
Hackers Abuse Robinhood Signup Process to Deliver Phishing Emails

Robinhood users, beware.
Over the weekend, some Robinhood users received emails with the subject line “Your recent login to Robinhood.” On the surface, nothing seemed unusual. The messages appeared to come directly from the company’s official address, [email protected], and even passed standard email security checks.
The emails warned recipients about suspicious activity, including an “Unrecognized Device Linked to Your Account,” and urged them to act quickly.
As one version of the phishing message stated: “We detected a login attempt from a device that is not recognized,” and “If this was not you, please review your account activity immediately to secure your account.” A button labeled “Review Activity Now” directed users to a malicious site designed to steal login credentials, according to BleepingComputer.
Security researchers say the attackers didn’t hack Robinhood’s systems in the traditional sense. Instead, they exploited a flaw in the platform’s account creation process.
When a new account is registered, Robinhood automatically sends a login notification email that includes details like device type, IP address, and location. The attackers found a way to manipulate this process by injecting malicious HTML code into the “device name” field during signup.
Because this field wasn’t properly sanitized, the injected code was rendered inside the legitimate email, effectively embedding a phishing message within a real notification. The result was an email that looked authentic, passed SPF and DKIM checks, and came from Robinhood’s own infrastructure, making it extremely difficult for users to spot the scam.
How attackers reached users
To deliver these emails to real users, attackers reportedly used a technique known as Gmail “dot aliasing,” where slight variations of an email address still route to the same inbox. This allowed them to create new accounts that would trigger emails to intended victims.
Experts also believe the attackers may have relied on previously leaked email lists, possibly linked to Robinhood’s 2021 data breach that exposed millions of customer records.
Robinhood responds
Robinhood acknowledged the issue in a statement on X:
“On Sunday evening, some customers received a falsified email from [email protected] with the subject line ‘Your recent login to Robinhood.’ This phishing attempt was made possible by an abuse of the account creation flow. It was not a breach of our systems or customer accounts, and personal information and funds were not impacted.”
The company said it has since fixed the vulnerability, including removing the field that allowed the malicious content to be injected. Robinhood is urging users who received the email to delete it and avoid clicking any links. The company also advises contacting support only through its official app or website if there are concerns.
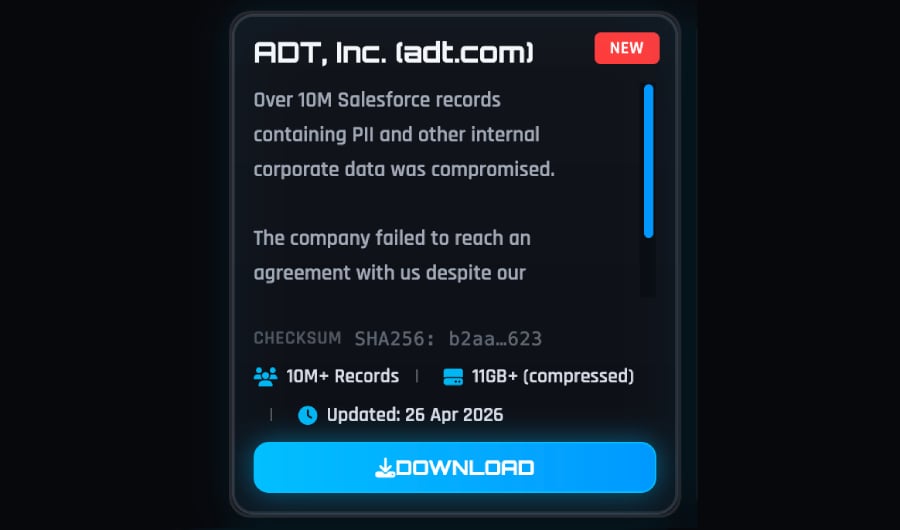
Check out our roundup of 2026 cyberattacks to see how breaches, phishing risks, and software flaws are shaping the year’s security landscape.





.png)


