Supply Chain Attacks Surge in March 2026
IntroductionThere was a significant increase in software supply chain attacks in March 2026.

How reliable are NHIs in identity management
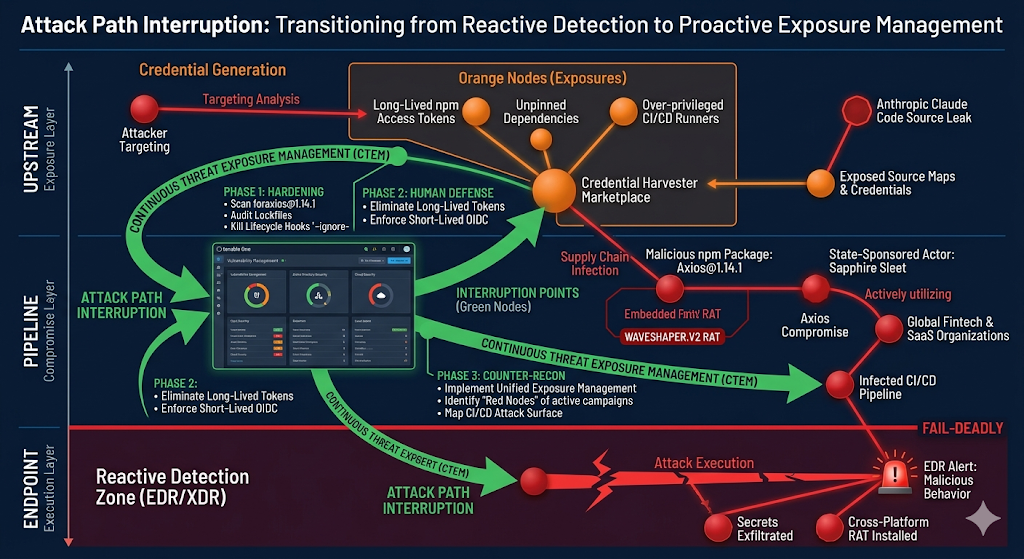
IntroductionThere was a significant increase in software supply chain attacks in March 2026. There were five major software supply-chain attacks that occurred including the Axios NPM package compromise, which has been attributed to a North Korean threat actor. In addition, a hacking group known as TeamPCP was able to compromise Trivy (a vulnerability scanner), KICS (a static analysis tool), LiteLLM (an interface for AI models), and Telnyx (a library for real-time communication features).In this blog, we cover two of these supply chain attacks, which are significant given the scale and popularity of these packages.Axios NPM Package Compromised to Distribute Cross-Platform RATSummaryOn March 30, 2026, security researchers discovered that the widely-used NPM package Axios was compromised through an account takeover attack targeting a lead maintainer. Threat actors bypassed the project’s GitHub Actions CI/CD pipeline by compromising the maintainer’s NPM account and changing its associated email. The threat actor manually published two malicious versions via NPM CLI.These poisoned releases inject a hidden dependency called [email protected], which executes a postinstall script functioning as a cross-platform Remote Access Trojan (RAT) dropper targeting macOS, Windows, and Linux systems.During execution, the malware contacts command-and-control (C2) infrastructure at sfrclak[.]com to deliver platform-specific payloads, then deletes itself and replaces its package.json with a clean version to evade detection.RecommendationsReview package.json, package-lock.json, and yarn.lock files for [email protected], [email protected], or [email protected]. Remove any compromised packages, clear caches, and reinstall clean ones.Downgrade to [email protected] (for 1.x users) or [email protected] (for 0.x users) and update lockfiles.Search for connections to sfrclak[.]com or 142.11.206[.]73 from developer workstations and CI/CD systems.Use private registry proxies and Software Composition Analysis (SCA) tools to filter and monitor third-party packages.Restrict open-source package consumption on corporate devices and CI systems to enterprise-open source package managers. Use Zscaler Internet Access controls to block access to internet package managers from corporate devices. Use native controls and Zscaler Private App Connectors to block access to internet package managers from CI systems.Apply lockfiles strictly (e.g., package-lock.json, pnpm-lock.yaml) and use npm ci instead of npm install.Reduce dependency surface by auditing and removing unused packages.Apply least privilege principles using scoped, short-lived keys and tokens.Revoke NPM tokens, GitHub PATs, cloud keys, and CI/CD secrets.Enable phishing-resistant multifactor authentication (MFA) on NPM, GitHub, and cloud platforms.Flag abnormal NPM publishes, unexpected GitHub workflow additions, or secret scanner usage in CI.Treat impacted systems as compromised by isolating, scanning, or reimaging them.Update response playbooks for supply chain attacks and run practice drills.Restrict build environments to internal package managers or trusted mirrors, and limit internet access to reduce exfiltration risk.Reinforce the secure handling of tokens and secrets, and train teams on phishing awareness and supply chain security best practices.Enforce a release cooldown period to ensure users can’t check out newly released packages, stopping emerging supply chain attacks.Affected packages and versionsThe following packages are impacted by this compromise.Package VersionAxios1.14.1Axios0.30.4Table 1: Axios package versions impacted by the compromise.How it worksAll NPM packages include a package.json file that declares dependencies. In the compromised version of Axios, the threat actor added a dependency for a malicious package called plain-crypto-js, which included a postinstall script that ran a setup.js script via node.When developers or CI pipelines run npm install [email protected], NPM resolves the dependency tree, downloads [email protected], and runs the postinstall script. Running node setup.js triggers the compromise sequence.Attack chainThe figure below shows the attack chain.Figure 1: Attack chain for the compromised Axios package.TeamPCP Supply Chain Attack Targets LiteLLM on PyPISummarySummaryOn March 26, 2026, a supply chain attack was uncovered targeting LiteLLM, a popular AI infrastructure library hosted on PyPI with roughly 3.4 million downloads per day. Two LiteLLM package versions were found to include malicious code published by a threat group called TeamPCP. TeamPCP has been associated with multiple recent supply chain attacks such as KICS, Telnyx, and an attack on Aqua Security’s Trivy. The impacted package versions of