
The
findings
come
as
SonicWall
detailed
a
new
variant
of
another
downloader
malware
known
as
GuLoader
(aka
CloudEyE)
that’s
used
to
deliver
a
wide
range
of
malware
such
as
Agent
Tesla,
Azorult,
and
Remcos.
“In
the
latest
variant
of
GuLoader,
it
introduces
new
ways
to
raise
exceptions
that
hamper
complete
analysis
process
and
its
execution
under
controlled
environment,”
SonicWall
said.