.png)
Android
The Android VRP had an incredible record breaking year in 2022 with $4.8 million in rewards and the highest paid report in Google VRP history of $605,000!
In our continued effort to ensure the security of Google device users, we have expanded the scope of Android and Google Devices in our program and are now incentivizing vulnerability research in the latest versions of Google Nest and Fitbit! For more information on the latest program version and qualifying vulnerability reports, please visit our public rules page.
We are also excited to share that the invite-only Android Chipset Security Reward Program (ACSRP) – a private vulnerability reward program offered by Google in collaboration with manufacturers of Android chipsets – rewarded $486,000 in 2022 and received over 700 valid security reports.
We would like to give a special shoutout to some of our top researchers, whose continued hard work helps to keep Android safe and secure:
- Submitting an impressive 200+ vulnerabilities to the Android VRP this year, Aman Pandey of Bugsmirror remains one of our program’s top researchers. Since submitting their first report in 2019, Aman has reported more than 500 vulnerabilities to the program. Their hard work helps ensure the safety of our users; a huge thank you for all of their hard work!
- Zinuo Han of OPPO Amber Security Lab quickly rose through our program’s ranks, becoming one of our top researchers. In the last year they have identified 150 valid vulnerabilities in Android.
- Finding yet another critical exploit chain, gzobqq submitted our highest valued exploit to date.
- Yu-Cheng Lin (林禹成) (@AndroBugs) remains one of our top researchers submitting just under 100 reports this year.
Chrome
Chrome VRP had another unparalleled year, receiving 470 valid and unique security bug reports, resulting in a total of $4 million of VRP rewards. Of the $4M, $3.5 million was rewarded to researchers for 363 reports of security bugs in Chrome Browser and nearly $500,000 was rewarded for 110 reports of security bugs in ChromeOS.
This year, Chrome VRP re-evaluated and refactored the Chrome VRP reward amounts to increase the reward amounts for the most exploitable and harmful classes and types of security bugs, as well as added a new category for memory corruption bugs in highly privileged processes, such as the GPU and network process, to incentivize research in these critical areas. The Chrome VRP increased the fuzzer bonuses for reports from VRP-submitted fuzzers running on the Google ClusterFuzz infrastructure as part of the Chrome Fuzzing program. A new bisect bonus was introduced for bisections performed as part of the bug report submission, which helps the security team with our triage and bug reproduction.
2023 will be the year of experimentation in the Chrome VRP! Please keep a lookout for announcements of experiments and potential bonus opportunities for Chrome Browser and ChromeOS security bugs.
The entire Chrome team sincerely appreciates the contributions of all our researchers in 2022 who helped keep Chrome Browser, ChromeOS, and all the browsers and software based on Chromium secure for billions of users across the globe.
In addition to posting about our Top 0-22 Researchers in 2022, Chrome VRP would like to specifically acknowledge some specific researcher achievements made in 2022:
- Rory McNamara, a six-year participant in Chrome VRP as a ChromeOS researcher, became the highest rewarded researcher of all time in the Chrome VRP. Most impressive is that Rory has achieved this in a total of only 40 security bug submissions, demonstrating just how impactful his findings have been – from ChromeOS persistent root command execution, resulting in a $75,000 reward back in 2018, to his many reports of root privilege escalation both with and without persistence. Rory was also kind enough to speak at the Chrome Security Summit in 2022 to share his experiences participating in the Chrome VRP over the years. Thank you, Rory!
- SeongHwan Park (SeHwa), a participant in the Chrome VRP since mid-2021, has been an amazing contributor of ANGLE / GPU security bug reports in 2022 with 11 solid quality reports of GPU bugs earning them a spot on Chrome VRP 2022 top researchers list. Thank you, SeHwa!
Securing Open Source
Recognizing the fact that Google is one of the largest contributors and users of open source in the world, in August 2022 we launched OSS VRP to reward vulnerabilities in Google’s open source projects – covering supply chain issues of our packages, and vulnerabilities that may occur in end products using our OSS. Since then, over 100 bughunters have participated in the program and were rewarded over $110,000.