LiteLLM were only available in PyPI for about three hours before they were quarantined.The poisoned LiteLLM packages appear to be part of an attack designed to harvest high-value secrets such as AWS, GCP, and Azure tokens, SSH keys, and Kubernetes credentials, enabling lateral movement and long-term persistence across compromised CI/CD systems and production environments. RecommendationsRotate or revoke all potentially exposed secrets such as PyPI tokens, API keys, SSH keys, and cloud credentials. Remove unused secrets, and restrict access to sensitive stores and configuration files (for example, .env files, SSH keys, and cloud CLI configs) using least-privilege controls and strict filesystem or secret-store permissions.Closely monitor PyPI publishing activity and recent release history, limit and regularly review maintainer access, and enforce MFA for all maintainers. Strengthen dependency integrity by prioritizing review of Git diffs for dependency version changes to spot suspicious modifications, and implement alerting for any unexpected direct or transitive dependency updates. Verify hashes and signatures where supported.Restrict who or what can run builds and publish artifacts, eliminate plaintext secrets in pipelines, and move to secret managers plus short-lived and ephemeral tokens. Add protected branches and tags, mandatory reviews for release workflows, and limit runner and network permissions.Apply least-privilege Identity and Access Management (IAM), tighten Kubernetes Role-Based Access Control (RBAC), and reduce credential exposure paths. Ensure container and runtime policies prevent credential harvesting and restrict workload identity access to only the required resources.Affected versions and deliveryThe following versions of LiteLLM were impacted. Users should upgrade to version 1.82.6 (the last known clean version).VersionDelivery1.82.8This version introduced a .pth file (litellm_init.pth) added to site-packages/. Python automatically executes code within .pth files during startup, meaning the malicious payload triggers on any Python invocation on the host, even if LiteLLM itself is not imported. The .pth file is correctly recorded in the wheel’s RECORD, so pip’s hash verification and other integrity checks still pass because the malicious content was published with legitimate credentials rather than injected afterward.1.82.7This version introduced an obfuscated Base64-encoded payload within proxy_server.py. This payload is designed to execute immediately upon the library being imported.Table 2: LiteLLM package versions affected and their corresponding delivery mechanism.How it worksLiteLLM is a wrapper or proxy for AI models that lets developers call different LLMs using an OpenAI-style API. Since it’s published on PyPI, a developer might download it by installing it for a project with the standard Python package installer, either directly or as part of an automated dependency install. Attack chainThe attack chain for the compromised packages is shown below.Figure 2: Attack chain for compromised LiteLLM packages.ConclusionThese supply chain threats highlight the fragility of the global software supply chain, especially with respect to open source software. ThreatLabz encourages readers to review the recommendations in this blog to help protect against these kinds of threats and minimize their impacts. Zscaler CoverageZscaler has added coverage for the threats associated with these campaigns, ensuring that any attempts to download a compromised package will be detected with the following threat names.For AxiosAdvanced Threat ProtectionJS.Malicious.npmpackagePS.RAT.npmpackagePython.RAT.npmpackageOSX.RAT.npmpackageFor LiteLLMAdvanced Threat ProtectionLiteLLM-ZABTrojan.SKMGPython.Trojan.LiteLLMIndicators Of Compromise (IOCs)For AxiosPackageVersionHashaxios0.30.4e56bafda15a624b60ac967111d227bf8axios1.14.121d2470cae072cf2d027d473d168158cplain-crypto-js4.2.052f3311ceb5495796e9bed22302d79bcplain-crypto-js4.2.1db7f4c82c732e8b107492cae419740ab@shadanai/openclaw2026.3.31-11b8615b9732833b4dd0a3e82326982fa@qqbrowser/openclaw-qbot0.0.130759e597c3cc23c04cd39301bd93fc79fsetup.js-7658962ae060a222c0058cd4e979bfa1osx script-7a9ddef00f69477b96252ca234fcbeebpython script-9663665850cdd8fe12e30a671e5c4e6fpowershell script-04e3073b3cd5c5bfcde6f575ecf6e8c1system.bat-089e2872016f75a5223b5e02c184dfec For LiteLLMFile hashesMD5 HashNamecde4951bee7e28ac8a29d33d34a41ae5litellm_init.pthf5560871f6002982a6a2cc0b3ee739f7proxy_server.py7cac57b2d328bd814009772dd1eda429p.py85ed77a21b88cae721f369fa6b7bbba3LiteLLM v1.82.7 Package2e3a4412a7a487b32c5715167c755d08LiteLLM v1.82.8 PackageNetwork indicators IndicatorTypecheckmarx[.]zoneC2 pollingmodels[.]litellm[.]cloudExfiltration URL
*** This is a Security Bloggers Network syndicated blog from Security Research | Blog authored by ThreatLabz (Zscaler). Read the original post at: https://www.zscaler.com/blogs/security-research/supply-chain-attacks-surge-march-2026