Apple urges iPhone users to update as Coruna and DarkSword exploit kits emerge
Apple urges iPhone users to update as Coruna and DarkSword exploit kits emerge

Apple warns that outdated iPhones are vulnerable to Coruna and DarkSword exploit kits and urges users to update iOS.
Apple has warned that iPhones running outdated iOS versions are at risk from exploit kits like Coruna and DarkSword. These attacks use malicious web content to trigger infection chains that can steal sensitive data. Users are strongly advised to update their devices to stay protected.
“Security researchers recently identified web-based attacks that target out-of-date versions of iOS through malicious web content. For example, if you’re using an older version of iOS and were to click a malicious link or visit a compromised website, the data on your iPhone might be at risk of being stolen.” reads Apple’s advisory. “We thoroughly investigated these issues as they were found and released software updates as quickly as possible for the most recent operating system versions to address vulnerabilities and disrupt such attacks.”
Keeping the iPhone updated is the most effective way to stay protected from threats like Coruna and DarkSword. Devices running the latest iOS versions are not vulnerable, and Lockdown Mode also blocks these attacks, even on older systems, though updates are still strongly recommended.
If your iPhone runs an older iOS version, take action:
- Devices on iOS 15 to iOS 26 are already protected if fully updated
- Apple released updates on March 11, 2026, to extend protection to iOS 15 and 16 devices
