Fingerprinting Is Broken. Here’s How We Fixed It.
The invisible problem costing businesses millions — and the Arkose Labs solution
Every time a user visits a website or opens an app, their device leaves a fingerprint.

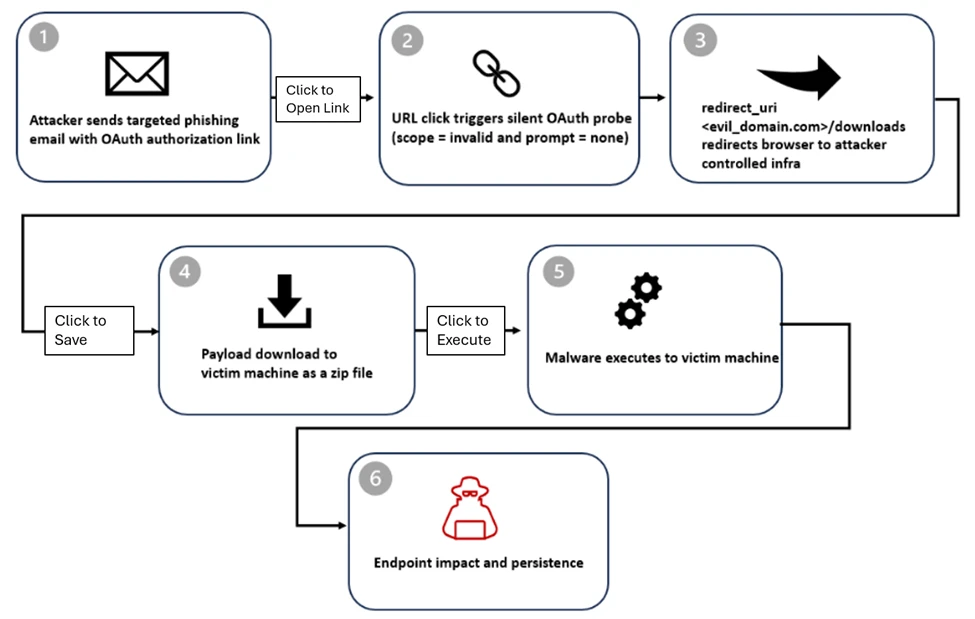
OAuth phishers make ‘check where the link points’ advice ineffective
The invisible problem costing businesses millions — and the Arkose Labs solution
Every time a user visits a website or opens an app, their device leaves a fingerprint. Browser version, screen resolution, installed fonts, graphics hardware — hundreds of signals that, combined, can uniquely identify a device even without cookies or a login. For fraud prevention, this fingerprint is invaluable. It’s one of the few signals that persists across sessions, accounts and even identity changes.
But fingerprinting has a dirty secret: it breaks. Quietly, invisibly and at scale.
At Arkose Labs, device fingerprinting sits at the core of how we detect and stop fraud. To address the changing threat landscape, we knew we had to overcome the traditional fail-points of fingerprinting – building a system that no longer treats every fingerprint as a static snapshot, but instead understands devices as dynamic, evolving entities. The result is our latest release of Arkose Device ID.
Where Device Fingerprinting Falls Short
The industry’s standard approach to device fingerprinting has traditionally been static and fairly simplistic: take a set of device signals, hash them, and produce an ID. Simple, fast, and for a long time, sufficient.
But the modern web has made this traditional approach increasingly fragile. Browsers routinely update, users switch networks, operating systems push patches, and privacy tools deliberately randomize signals to prevent tracking. Each of these events can produce a different hash from the same physical device, fragmenting what should be a single identity into dozens of disconnected records.
We call this the division problem — one real device, many IDs.
The opposite problem is equally damaging. Some device signals are so common — a standard screen resolution, a popular browser version, a shared corporate network — that thousands of completely different devices produce identical fingerprints.
We call this the collision problem — one ID, many real devices.
In our analysis across major platforms, more than one in five device IDs produced by static systems were shared across multiple distinct users. That’s not a fingerprinting system. That’s noise.
Division inflates your device population with phantom records, making historical signals useless and causing false negatives. Collision ties innocent users to fraudulent behavior they have nothing to do with, driving false positives and eroding trust.
Where Fingerprinting Hits Its Ceiling
Improving static fingerprinting is a game of diminishing returns. You can add more signals, weight them differently, or apply more sophisticated hashing — but you are fundamentally trying to solve an unsolvable problem with the wrong tool.
Consider two users on identical MacBook Pro models, running the same browser. Static fingerprinting forces a difficult trade-off: use unstable signals and risk division — any time a signal changes, the device gets a new ID — or stick to only stable signals to avoid that, but now you’re working with a much smaller pool of attributes. The smaller that pool, the less you can distinguish between devices, and the more collision you introduce. It’s a catch-22 baked into the architecture itself. More signals don’t fix this. The moment you expand beyond what’s stable, you’re back to taking snapshots of something that moves.
The industry’s open secret is that device identification has never been purely about fingerprints. The most reliable commercial solutions have always layered multiple identification strategies — because no single signal is robust enough to maintain accuracy in a real-world threat environment.
