The Threat Within: How Intelligent Detection Prevented a Potential Internal Malware Incident
Executive Overview
Organizations often focus heavily on defending their perimeter against external attackers.

Apple says its upcoming 50th birthday treat is you
Executive Overview
Organizations often focus heavily on defending their perimeter against external attackers. Firewalls, threat intelligence feeds, and intrusion prevention systems are designed to stop threats attempting to break in from outside the network.
However, experienced security professionals understand an important reality. Threats that originate from within the network can sometimes be more dangerous than those coming from outside.
Once malicious files or compromised systems exist inside an environment, attackers can move laterally, disguise their actions as legitimate activity, and quietly prepare larger attacks such as data theft or ransomware deployment.
This is where intelligent, behavior driven security platforms become critical. During routine monitoring of an enterprise environment, the Seceon aiSIEM and aiXDR platform identified suspicious activity suggesting the presence of a malicious executable and abnormal internal file movement. By correlating signals across network telemetry, endpoint detection systems, and advanced malware analysis engines, the platform enabled the security team to detect and contain the threat before it escalated.
When Legitimate Protocols Become Attack Channels
Enterprise networks rely heavily on trusted protocols for daily operations. One widely used example is the Server Message Block protocol, which enables file sharing between systems.
Although SMB plays a legitimate role in enterprise collaboration, attackers frequently exploit it after gaining an internal foothold.
During continuous monitoring, Seceon detected suspicious activity involving the transfer of an executable file between internal systems using SMB over TCP port 445. While file sharing is a normal function within corporate environments, the nature of the transferred file and its behavioral indicators raised immediate concern.
Advanced malware analysis performed through an integrated sandbox engine classified the executable as malicious based on behavioral signatures and threat intelligence indicators.
Before the transfer operation could complete, the security control enforced a connection reset. This action prevented the malicious payload from being delivered and stopped the potential spread of malware across the network.
Hidden Malware Artifacts: A Common Attacker Technique
Around the same timeframe, endpoint monitoring identified another suspicious indicator. A malicious executable was discovered within a hidden system directory associated with the Windows Recycle Bin.
Attackers frequently abuse hidden or temporary directories to conceal malicious artifacts from casual inspection. Files placed in these locations are often used during the staging phase of an attack, where adversaries position their payloads before executing them later in the attack chain.
Because the file was executable and stored in a concealed directory, it presented a potential risk for triggering additional malicious activity such as persistence mechanisms or ransomware deployment.
Understanding the Adversary Playbook
The behavior observed in this incident aligns with tactics commonly used by advanced threat actors seeking to expand their presence within compromised environments.
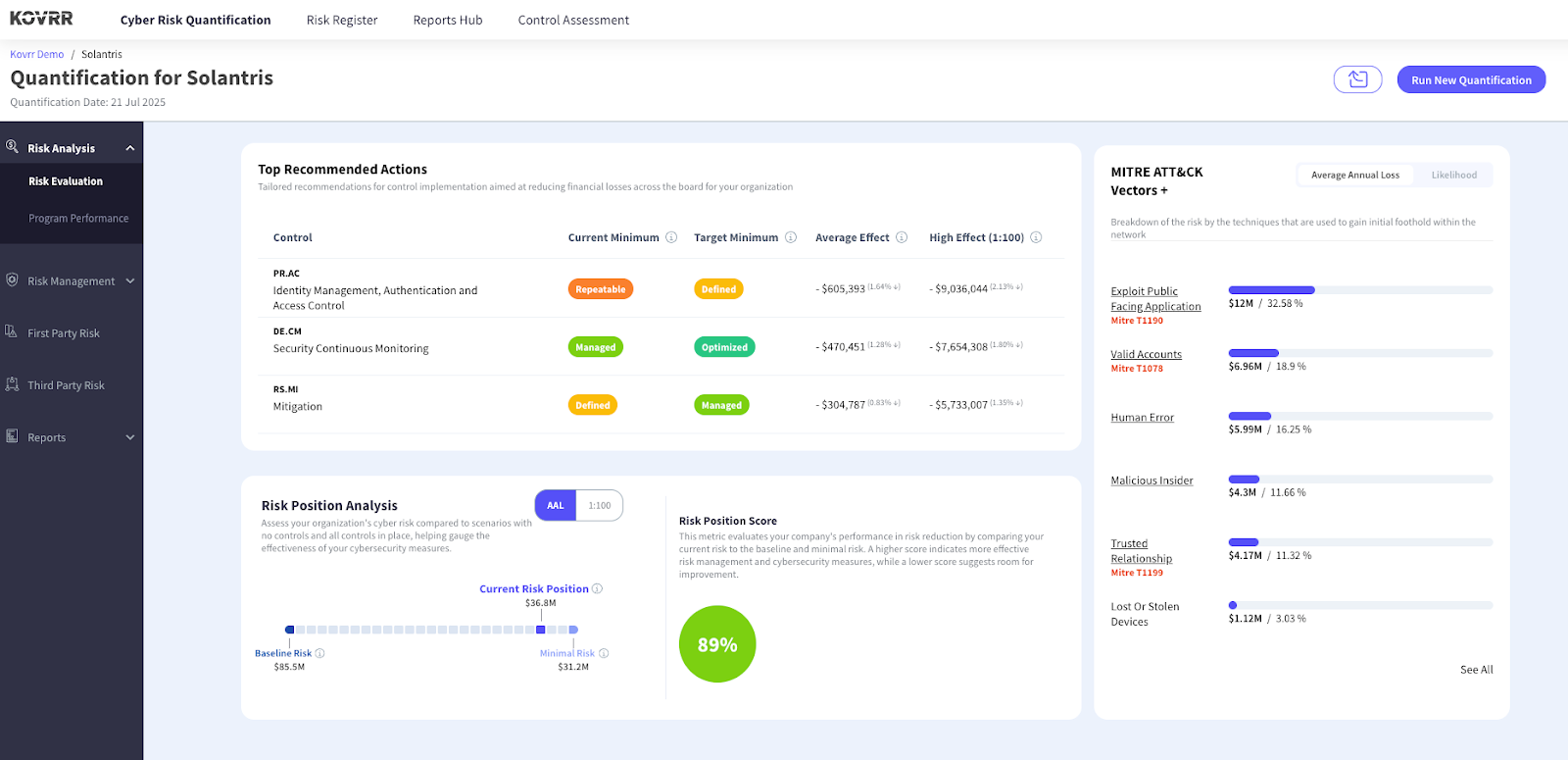
Several activities mapped closely to techniques described in the MITRE ATT&CK framework, including:
Remote services using SMB or Windows administrative shares for lateral movement
Ingress tool transfer used to distribute malicious utilities
User execution of malicious files delivered through deceptive artifacts
Data encryption for impact, a technique associated with ransomware operations
