Recent
reports
of
Lockbit
locker-based
attacks
against
North
European
SMBs
indicate
that
local
crooks
started
using
Lockbit
locker
variants.
Executive
Summary
-
During
the
past
months,
the
Lockbit
gang
reached
very
high
popularity
in
the
underground
ecosystem. -
The
recent
Hive
infrastructure
takedown
as
well
as
other
major
gangs
dissolution
such
as
Conti
in
2022,
is
making
room
in
the
cybercrime
business -
The
Lockbit
locker
leaked
a
few
months
ago
in
the
underground,
is
increasing
its
popularity
and
adoption
among
micro-criminal
actors. -
Recent
reports
of
Lockbit
locker-based
extortions
against
North
European
SMBs
indicate
that
local
cyber-criminal
gangs
started
adopting
Lockbit
locker
variants.
Incident
Insights
Recently,
there
has
been
a
significant
increase
in
ransomware
attacks
targeting
companies
in
northern
Europe.
These
attacks
are
being
carried
out
using
the
LockBit
locker,
which
is
known
to
be
in
use
by
the
homonymous
criminal
affiliation
program.
The
Lockbit
group
has
been
targeting
companies
of
all
sizes
and
across
a
wide
range
of
industries,
causing
significant
disruptions
and
financial
losses.
One
of
the
most
concerning
aspects
of
these
recent
attacks
is
the
way
in
which
they
are
being
conducted.
The
LockBit
Locker
group
is
known
for
using
a
combination
of
advanced
techniques,
even
phishing,
and
also
social
engineering,
to
gain
initial
access
to
a
company’s
network.
Once
they
have
access,
they
use
a
variety
of
tools
and
techniques
to
move
laterally
throughout
the
network,
compromising
systems
and
stealing
sensitive
data.
One
of
the
most
recent
attacks
was
reported
by
Computerland
in
Belgium
against
SMBs
in
the
country,
but
according
to
the
company
they
were
targeted
by
a
group
of
cybercriminals
who
appeared
to
be
using
a
variant
of
the
LockBit
locker
malware.
However,
upon
further
investigation,
it
was
discovered
that
these
attackers
were
not
likely
related
to
the
real
LockBit
group,
but
rather
“wannabes”
who
had
obtained
a
leaked
version
of
the
malware.
Despite
not
being
the
true
LockBit
Locker
group,
these
micro
criminals
were
still
able
to
cause
significant
damage
by
encrypting
a
large
number
of
internal
files.
However,
the
company
was
able
to
restore
its
network
from
backups
and
no
client
workstations
were
affected
during
the
intrusions.
Among
the
increasing
popularity
of
extortion
practices
in
the
criminal
underground,
even
among
less
sophisticated
actors,
this
incident
also
highlights
the
dangers
of
outdated
software
and
systems.
In
fact,
in
this
case,
the
attackers
were
able
to
exploit
unpatched
vulnerabilities
in
the
company’s
FortiGate
firewall.
Unpached
FortiGate
firewalls
have
several
vulnerabilities
that
are
currently
exploited
by
cybercriminals
according
to
the
CISA’s
Known
Exploited
Vulnerabilities
Catalog,
but
in
these
recent
cases,
the
exploited
flaws
were
the
infamous
“Fortifuck”
flaws
straight
back
from
2018.
Those
flaws
have
been
exploited
through
unattended
exposure
through
a
company’s
branch
internet
gateway.
These
network
gateways
are
often
less
well-protected
than
the
company’s
main
network
and
typically
provide
an
easier
entry
point
for
attackers.
In
conclusion,
the
recent
ransomware
attacks
targeting
North
European
SMBs
companies
are
a
serious
concern
for
many
reasons:
despite
the
reduced
effectiveness
due
to
the
lack
of
experience
of
the
criminal
operators,
the
targeted
industries
suffered
important
outages
and
data
exfiltration.
Threat
Actor
Brief
LockBit
is
a
well-known
ransomware
affiliation
program
started
back
in
September
2019,
where
the
developers
use
third
parties
to
spread
the
ransomware
by
hiring
unethical
penetration
testing
teams.