Sharing Knowledge
We’re pleased to announce that in 2022, we’ve made the learning opportunities for bug hunters available at our Bug Hunter University (BHU) more diverse and accessible. In addition to our existing collections of articles, which support improving your reports and avoiding invalid reports, we’ve made more than 20 instructional videos available. Clocking in at around 10 minutes each, these videos cover the most relevant learning topics and trends we’ve observed over the past years.
To make this happen, we teamed up with some of your favorite and best-known security researchers from around the globe, including LiveOverflow, PwnFunction, stacksmashing, InsiderPhD, PinkDraconian, and many more!
If you’re tired of reading our articles, or simply curious and looking for an alternative way to expand your bug hunting skills, these videos are for you. Check out our overview, or hop right in to the BHU YouTube playlist. Happy watching & learning!
Google Play
2022 was a year of change for the Google Play Security Reward Program. In May we onboarded both new teammates and some old friends to triage and lead GPSRP. We also sponsored NahamCon ‘22, BountyCon in Singapore, and NahamCon Europe’s online event. In 2023 we hope to continue to grow the program with new bug hunters and partner on more events focused on Android & Google Play apps.
Research Grants
In 2022 we continued our Vulnerability Research Grant program with success. We’ve awarded more than $250,000 in grants to over 170 security researchers. Last year we also piloted collaboration double VRP rewards for selected grants and are looking forward to expanding it even more in 2023.
If you are a Google VRP researcher and want to be considered for a Vulnerability Research Grant, make sure you opted in on your bughunters profile.
Looking Forward
Without our incredible security researchers we wouldn’t be here sharing this amazing news today. Thank you again for your continued hard work!