- Devices on iOS 13 or 14 must upgrade to iOS 15 and install a Critical Security Update
- Safari’s Safe Browsing feature helps block known malicious domains by default
Updating ensures user data remains secure.
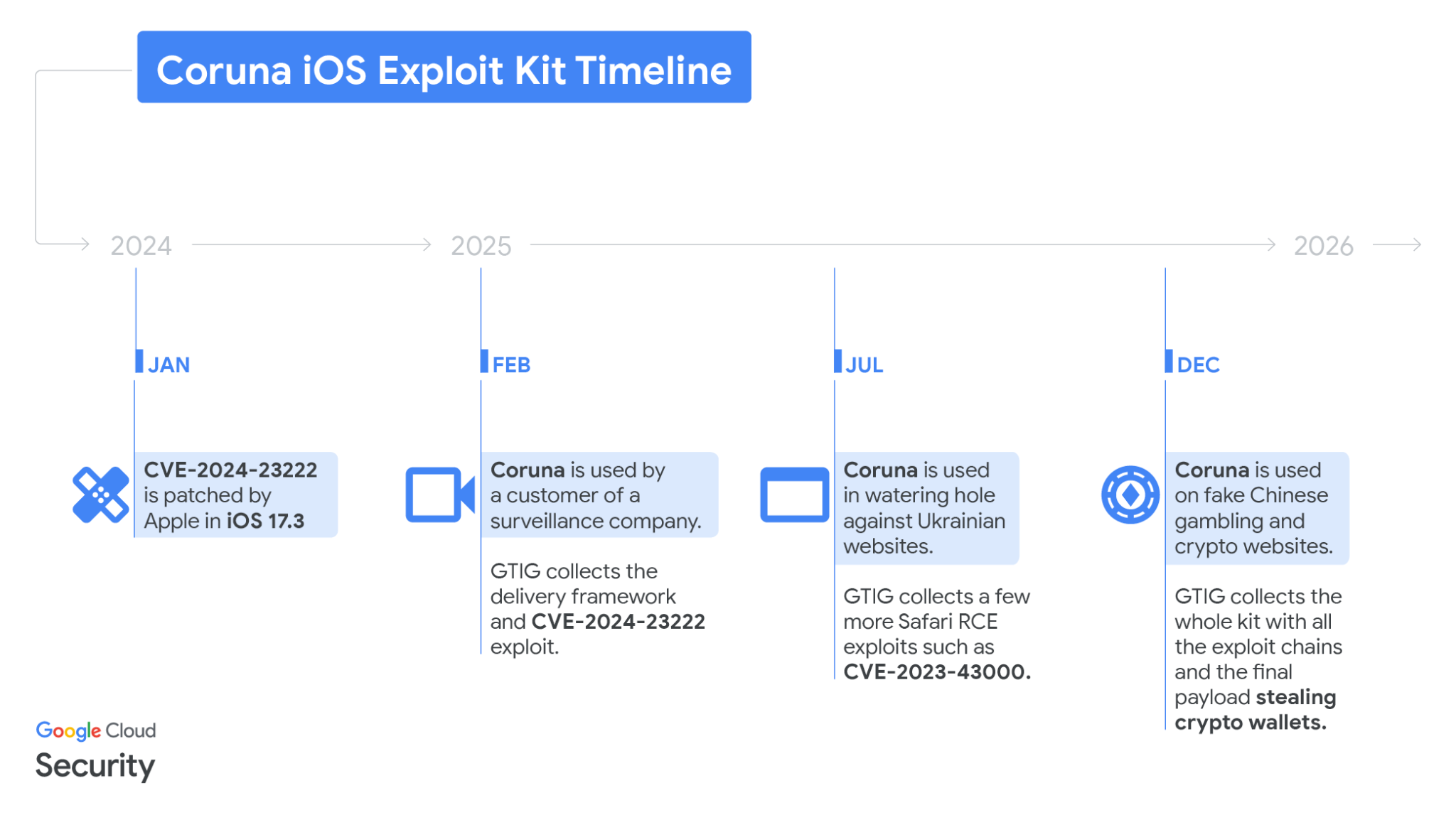
In February, Google’s Threat Intelligence Group identified a powerful new iOS exploit kit called Coruna (also known as CryptoWaters) that targets Apple iPhones running iOS versions 13.0 through 17.2.1. The kit includes five full exploit chains and a total of 23 exploits.
| Codename | CVE | Type |
|---|---|---|
| buffout | CVE-2021-30952 | WebContent R/W |
| jacurutu | CVE-2022-48503 | WebContent R/W |
| bluebird | No CVE | WebContent R/W |
| terrorbird | CVE-2023-43000 | WebContent R/W |
| cassowary | CVE-2024-23222 | WebContent R/W |
| breezy | No CVE | WebContent PAC bypass |
| breezy15 | No CVE | WebContent PAC bypass |
| seedbell | No CVE | WebContent PAC bypass |
| seedbell_16_6 | No CVE | WebContent PAC bypass |
| seedbell_17 | No CVE | WebContent PAC bypass |
| IronLoader | CVE-2023-32409 | WebContent sandbox escape |
| NeuronLoader | No CVE | WebContent sandbox escape |
| Neutron | CVE-2020-27932 | PE |
| Dynamo | CVE-2020-27950 | PE (infoleak) |
| Pendulum | No CVE | PE |
| Photon | CVE-2023-32434 | PE |
| Parallax | CVE-2023-41974 | PE |
| Gruber | No CVE | PE |
| Quark | No CVE | PPL Bypass |
| Gallium | CVE-2023-38606 | PPL Bypass |
| Carbone | No CVE | PPL Bypass |
| Sparrow | CVE-2024-23225 | PPL Bypass |
| Rocket | CVE-2024-23296 | PPL Bypass |
While highly capable against iPhones running iOS 13.0 through 17.2.1versions, Coruna is ineffective against the latest iOS release, according to Google.