The
gang
was
one
of
the
first
gangs
operating
double
extortion
practices
and
supporting
such
attacks
with
dedicated
toolkits
such
as
the
Stealbit
malware.
During
his
infamous
career,
Lockbit
operators
hit
high-value
targets
such
as
Accenture
and
Royal
Mail,
but
also
a
large
number
of
small
and
medium
businesses
worldwide.
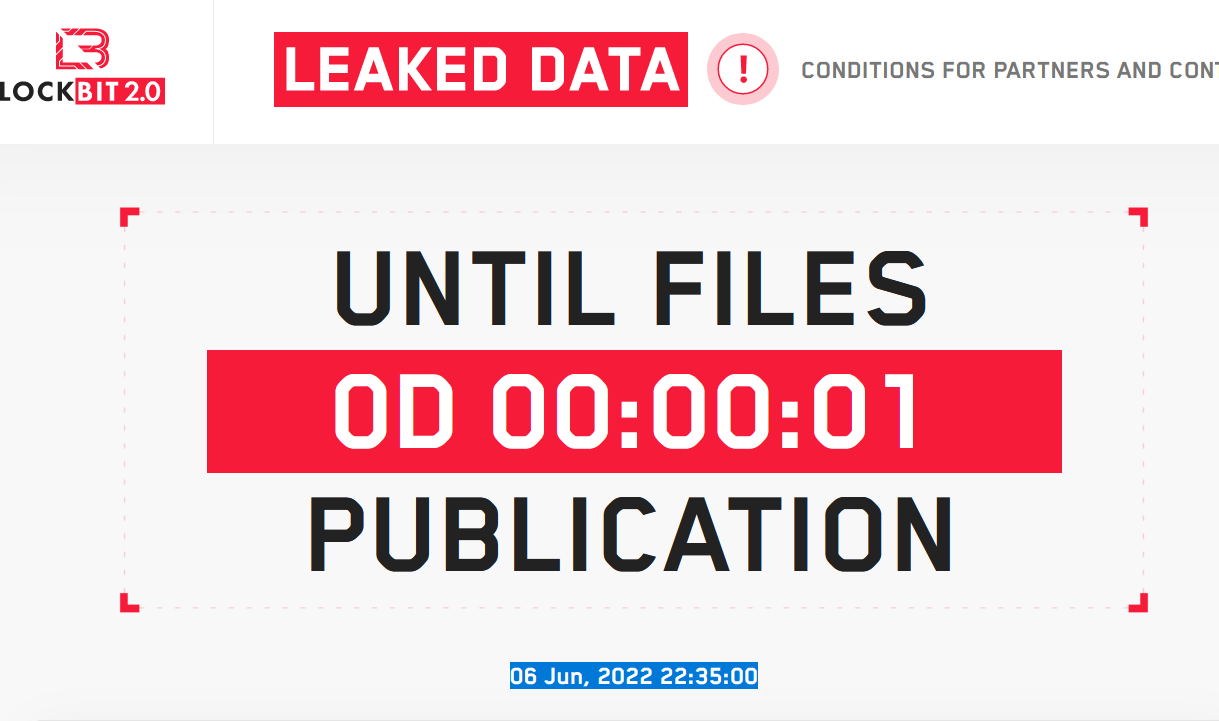
Once
an
environment
is
infected,
the
victim
is
sent
to
the
gang
payment
site
managed
by
the
ransomware
developers
who
threaten
to
leak
the
victim’s
data
to
extort
further
payments.
About
the
author:
Luca
Mella,
Cyber
Security
Expert,
Response
&
Threat
Intel
|
Manager
In
2019,
Luca
was
mentioned
as
one
of
the
“32
Influential
Malware
Research
Professionals”.
He
is
a
former
member
of
the
ANeSeC
CTF
team,
one
of
the
firsts
Italian
cyber
wargame
teams
born
back
in
2011.
Follow
me
on
Twitter:
@securityaffairs
and
Facebook
and
Mastodon
(SecurityAffairs –
hacking,
Lockbit)