Also, in case you haven’t seen Hacking Google yet, make sure to check out the “Bug Hunters” episode, featuring some of our very own super talented bug hunters.
Thank you again for helping to make Google, the Internet, and our users more safe and secure! Follow us on @GoogleVRP for other news and updates.
Thank you to Adam Bacchus, Dirk Göhmann, Eduardo Vela, Sarah Jacobus, Amy Ressler, Martin Straka, Jan Keller, Tony Mendez, Rishika Hooda
]]>
It
has
been
another
incredible
year
for
the
Vulnerability
Reward
Programs
(VRPs)
at
Google!
Working
with
security
researchers
throughout
2022,
we
have
been
able
to
identify
and
fix
over
2,900
security
issues
and
continue
to
make
our
products
more
secure
for
our
users
around
the
world.
We
are
thrilled
to
see
significant
year
over
year
growth
for
our
VRPs,
and
have
had
yet
another
record
breaking
year
for
our
programs!
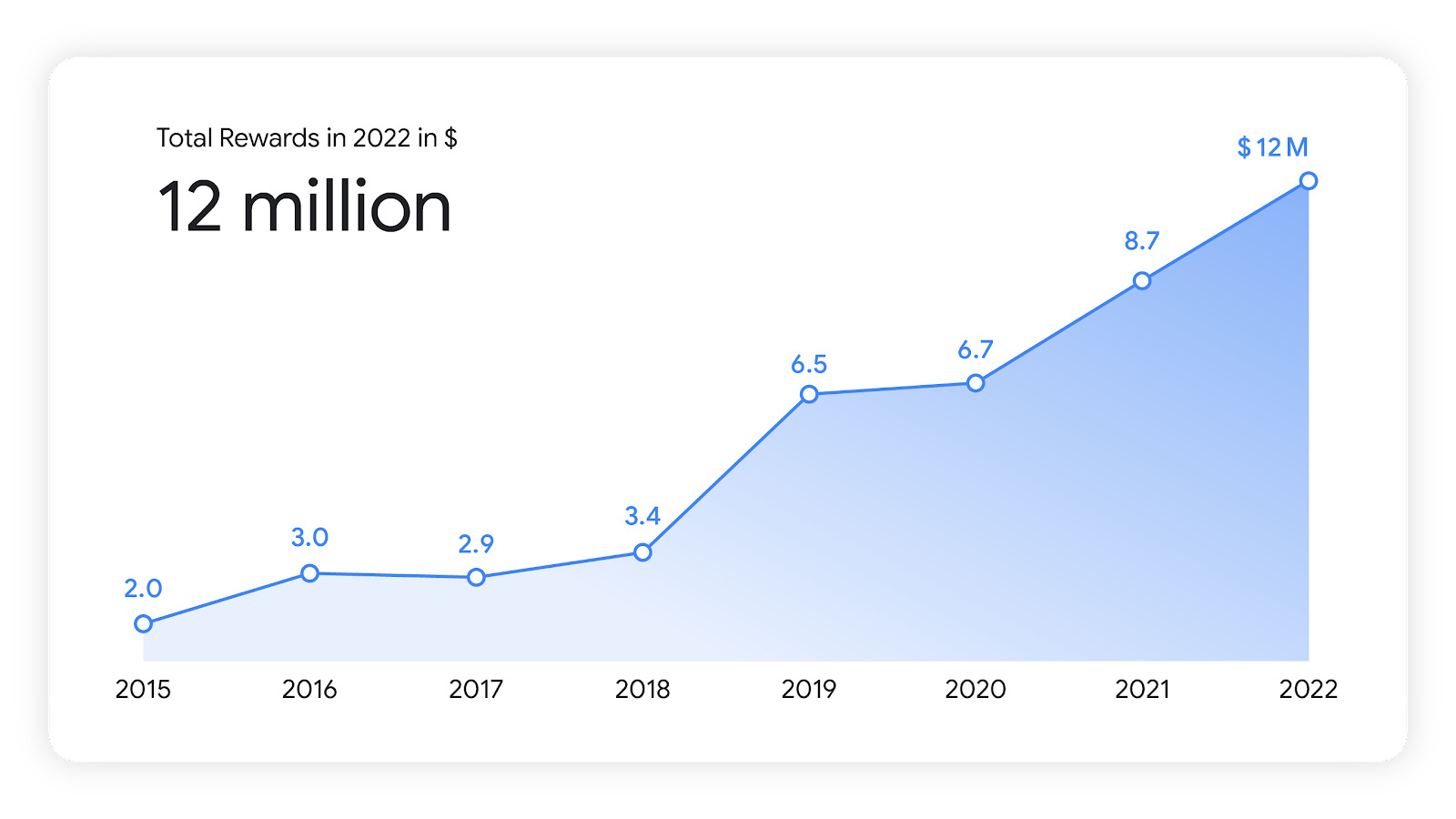
In
2022
we
awarded
over
$12
million
in
bounty
rewards
–
with
researchers
donating
over
$230,000
to
a
charity
of
their
choice.
As
in
past
years,
we
are
sharing
our
2022
Year
in
Review
statistics
across
all
of
our
programs.
We
would
like
to
give
a
special
thank
you
to
all
of
our
dedicated
researchers
for
their
continued
work
with
our
programs
–
we
look
forward
to
more
collaboration
in
the
future!
Android
The
Android
VRP
had
an
incredible
record
breaking
year
in
2022
with
$4.8
million
in
rewards
and
the
highest
paid
report
in
Google
VRP
history
of
$605,000!
In
our
continued
effort
to
ensure
the
security
of
Google
device
users,
we
have
expanded
the
scope
of
Android
and
Google
Devices
in
our
program
and
are
now
incentivizing
vulnerability
research
in
the
latest
versions
of
Google
Nest
and
Fitbit!
For
more
information
on
the
latest
program
version
and
qualifying
vulnerability
reports,
please
visit
our
public
rules
page.
We
are
also
excited
to
share
that
the
invite-only
Android
Chipset
Security
Reward
Program
(ACSRP)
–
a
private
vulnerability
reward
program
offered
by
Google
in
collaboration
with
manufacturers
of
Android
chipsets
–
rewarded
$486,000
in
2022
and
received
over
700
valid
security
reports.