We built Arkose Device ID on this same foundational truth, then went further — designing a system that treats change as signal, not noise. Whether a device evolves naturally over time or an actor attempts to manipulate its fingerprint, the system is built to know the difference.
The Architecture of Arkose Device ID: Hybrid by Design
The Intelligence Behind Arkose Device ID
The core challenge was straightforward to state and hard to solve: produce one reliable identity for every device, regardless of how it changes over time or what an attacker does to obscure it. That required abandoning the assumption that any single identification method could be sufficient. The most accurate device identification comes from multiple complementary capabilities working in concert, each compensating for the other’s failure modes. The result is a single, unified output — the Arkose ID — that is both precise on first encounter and persistent across every return visit.
Recognition Without History (Stateless Identification)
The first capability generates an Arkose ID purely from signals present in the current session — no prior history required, making it fast to deploy and inherently privacy-preserving. Rather than producing a brittle static fingerprint that breaks the moment a user updates their browser or changes networks, it uses an AI-powered model to understand how similar a device is to others it has seen — not just whether it matches exactly. This shifts the question from “is this fingerprint identical?” to “how similar is this device, and does that similarity matter?” — a far more meaningful standard for fraud detection.
Recognition Across Time (Stateful Identification)
The second capability gives the Arkose ID its memory. When a device is encountered for the first time, an identity is established. When it returns — even with an altered fingerprint — the system evaluates whether it has been seen before, treating signal changes as information rather than failure. Organic evolution looks different from deliberate manipulation, and the system is designed to know the difference. All of this happens in milliseconds, well within the latency demands of real-time risk decisioning.
One ID. Two Sources of Confidence.
These capabilities are designed to reinforce each other, together producing a single Arkose ID you can act on. When signals align, confidence is high. When they diverge — a device that looks familiar on the surface but doesn’t match its own history — that gap becomes a fraud signal in its own right. It’s not just identification. It’s intelligence.
Solving Collisions and Divisions at Scale
Enterprise deployments don’t forgive identity errors — a collision means two devices sharing an ID they shouldn’t; a division means one device fragmented across IDs it shouldn’t have. With the new architecture in place, we focused on systematically driving both rates down to a level that holds under real-world fraud pressure.
Understanding Collisions in the Wild
Not all collisions are equal. Our analysis revealed three distinct causes that, in combination, make collision a far harder problem than it first appears.
Shared infrastructure — Corporate networks, university campuses and residential ISPs where many users share the same network environment produce fingerprints that look identical to a static system. These are not fraud signals; they are geography.
Common hardware — Identical device models with default configurations, particularly common in consumer markets, produce near-identical fingerprints regardless of who is using them.
Adversarial homogenization — Sophisticated fraud operations deliberately attempt to blend in with legitimate user profiles, intentionally manufacturing collisions to hide in the crowd.
Each of these requires a different response. Arkose Device ID approaches each collision type with tailored signals and models designed to surface the differences that static fingerprinting misses. Critically, adversarial homogenization is designed to be detected — because Arkose Device ID builds a continuous identity record across sessions, it has the historical context to recognize when a device starts behaving like something it isn’t.
The Results
The impact on collision rates was dramatic. Across our production traffic:
Collision rates dropped significantly — meaning far more device IDs now map to a single, distinct user, directly translating to fewer innocent users incorrectly tied to fraud signals
False positive rates on device-based signals improved proportionally
Device ID persistence improved significantly, strengthening the signal quality of historical device reputation
Division rates showed similar improvement. As fingerprints shift with browser updates or network changes, Arkose Device ID is designed to link those sessions to a single persistent identity — meaningfully reducing the fragmentation that undermines trust scores and friction decisions downstream.
What This Means in Practice
For fraud and risk teams, the practical implications of this new version of Arkose Device ID are significant.
Historical device reputation becomes reliable. When a device ID is stable and accurate, the history attached to it — past decisions, past behavior, past associations — can be trusted. A device that has been involved in chargebacks, account takeovers or credential stuffing carries that history forward reliably.
Low-risk users face less friction. False positives are not just an operational problem — they are a revenue problem. Every legitimate user incorrectly flagged as suspicious is a potential churned customer. By meaningfully reducing collision rates, Arkose Device ID shrinks the population of innocent devices incorrectly associated with fraud signals.
Sophisticated attackers have less room to hide. Because Arkose Device ID builds a continuous identity record across sessions, evasion attempts don’t produce a clean slate — they produce a detectable pattern. That pattern is itself a signal.
Looking Forward
This latest release of Arkose Device ID represents a shift in how we think about identity at the device level — from a static label assigned at a point in time to a living, continuously updated representation that reflects the full history of a device’s interactions with the web.
Perfect device identification isn’t a realistic goal — and any vendor claiming otherwise should be questioned. The signal space is finite, real-world device diversity is vast, and the hard limits are real. What is achievable is a system engineered to perform well within those limits — accurate enough, persistent enough and resilient enough to make a meaningful difference at enterprise scale.
That’s what Arkose Device ID is built to be.
*** This is a Security Bloggers Network syndicated blog from Arkose Labs authored by Ashish Mittal. Read the original post at: https://www.arkoselabs.com/blog/fingerprinting-is-broken-heres-how-we-fixed-it/