Vibe Hacking: Two AI-Augmented Campaigns Target Government and Financial Sectors in Latin America
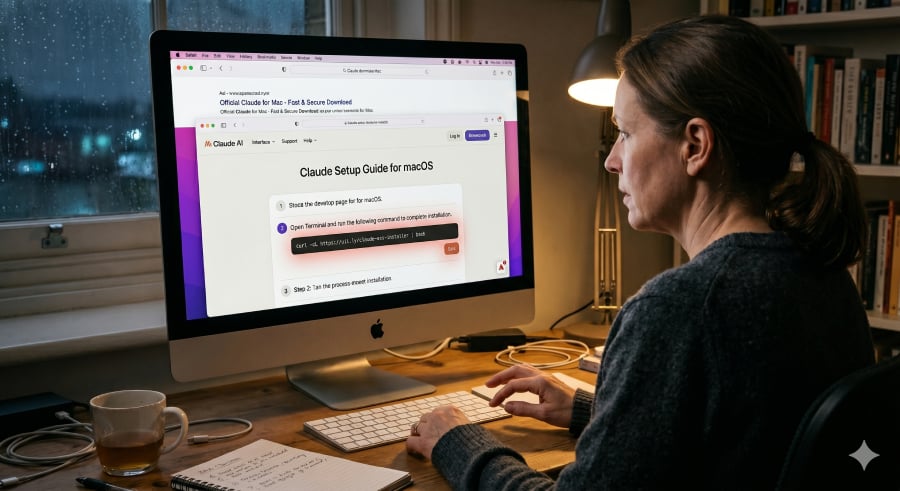
The server-side controllers for these tools were both implemented as Python-based servers. The Python source code contained comprehensive comments, structured error handling, and clear evidence of iterative development, leading us to assess that the campaign likely also used vibe coding in developing these tools.
Observations and security implications
The SHADOW-AETHER-040 and SHADOW-AETHER-064 cases demonstrate how the threat actors used agentic AI to support their malicious operations. By employing AI agents in their offensive operations, actors were not only able to automate tasks that previously required manual execution, but also demonstrated the advantages of generative AI technologies in some areas.
First, AI agents were able to rapidly analyze source code, configuration files, and log data to identify misconfigurations or exposed information such as the internal IP addresses, usernames, and even embedded credentials. Historically, this type of task would have required manual review and time-intensive analysis. With AI support, it can now be completed almost immediately. Any small oversight can be identified and weaponized quickly by AI-driven threat actors.
Second, AI agents were able to dynamically generate commands and scripts on demand. Rather than relying on an arsenal of previously developed hacking tools, AI agents in these campaigns directly generated the commands and scripts required to complete each task. These included malicious activities such as internal network scanning, password spraying, and vulnerability exploitation. Once the underlying logic of the attack is established, the AI agent could immediately produce complex commands or scripts to execute it without old tooling. Because these dynamically generated commands, scripts, and code differ with each execution, they effectively replace open-source hacking tools that are more likely to be detected, reducing the possibility of detection by traditional security solutions.
Conclusion
Using AI agents to execute parallel attack operations enhances threat actors’ efficiency. However, the adoption of agentic AI does not mean that attackers can successfully compromise every environment. We observed some cases in which the actors still ultimately failed even with the help of an AI agent because it could not identify any feasible path for lateral movement. In those cases, the targeted victims maintained strong security configurations, which prevented further compromise and limited the potential of additional damage.
As we have observed a growing number of attacks leveraging agentic AI in recent months, foundational defensive measures have become more critical than ever. It is worth noting that while AI agents can accelerate attacks, they cannot conjure vulnerabilities and misconfigurations. Against an environment with strong security fundamentals, even AI-augmented campaigns will struggle to find a way through. Timely patching, properly implemented zero-trust access controls, and comprehensive monitoring of environmental activity will be increasingly important in defending against this evolving threat landscape.
TrendAI™ Research will continue tracking SHADOW-AETHER-040, SHADOW-AETHER-064, and related campaigns, delivering actionable intelligence to help organizations stay ahead of emerging threats. Our threat intelligence, paired with advanced detection capabilities, helps keep your organization protected against sophisticated AI-assisted attacks targeting government entities, financial institutions, and other critical sectors.
TrendAI Vision One™ customers are protected from the IoCs listed in the table below.
MITRE ATT&CK techniques of SHADOW-AETHER-040