The Emails Hitting K-12 Right Now
I’m heading to the National K-12 Cybersecurity Leadership Conference in Albuquerque this week.
The Emails Hitting K-12 Right Now
I’m heading to the National K-12 Cybersecurity Leadership Conference in Albuquerque this week. It’s the kind of event where IT directors, network admins, and technology coordinators gather to compare notes on what’s actually hitting their districts (not theoretical threats, but the emails that landed in inboxes last Tuesday).
I’ve spent the past several months deep in education-specific threat data, studying real phishing campaigns that target schools. And the conversations I’m most looking forward to this week aren’t about technology. They’re about what’s actually hitting their districts (and whether what we’re seeing in the data matches what they’re living every day).
Here’s what I expect to hear.
“We Almost Wired $1.6 Million to the Wrong Account”
Vendor payment fraud remains the single most expensive attack type in education. And it’s because the emails are genuinely that good.
Butte School District in Montana lost $1.1 million when attackers impersonated their construction contractor. The FBI called it a “highly sophisticated social engineering attack.” Calcasieu Parish School Board in Louisiana lost $1.6 million across seven payments over six months. The Louisiana Legislative Auditor found that staff updated vendor records based solely on email requests, no phone verification.
These aren’t edge cases.
Manor ISD in Texas lost $2.3 million
Scott County Schools in Kentucky lost $3.7 million (thankfully recovered)
Portland Public Schools caught a $2.9 million attempt just in time.
The pattern is always the same… an email that looks exactly like it came from a trusted vendor, requesting a change to payment routing. Finance staff comply because the email matches what they expect.
No malicious links.
No attachments.
Just social engineering that exploits established trust.
I want to ask every IT director I meet this week: Have you changed how your district handles vendor payment requests since these stories broke? Because the answer tells me everything about where they are in their security journey.
“Someone Stole a Teacher’s Paycheck”
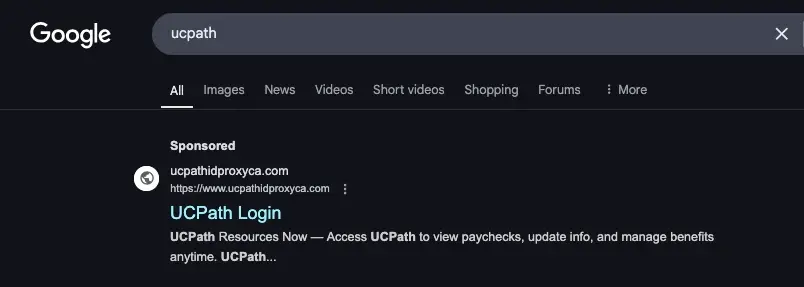
Payroll redirect attacks are hitting education hard, and they’re more sophisticated than most people realize. These aren’t single-vector attacks. The campaign UC Berkeley documented used four simultaneous vectors: phishing emails, text messages impersonating the help desk, sponsored Google Ads pointing to fake payroll portals, and fake terms-and-conditions pages.
A fake UCPath payroll portal designed to harvest employee credentials
The URLs are crafted to look legitimate, something like fake-domain.com/auth.berkeley.edu where the real institutional domain appears at the end of the URL, after the attacker’s domain. It’s subtle. And for a teacher who just wants to check their pay stub, the difference between that and a real URL isn’t obvious.
One variant even came from a compromised Austin ISD email address, which means it sailed right past any filter checking whether the sender was from a .edu domain.
A text message phishing attempt asking for multi-factor authentication codes
Here’s the thing I hope to reinforce at the conference: help desks never initiate contact via text to personal cell phones. No technician will ever ask for passwords or MFA codes via email or text. If your staff knows nothing else about phishing, knowing this one fact would prevent a meaningful percentage of successful attacks.
“Our Teachers Can’t Tell the Fake HR Emails from the Real Ones”
This one’s personal for IT teams because it directly affects their colleagues. Fake benefits enrollment, salary increase notifications, compensation statements – these campaigns time themselves to when employees are actually expecting HR communications.
A fraudulent salary notification email targeting university staff
Brown University caught a fake open enrollment campaign sent from [email protected] (not a Brown address) with an HTML attachment called Benefits_Enrollment.htm. It had conflicting deadlines in the same message (June 27 and July 10) and arrived at the wrong time of year for actual enrollment. But how many employees actually notice those details when they’re worried about their benefits?
UC Berkeley documented a wave of fake “$2,250 Financial Support Program” emails and salary increase notifications, all linking to credential harvesting pages disguised as institutional login portals.
A fake financial support program email designed to harvest credentials
The reason these work is simple: teachers and staff routinely receive legitimate HR emails that require action. Attackers just blend in.
What I Want to Talk About in Albuquerque
The MS-ISAC’s 2025 K-12 Cybersecurity Assessment Report (the most comprehensive study of its kind) found that 82% of K-12 organizations experienced cyber incidents over an 18-month period. And 86% of those districts are defending themselves with fewer than five security staff.
That’s the impossible math of K-12 cybersecurity: massive attack surfaces, skeleton crews, and adversaries who know your calendar better than you do.
The IT directors I’ll meet this week aren’t behind because they’re incompetent. They’re behind because the math doesn’t work. They’re resourceful, pragmatic people who’ve learned to do a lot with a little. I respect that.
But the attacks targeting education aren’t getting simpler. They’re getting more personalized, more multi-channel, and more precisely timed. Vendor fraud during construction season. Fake assessments during review cycles. Benefits scams during open enrollment. The attackers study the academic calendar the way a quarterback studies film.
So…the conversation I want to have isn’t “here’s what you should be afraid of.” These people are afraid enough.
The conversation I want to have is: What would change if your email security actually understood education?
If it recognized that a “salary increase notification” arriving from a non-institutional domain during the wrong pay cycle is almost certainly a credential harvesting attempt. If it could pull a malicious email from 100 inboxes simultaneously, in seconds, without your 3-person team touching it.
That’s the conversation worth having. And I’m looking forward to it.
If you’re at the National K-12 Cybersecurity Leadership Conference this week, come find me. I’d love to hear what’s hitting your district, and whether it matches what we’re seeing in the data.
You can also explore how IRONSCALES protects education at https://ironscales.com/solutions/education-email-security.
*** This is a Security Bloggers Network syndicated blog from Blog authored by Audian Paxson. Read the original post at: https://ironscales.com/blog/the-emails-hitting-k-12-right-now




.png?width=1062&height=466&name=image%20(2).png)
