Linux
routers
in
Japan
are
the
target
of
a
new
Golang
remote
access
trojan
(RAT)
called
GobRAT.
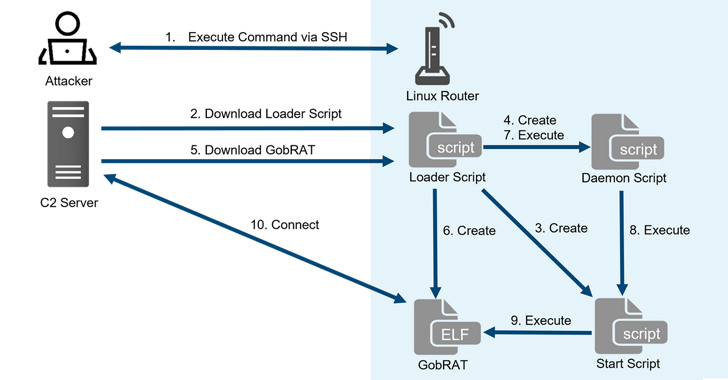
“Initially,
the
attacker
targets
a
router
whose
WEBUI
is
open
to
the
public,
executes
scripts
possibly
by
using
vulnerabilities,
and
finally
infects
the
GobRAT,”
the
JPCERT
Coordination
Center
(JPCERT/CC)
said
in
a
report
published
today.
The
compromise
of
an
internet-exposed
router
is
followed
by
the
deployment
of
a
loader
script
that
acts
as
a
conduit
for
delivering
GobRAT,
which,
when
launched,
masquerades
as
the
Apache
daemon
process
(apached)
to
evade
detection.
The
loader
is
also
equipped
to
disable
firewalls,
establish
persistence
using
the
cron
job
scheduler,
and
register
an
SSH
public
key
in
the
.ssh/authorized_keys
file
for
remote
access.
GobRAT,
for
its
part,
communicates
with
a
remote
server
via
the
Transport
Layer
Security
(TLS)
protocol
to
receive
as
many
as
22
different
encrypted
commands
for
execution.
Some
of
the
major
commands
are
as
follows
–
-
Obtain
machine
information -
Execute
reverse
shell -
Read/write
files -
Configure
new
command-and-control
(C2)
and
protocol -
Start
SOCKS5
proxy -
Execute
file
in
/zone/frpc,
and -
Attempt
to
login
to
sshd,
Telnet,
Redis,
MySQL,
PostgreSQL
services
running
on
another
machine
The
findings
come
nearly
three
months
after
Lumen
Black
Lotus
Labs
revealed
that
business-grade
routers
have
been
victimized
to
spy
on
victims
in
Latin
America,
Europe,
and
North
America
using
a
malware
called
HiatusRAT.