A Mini Shai-Hulud Targeting the SAP Ecosystem
The post A Mini Shai-Hulud Targeting the SAP Ecosystem appeared first on GitGuardian Blog – Take Control of Your Secrets Security.
This attack is still active. Repository count grew from 847 to 1,006 while writing this analysis.
![[un]prompted 2026 – Total Recon: How We Discovered 1000s Of Open Agents In The Wild](https://securityboulevard.com/wp-content/uploads/2018/01/TwitterLogo-002.jpg)
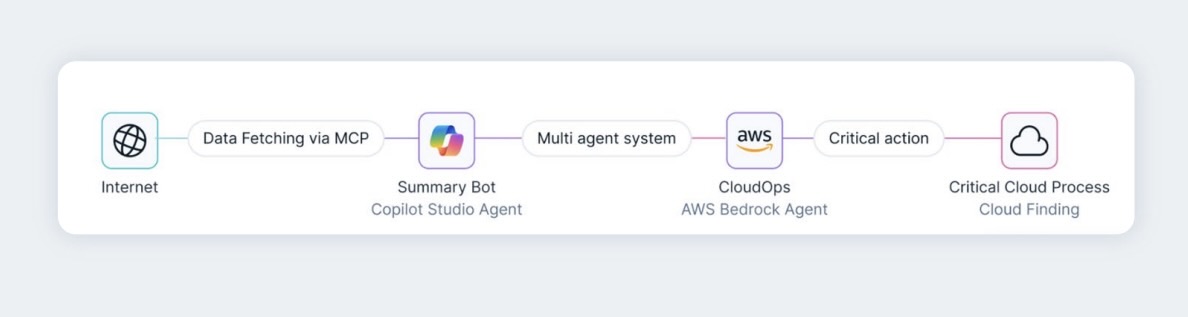
[un]prompted 2026 – Total Recon: How We Discovered 1000s Of Open Agents In The Wild
The post A Mini Shai-Hulud Targeting the SAP Ecosystem appeared first on GitGuardian Blog – Take Control of Your Secrets Security.
This attack is still active. Repository count grew from 847 to 1,006 while writing this analysis. We expect it to keep on growing in the next few hours.
Earlier today, Aikido researchers detected multiple compromised Node.js packages in SAP’s namespace today. The malware adapts to CI environments, steals GitHub personal access tokens, and uses them to self-propagate—a pattern consistent with recent supply-chain attacks.
How it works
Credential harvesting: The payload reads CI environment variables and adjusts its behavior accordingly.
Token exfiltration: If a GitHub personal access token (ghp_) is found locally, the malware exfiltrates encrypted secrets to the corresponding GitHub account.
Fallback mechanism: If no token is present, the malware scans commit messages for the string ‘OhNoWhatsGoingOnWithGitHub:’, then decodes a double-base64-encoded payload hidden inside, and uses it to exfiltrate the encrypted secrets to this account.
The RSA keys used to encrypt the exfiltrated secrets are the same as the ones used last week in the @bitwarden/cli attack.
Exfiltration infrastructure
GitGuardian identified 7 commits containing exposed ghp_ tokens—all remain valid and active at 16h46 EST. The attacker used the stolen tokens to create public repositories, each named with Dune-themed keywords. Inside each repository:
A README.md file containing the string “A Mini Shai-Hulud has Appeared”
A results/ directory with a JSON file holding the encrypted payload, protected by a 4096-bit RSA key
Our telemetry shows the attack’s full scope:
23 GitHub accounts used for exfiltration
971 public repositories created with stolen tokens
Top 6 accounts created 936 repos (96%) — these are the accounts tied to the 7 compromised tokens
*** This is a Security Bloggers Network syndicated blog from GitGuardian Blog – Take Control of Your Secrets Security authored by Guillaume Valadon. Read the original post at: https://blog.gitguardian.com/a-mini-shai-hulud-targeting-the-sap-ecosystem/