We
would
like
to
give
a
special
shoutout
to
some
of
our
top
researchers,
whose
continued
hard
work
helps
to
keep
Android
safe
and
secure:
-
Submitting
an
impressive
200+
vulnerabilities
to
the
Android
VRP
this
year,
Aman
Pandey
of
Bugsmirror
remains
one
of
our
program’s
top
researchers.
Since
submitting
their
first
report
in
2019,
Aman
has
reported
more
than
500
vulnerabilities
to
the
program.
Their
hard
work
helps
ensure
the
safety
of
our
users;
a
huge
thank
you
for
all
of
their
hard
work! -
Zinuo
Han
of
OPPO
Amber
Security
Lab
quickly
rose
through
our
program’s
ranks,
becoming
one
of
our
top
researchers.
In
the
last
year
they
have
identified
150
valid
vulnerabilities
in
Android. -
Finding
yet
another
critical
exploit
chain,
gzobqq
submitted
our
highest
valued
exploit
to
date. -
Yu-Cheng
Lin
(林禹成)
(@AndroBugs)
remains
one
of
our
top
researchers
submitting
just
under
100
reports
this
year.
Chrome
Chrome
VRP
had
another
unparalleled
year,
receiving
470
valid
and
unique
security
bug
reports,
resulting
in
a
total
of
$4
million
of
VRP
rewards.
Of
the
$4M,
$3.5
million
was
rewarded
to
researchers
for
363
reports
of
security
bugs
in
Chrome
Browser
and
nearly
$500,000
was
rewarded
for
110
reports
of
security
bugs
in
ChromeOS.
This
year,
Chrome
VRP
re-evaluated
and
refactored
the
Chrome
VRP
reward
amounts
to
increase
the
reward
amounts
for
the
most
exploitable
and
harmful
classes
and
types
of
security
bugs,
as
well
as
added
a
new
category
for
memory
corruption
bugs
in
highly
privileged
processes,
such
as
the
GPU
and
network
process,
to
incentivize
research
in
these
critical
areas.
The
Chrome
VRP
increased
the
fuzzer
bonuses
for
reports
from
VRP-submitted
fuzzers
running
on
the
Google
ClusterFuzz
infrastructure
as
part
of
the
Chrome
Fuzzing
program.
A
new
bisect
bonus
was
introduced
for
bisections
performed
as
part
of
the
bug
report
submission,
which
helps
the
security
team
with
our
triage
and
bug
reproduction.
2023
will
be
the
year
of
experimentation
in
the
Chrome
VRP!
Please
keep
a
lookout
for
announcements
of
experiments
and
potential
bonus
opportunities
for
Chrome
Browser
and
ChromeOS
security
bugs.
The
entire
Chrome
team
sincerely
appreciates
the
contributions
of
all
our
researchers
in
2022
who
helped
keep
Chrome
Browser,
ChromeOS,
and
all
the
browsers
and
software
based
on
Chromium
secure
for
billions
of
users
across
the
globe.
In
addition
to
posting
about
our
Top
0-22
Researchers
in
2022,
Chrome
VRP
would
like
to
specifically
acknowledge
some
specific
researcher
achievements
made
in
2022:
-
Rory
McNamara,
a
six-year
participant
in
Chrome
VRP
as
a
ChromeOS
researcher,
became
the
highest
rewarded
researcher
of
all
time
in
the
Chrome
VRP.
Most
impressive
is
that
Rory
has
achieved
this
in
a
total
of
only
40
security
bug
submissions,
demonstrating
just
how
impactful
his
findings
have
been
–
from
ChromeOS
persistent
root
command
execution,
resulting
in
a
$75,000
reward
back
in
2018,
to
his
many
reports
of
root
privilege
escalation
both
with
and
without
persistence.
Rory
was
also
kind
enough
to
speak
at
the
Chrome
Security
Summit
in
2022
to
share
his
experiences
participating
in
the
Chrome
VRP
over
the
years.
