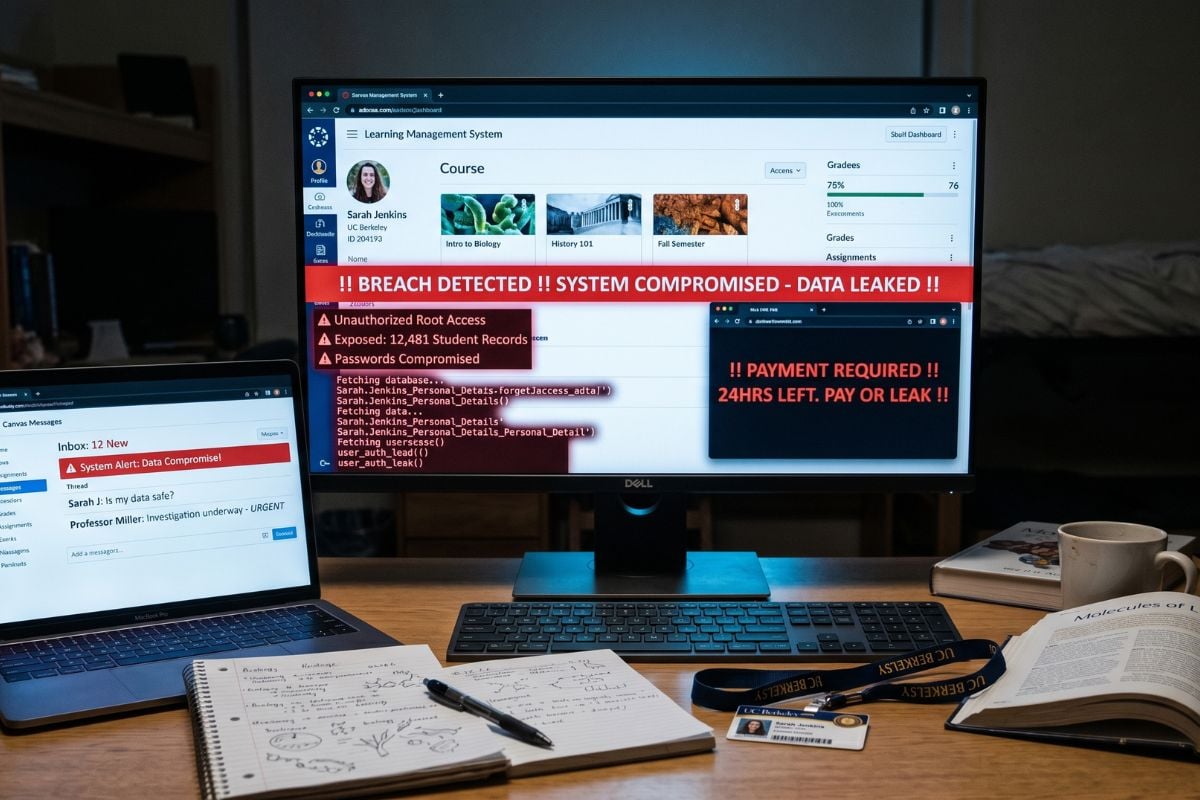
Canvas Breach May Put 275M Users, 9,000 Schools at Risk
A classroom platform built for homework, grades, and student messages is now at the center of a high-stakes extortion claim.
Instructure has confirmed a cybersecurity incident involving some Canvas LMS user information and messages, though its investigation is still ongoing. The confirmation follows claims from ShinyHunters that data tied to 275 million users and nearly 9,000 schools was stolen, a scale that Instructure has not publicly verified.
The most sensitive question now is not just how many users were affected, but what kinds of school communications may have been exposed.
Pay or leak
ShinyHunters gave Instructure a deadline and a threat: “FINAL WARNING PAY OR LEAK.” In the listing, the group claimed the stolen data includes PII connected to students, teachers, and staff, plus “several billions of private messages” exchanged by Canvas users.
The group listed the archive at “3.65TB+ (uncompressed)” and alleged that Instructure’s Salesforce instance was also breached. Instructure has not publicly confirmed the Salesforce claim or the scale of the alleged data theft.
The private-message claim adds a more sensitive category of data to the alleged breach. Names, emails, and student IDs identify users, but Canvas messages could reveal how students and teachers communicate during the school day, from assignment questions and feedback to academic concerns or extension requests.
Instructure confirms data exposure
Instructure’s public updates confirm a breach, but stop short of the scale claimed by ShinyHunters.
Steve Proud, Instructure’s chief information security officer, said the company “recently experienced a cybersecurity incident perpetrated by a criminal threat actor” and brought in outside forensics experts to investigate.
A later update said the incident had been contained and confirmed that some user information and messages were involved.
Instructure also reported “no evidence” that passwords, dates of birth, government identifiers or financial information were involved, adding that impacted institutions would be notified if that changes.
Must-read security coverage
A recent run of big-name breach claims
ShinyHunters has spent 2026 attaching its name to a string of high-profile data claims across finance, food, education, travel, and home security. Its recent playbook has leaned on stolen records, leak-site pressure, disputed victim counts, and public threats to release data.
At fintech lender Figure, the group claimed a social-engineering breach tied to 967,200 exposed email records. It also claimed a Panera Bread breach involving 14 million customer records, allegedly obtained through Microsoft single sign-on access, though Panera had not confirmed the breach in the uploaded source.
Education technology has already appeared in that run. McGraw-Hill confirmed unauthorized access tied to a Salesforce misconfiguration, while hackers claimed to have accessed 45 million Salesforce records. The company disputed that scale and said its findings showed limited, non-sensitive exposure.
The pattern continued with Amtrak and ADT. Amtrak’s breach involved at least 2.1 million customer records after CRM access, while ADT confirmed customer data exposure in an incident breach analysis tied to 5.5 million people, employee SSO, Okta vishing and Salesforce exfiltration.
Microsoft flagged 8.3 billion phishing emails in Q1 as attackers leaned on more evasive tactics.