Researchers
spotted
a
new
information
stealer,
called
Stealc,
which
supports
a
wide
set
of
stealing
capabilities.
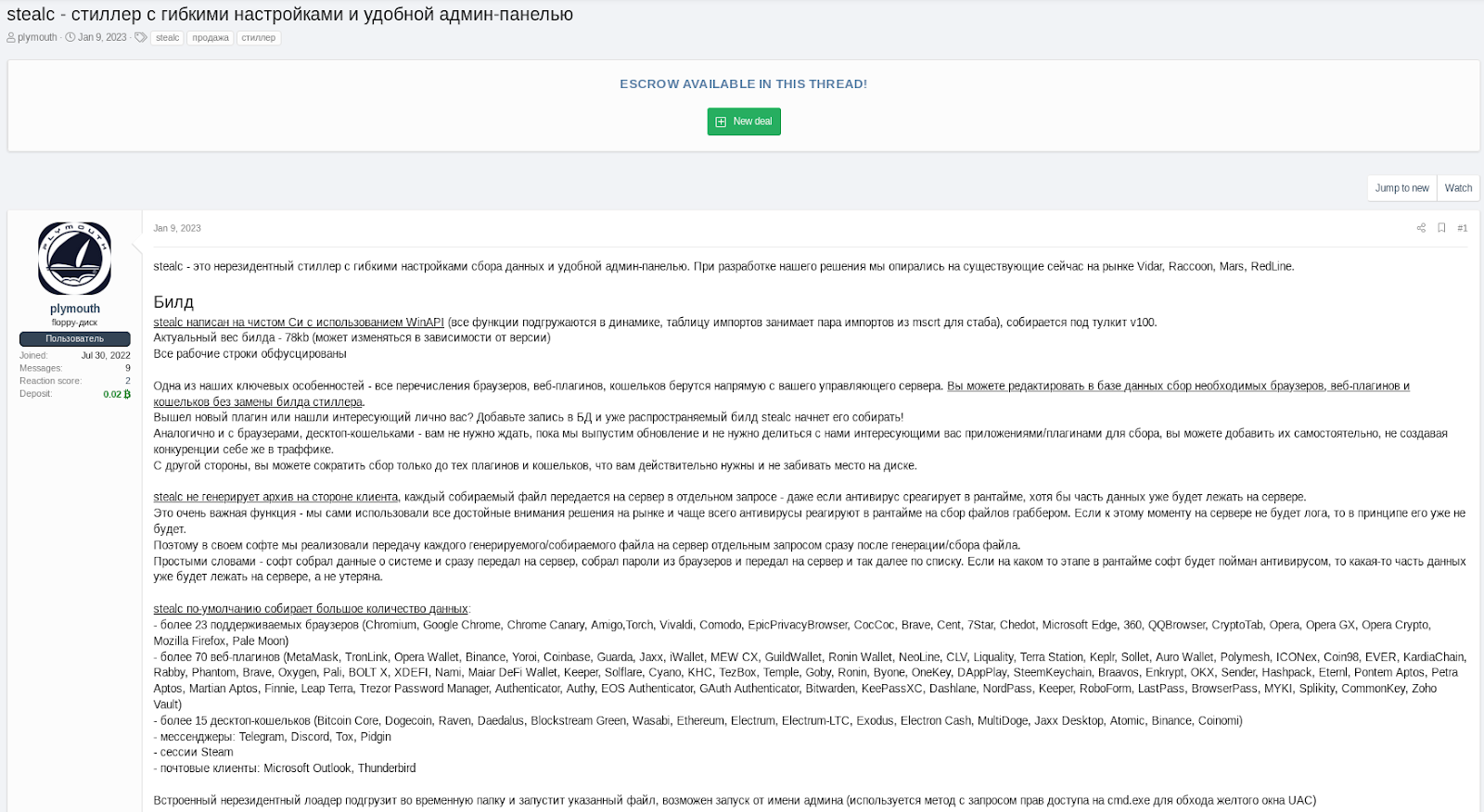
In
January
2023,
researchers
at
SEKOIA.IO
discovered
a new
information
stealer,
dubbed
Stealc,
which
was
advertised
in
the
dark
web
forums.
The
malware
was
developed
by
a
threat
actor
that
uses
the
moniker
Plymouth
who
claims
the
info-stealer
supports
a
wide
set
of
stealing
capabilities.
According
to
the
experts,
the
development
of
Stealc
relied
on
Vidar,
Raccoon,
Mars
and
Redline
stealers.
In
February
the
experts
found
several
dozens
of
Stealc
samples
in
the
wild,
they
were
showing
similarities
with
Vidar
and
Raccoon.
SEKOIA
identified
more
than
40
Stealc
C2
servers,
a
circumstance
that
confirms
the
increasing
popularity
of
the
malware
among
cybercriminals
distributing
stealers.