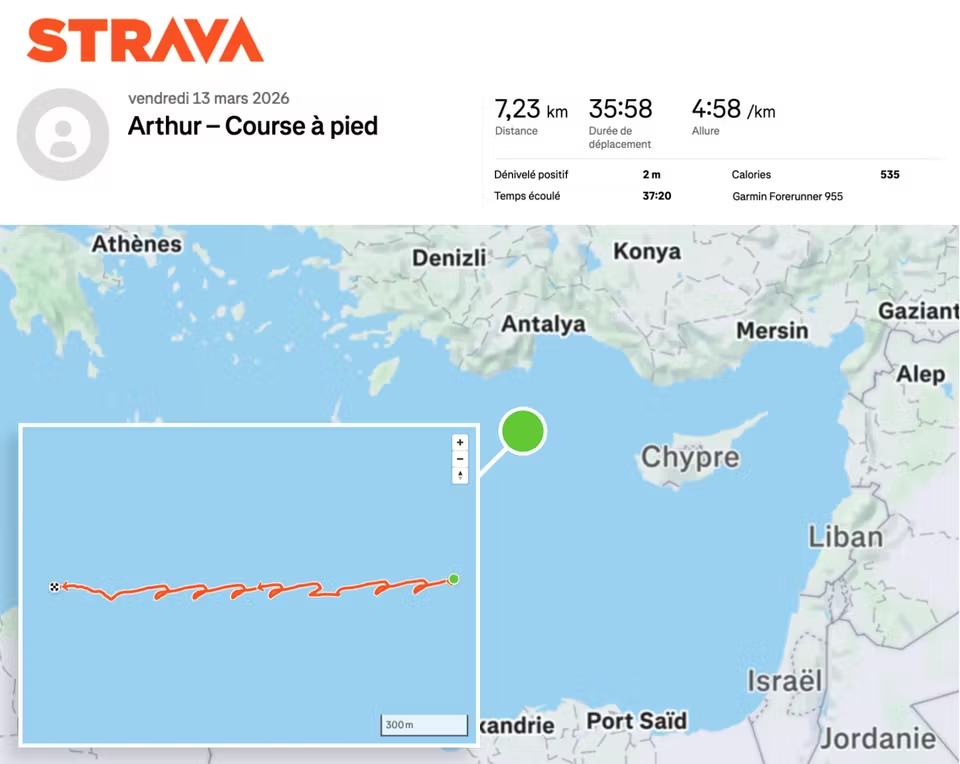
GTIG tracked the use of the exploit in highly targeted attacks by a surveillance vendor’s customer, in Ukrainian watering hole campaigns by UNC6353, and later in broad-scale attacks by Chinese financial threat actor UNC6691, showing an active market for “second-hand” zero-day exploits. Multiple threat actors now reuse and adapt these advanced techniques for new vulnerabilities.
GTIG shared the findings to raise awareness and protect users, adding identified domains to Safe Browsing.
Initial discovery occurred in February 2025 when GTIG captured a previously unseen JavaScript framework delivering an iOS exploit chain from a surveillance vendor’s customer.
“In February 2025, we captured parts of an iOS exploit chain used by a customer of a surveillance company.” reads the report published by GTIG. “The exploits were integrated into a previously unseen JavaScript framework that used simple but unique JavaScript obfuscation techniques.”
“The core technical value of this exploit kit lies in its comprehensive collection of iOS exploits, with the most advanced ones using non-public exploitation techniques and mitigation bypasses.”

The framework uses fingerprinting to detect device type and iOS version, then loads the appropriate WebKit RCE exploit and pointer authentication bypass. One recovered exploit, CVE-2024-23222, was later patched in iOS 17.3.
Government-backed attackers used the same framework in Ukrainian watering hole attacks, delivering multiple RCE exploits to select iPhone users. Later, Chinese scam websites deployed the full Coruna kit, dropping the same exploits via hidden iFrames on fake financial and crypto sites. GTIG collected hundreds of samples covering all five exploit chains and observed debug versions exposing internal exploit names, confirming the kit’s internal name as Coruna.
The Coruna exploit kit relies on a highly engineered framework that links all components through shared utilities and custom loaders. It avoids devices in Lockdown Mode or private browsing, derives resource URLs from a hard-coded cookie, and delivers WebKit RCE and PAC bypasses in clear form. After exploitation, a binary loader deploys encrypted, compressed payloads disguised as .min.js files, tailored to specific chips and iOS versions. In total, the kit includes 23 exploits covering iOS 13 through 17.2.1, with advanced mitigation bypasses and reusable modules for defeating memory and kernel protections.
At the end of the chain, a stager called PlasmaLoader injects into a root daemon and deploys a financially focused payload.