Thank
you,
Rory! -
SeongHwan
Park
(SeHwa),
a
participant
in
the
Chrome
VRP
since
mid-2021,
has
been
an
amazing
contributor
of
ANGLE
/
GPU
security
bug
reports
in
2022
with
11
solid
quality
reports
of
GPU
bugs
earning
them
a
spot
on
Chrome
VRP
2022
top
researchers
list.
Thank
you,
SeHwa!
Securing
Open
Source
Recognizing
the
fact
that
Google
is
one
of
the
largest
contributors
and
users
of
open
source
in
the
world,
in
August
2022
we
launched
OSS
VRP
to
reward
vulnerabilities
in
Google’s
open
source
projects
–
covering
supply
chain
issues
of
our
packages,
and
vulnerabilities
that
may
occur
in
end
products
using
our
OSS.
Since
then,
over
100
bughunters
have
participated
in
the
program
and
were
rewarded
over
$110,000.
Sharing
Knowledge
We’re
pleased
to
announce
that
in
2022,
we’ve
made
the
learning
opportunities
for
bug
hunters
available
at
our
Bug
Hunter
University
(BHU)
more
diverse
and
accessible.
In
addition
to
our
existing
collections
of
articles,
which
support
improving
your
reports
and
avoiding
invalid
reports,
we’ve
made
more
than
20
instructional
videos
available.
Clocking
in
at
around
10
minutes
each,
these
videos
cover
the
most
relevant
learning
topics
and
trends
we’ve
observed
over
the
past
years.
To
make
this
happen,
we
teamed
up
with
some
of
your
favorite
and
best-known
security
researchers
from
around
the
globe,
including
LiveOverflow,
PwnFunction,
stacksmashing,
InsiderPhD,
PinkDraconian,
and
many
more!
If
you’re
tired
of
reading
our
articles,
or
simply
curious
and
looking
for
an
alternative
way
to
expand
your
bug
hunting
skills,
these
videos
are
for
you.
Check
out
our
overview,
or
hop
right
in
to
the
BHU
YouTube
playlist.
Happy
watching
&
learning!
Google
Play
2022
was
a
year
of
change
for
the
Google
Play
Security
Reward
Program.
In
May
we
onboarded
both
new
teammates
and
some
old
friends
to
triage
and
lead
GPSRP.
We
also
sponsored
NahamCon
‘22,
BountyCon
in
Singapore,
and
NahamCon
Europe’s
online
event.
In
2023
we
hope
to
continue
to
grow
the
program
with
new
bug
hunters
and
partner
on
more
events
focused
on
Android
&
Google
Play
apps.
Research
Grants
In
2022
we
continued
our
Vulnerability
Research
Grant
program
with
success.
We’ve
awarded
more
than
$250,000
in
grants
to
over
170
security
researchers.
Last
year
we
also
piloted
collaboration
double
VRP
rewards
for
selected
grants
and
are
looking
forward
to
expanding
it
even
more
in
2023.
If
you
are
a
Google
VRP
researcher
and
want
to
be
considered
for
a
Vulnerability
Research
Grant,
make
sure
you
opted
in
on
your
bughunters
profile.
Looking
Forward
Without
our
incredible
security
researchers
we
wouldn’t
be
here
sharing
this
amazing
news
today.
Thank
you
again
for
your
continued
hard
work!
Also,
in
case
you
haven’t
seen
Hacking
Google
yet,
make
sure
to
check
out
the
“Bug
Hunters”
episode,
featuring
some
of
our
very
own
super
talented
bug
hunters.
Thank
you
again
for
helping
to
make
Google,
the
Internet,
and
our
users
more
safe
and
secure!
Follow
us
on
@GoogleVRP
for
other
news
and
updates.
Thank
you
to
Adam
Bacchus,
Dirk
Göhmann,
Eduardo
Vela,
Sarah
Jacobus,
Amy
Ressler,
Martin
Straka,
Jan
Keller,
Tony
Mendez,
Rishika
Hooda