These techniques are frequently used in campaigns designed to establish persistence, move laterally across enterprise networks, and disrupt business operations.
Correlating Signals Across the Security Ecosystem
One of the most important aspects of this detection was the ability to correlate signals across multiple security layers.
The Seceon aiSIEM and aiXDR platform continuously ingests telemetry from across the enterprise environment, including:
Network traffic flows and metadata
Endpoint detection and response tools
Malware sandbox analysis engines
Threat intelligence feeds
Behavioral anomaly detection models
By analyzing these signals in real time and correlating them through advanced analytics, the platform transformed isolated alerts into a meaningful threat narrative.
This allowed the security operations team to understand not only what activity occurred but also its potential impact and progression within the attack lifecycle.
From Detection to Response
Once the suspicious indicators were identified, the security team initiated a structured investigation and containment process.
The response included reviewing endpoint execution logs and process histories, performing malware scans across potentially affected systems, conducting sandbox analysis of the suspicious executable, and investigating the origin of internal file transfer attempts.
Security analysts also monitored the environment for additional signs of lateral movement or follow up malicious activity.
This rapid investigation helped ensure that no additional malicious components remained within the environment.
The Importance of Detecting the Threat Within
Security teams often focus on preventing threats from entering the network. However, many modern cyber attacks become most dangerous only after they have already entered an environment.
A single malicious executable or compromised endpoint can become the starting point for widespread internal compromise.
In this case, the attempted malware transfer and hidden executable placement were detected during the early stages of the attack lifecycle. Early detection significantly reduced the potential impact and prevented larger consequences such as data exfiltration or ransomware deployment.
Empowering Security Teams with Intelligent Defense
Incidents like this highlight the growing importance of AI driven security analytics and cross platform visibility in modern cybersecurity operations.
By correlating signals across endpoints, networks, and threat intelligence sources, the Seceon aiSIEM and aiXDR platform helps organizations uncover subtle indicators of compromise that traditional tools may miss.
Transforming large volumes of telemetry into actionable intelligence allows security teams to move from reactive incident response toward proactive threat prevention.
In today’s complex threat landscape, the most dangerous attacks are often the ones that are already inside the network.
Conclusion
This incident demonstrates how intelligent monitoring and real time correlation can help organizations detect threats before they spread.
By identifying suspicious internal file transfers and hidden malware artifacts early in the attack lifecycle, the security team was able to interrupt malicious activity before it escalated into a broader compromise.
Continuous monitoring, contextual detection, and rapid response capabilities are essential components of a resilient cybersecurity strategy.
Organizations that adopt intelligent detection platforms gain the visibility needed to identify threats early and prevent them from evolving into large scale security incidents.
The post The Threat Within: How Intelligent Detection Prevented a Potential Internal Malware Incident appeared first on Seceon Inc.
*** This is a Security Bloggers Network syndicated blog from Seceon Inc authored by Aniket Gurao. Read the original post at: https://seceon.com/the-threat-within-how-intelligent-detection-prevented-a-potential-internal-malware-incident/