Stealc
is
able
to
steal
sensitive
data
from
popular web
browsers, browser
extensions
for
cryptocurrency
wallets, desktop
cryptocurrency
wallets and
also
information
from
other
applications,
such
as
email
and
messenger clients.
Unlike
other
stealers,
Stealc
implements
a
customizable
data
collection
configuration
and
supports
a customisable
file
grabber.
Attackers
can
define
a
set
of
grabber
rules
to
to
steal
specific
files
matching
them.
Plymouth already
released
several
versions
of
the
infostealer
malware
and
published
changelogs
on
hacking
forums,
as
well
as
on
a
dedicated
Telegram
channel.
The
most
recent
variant
observed
by
the
experts
is
v1.3.0,
released
on
February
11,
2023.
The
following
table
reports
the
Stealc
features
as
advertised
by Plymouth and
features
implemented
in
the
samples
observed
by
SEKOIA.IO.
|
Stealc features, as described by Plymouth on XSS |
SEKOIA.IO observations based on samples of the new malware family |
|
When developing our solution, we relied on Vidar, Raccoon, Mars and RedLine |
Stealc, Vidar, Raccoon and Mars all download legitimate third-party DLLs (sqlite3.dll, nss3.dll, etc.), as the found sample. |
|
Current build weight – 78kb |
The standalone sample is approximately 80KB. |
|
stealc was written in pure C using WinAPI |
C written malware uses WinAPI functions. |
|
all functions are dynamically loaded |
Once the strings are deobfuscated, the malware loads the WinAPI functions using GetProcAddress and LoadLibraryA. |
|
import table is taken by couple of imports from mscrt |
The import address table imports 6 functions from MsvcrtDLL. |
|
All lines of work are obfuscated. |
All strings are obfuscated using RC4 and base64, except a few ones which are related to new features (update v1.1.2). |
|
stealc does not generate an archive on the client side, each file to be collected is sent to the server in a separate request |
The malware exfiltrates the collected data file by file and doesn’t wait to receive all configuration to collect and send data. |
|
more than 23 supported browsers |
Based on the configuration sent by the C2, the malware targets 22 browsers. |
|
more than 70 web plugins |
Based on the configuration sent by C2, Stealc targets 75 plugins. |
|
more than 15 desktop wallets |
Based on the configuration sent by C2, Stealc targets 25 wallets. |
|
clients |
The sample collects data from Outlook files (Outlookaccounts.txt), the configuration is stored in the obfuscated data. |
|
added random name generation for script-gate (api.php), in stealc update v1.1.2 |
The first samples communicated on /api.php and downloaded the DLLs from /libs/. Recent samples used random paths ([a-f0-9]{16}) for data exfiltration and DLL download. |
|
recorded user-agents in the system_info.txt file, in stealc update v1.1.2 |
The malware exfiltrates victim host’s user agents. |
|
recorded ip and country in file system_info.txt, in stealc update v1.1.2 |
IP address and country of the infected host (ISO) are exfiltrated to the C2. |
Once
executed,
the
info-stealer
deobfuscates
all
its RC4-encrypted
and
base64-encoded
strings
and
performs
anti-analysis
checks
to
avoid
being
executed
in
a
sandbox
or
a
virtual
environment.
“The
malware
dynamically
loads
the
different
WinAPI
functions
using
LoadLibrary
and
GetProcAddress,
and
initiates
the
communication
to
its
C2
server”
reads
the
analysis
published
by
the
experts.
Stealc
collects
data
from
the
victim’s
browser,
extensions,
and
applications,
it
also
steals
files
matching
its
grabber
rules
if
active.
Then
data
are
exfiltrated
to
the
C2
and
the
malware
removes
itself
and
the
downloaded
DLL
files
from
the
compromised
system.
Attackers
use
YouTube
videos
to
distribute
the
malware.
The
videos
provide
instructions
on
how
to
install
cracked
software
along
with
links
to
a
download
site.
The
victims
are
tricked
into
downloading
malware-laced
software
from
this
site.
SEKOIA
published
indicators
of
compromise
(IoCs)
for
this
threat
along
with
YARA and Suricata rules
to
detect
the
the
information-stealer
“Stealc
is another
fully
featured
infostealer
sold
as
a
MaaS which
emerged
on
underground
forums
in
early
2023.”
concludes
the
report.
“However,
we
expect
that
the Stealc
infostealer
will
become
widespread
in
the
near
term,
as
multiple
threat
actors
add
the
malware
to
their
arsenal
while
it
is
poorly
monitored.
Companies
facing
stealer
compromise
need
to
be
aware
of
this
malware.”
Follow
me
on
Twitter:
@securityaffairs
and
Facebook
and
Mastodon
(SecurityAffairs –
hacking,
malware)