The malware scans for crypto wallets, backup phrases, and banking data, exfiltrating sensitive information and loading additional modules from command-and-control servers. It targets numerous cryptocurrency apps, uses encrypted communications, and falls back on a custom domain generation algorithm seeded with “lazarus” to maintain persistence.
Google published Indicators of Compromise (IOCs) and Yara rules for this exploit.
Recently, Lookout Threat Labs discovered a new iOS exploit kit called DarkSword that has been used since late 2025 by multiple threat actors, including surveillance vendors and likely nation-state actors. The toolkit enables full-chain attacks to steal sensitive data from Apple devices and has been observed in campaigns targeting countries such as Saudi Arabia, Turkey, Malaysia, and Ukraine.
The exploit chain relies on six vulnerabilities, three used as zero-days, to achieve full device compromise:
- CVE-2025-31277 – JavaScriptCore memory corruption (CVSS: 8.8)
- CVE-2026-20700 – dyld PAC bypass (CVSS: 8.6) (zero-day)
- CVE-2025-43529 – JavaScriptCore memory corruption (CVSS: 8.8) (zero-day)
- CVE-2025-14174 – ANGLE memory corruption (CVSS: 8.8) (zero-day)
- CVE-2025-43510 – iOS kernel memory issue (CVSS: 8.6)
- CVE-2025-43520 – iOS kernel memory corruption (CVSS: 8.6)
Together, these flaws enable full-chain exploitation and complete control of targeted iOS devices.
DarkSword targets iPhones running iOS 18.4–18.7 and has been used by the suspected Russian-linked group UNC6353 against Ukrainian targets. It allows attackers to steal sensitive data, including credentials and crypto wallet information, then quickly exfiltrates it in a “hit-and-run” approach before cleaning traces.
The exploits appear to be linked to Coruna exploits, DarkSword enables near full device access with minimal user interaction, showing how advanced exploits are now available on a secondary market to a wider range of threat actors.
“DarkSword aims to extract an extensive set of personal information including credentials from the device and specifically targets a plethora of crypto wallet apps, hinting at a financially motivated threat actor.” reads the report published by Lookout. “Notably, DarkSword appears to take a “hit-and-run” approach by collecting and exfiltrating the targeted data from the device within seconds or at most minutes followed by cleanup.”
Researchers investigating Coruna uncovered related infrastructure linked to Russian actor UNC6353, including a similar domain used in attacks on compromised Ukrainian sites, even government ones. Malicious iframes loaded scripts to fingerprint devices and target specific iOS versions. Further analysis revealed a new exploit chain, later named DarkSword, discovered in late 2025 through joint research by Lookout, iVerify, and Google, confirming a distinct and evolving threat.
While it initially appeared that this may be another site distributing Coruna, upon closer inspection of the our researchers found that the iframe loads a javascript file called rce_loader.js, which is largely responsible for fingerprinting devices visiting the compromised site in order to determine whether to route the devices to the iOS exploit chain. However, the script was looking for iOS devices with OS versions 18.4 or 18.6.2, which are iOS versions that are not susceptible to the exploit chains used in Coruna.

Recognizing that this was a new threat, our researchers analyzed the code and began capturing all of the stages of the exploits.
According to Lookout, the actor behind the exploit, UNC6353, remains a largely unknown group but has used advanced iOS exploit chains in watering hole attacks on Ukrainian websites. Likely well-funded, it appears to rely on third-party or brokered exploits, possibly linked to Russian ecosystems. The group targets both intelligence and financial data, including crypto assets, suggesting dual motives.
Its infrastructure is limited but shows deep access to compromised sites. Poor obfuscation and signs of AI-assisted code suggest limited in-house expertise. Overall, UNC6353 is assessed as a capable yet not highly sophisticated actor, potentially a Russia-aligned proxy blending espionage with cybercrime.
Google GTIG experts found multiple actors using DarkSword since November 2025, and believes other surveillance vendors or threat groups are likely using the exploit chain as well.

“The use of both DarkSword and Coruna by a variety of actors demonstrates the ongoing risk of exploit proliferation across actors of varying geography and motivation.” concludes GTIG.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, exploit kits)