Patch Alert: Microsoft Fixes Nearly 80 Bugs, Including Critical Office Flaws

Microsoft’s March Patch Tuesday has arrived, bringing nearly 80 fixes for everything from your Excel spreadsheets to the heart of corporate SQL servers.
While we dodged the chaos of active zero-day attacks this month, don’t let your guard down just yet. Microsoft has still rolled out a massive batch of updates to plug holes that could let strangers take over your PC or sneak a peek at your private files.
One of the biggest concerns this month isn’t a complex hack; it’s something as simple as looking at a file. Two major flaws in Microsoft Office (CVE-2026-26113 and CVE-2026-26110) allow hackers to run their own malicious code on your computer just by having you view a rigged document in the “Preview Pane.”
Jack Bicer, Director of Vulnerability Research at Action1, told TechRepublic that this is a high-priority issue.
“Notably, the Preview Pane can serve as an attack vector, meaning exploitation may occur simply by viewing a malicious file. When a simple document preview can trigger code execution, attackers gain a doorway directly into the system,” Bicer said.
Mike Walters, president and co-founder of Action1, echoed this warning when discussing the second Office flaw, telling TechRepublic:
“A single memory handling mistake inside Office can allow attackers to run their own code, turning an ordinary document into a potential system takeover… Even a single malicious document could compromise an endpoint and give attackers a foothold inside the organization.”
Excel and the AI risk
If you use Microsoft’s new AI tools, you’ll want to pay extra attention to a bug in Excel (CVE-2026-26144). This “information disclosure” flaw could allow an attacker to trick Excel, specifically its Copilot Agent mode, into leaking sensitive data across a network without you knowing.
Alex Vovk, CEO and Co-Founder of Action1, noted that such leaks are silent but deadly for businesses.
“Information disclosure vulnerabilities are especially dangerous in corporate environments where Excel files often contain financial data, intellectual property, or operational records. If exploited, attackers could silently extract confidential information from internal systems without triggering obvious alerts,” Vovk noted.
The public zero-days
Even though hackers weren’t using them yet, two flaws were publicly disclosed, meaning the blueprints for how to exploit them were already out in the open.
- CVE-2026-21262: A bug in SQL Server that lets someone with basic access quietly promote themselves to a sysadmin.
- CVE-2026-26127: A flaw in the .NET framework that could be used to remotely crash applications, effectively knocking services offline.
According to Bicer, although the overall number of patches is below the yearly average, it’s still a heavy lift for IT teams.
“This Patch Tuesday includes 78 vulnerability fixes from Microsoft, above last month’s 55 patches but below its 12-month moving average of 93, with three rated critical.” He told TechRepublic. “While there are no zero-day vulnerabilities reported this time, the number of patches and several critical issues mean it’s still an update worth prioritizing.”
AI helps with the discovery of a 9.8 threat
In a fascinating twist, the most severe bug of the month (rated a nearly perfect 9.8 out of 10 for danger) wasn’t found by a human. CVE-2026-21536, which affects the Microsoft Devices Pricing Program, was discovered by an autonomous AI agent called XBOW.
While Microsoft has already patched this one on its end, it marks a shift in the arms race between security researchers and hackers, showing that AI can now find complex holes in software entirely on its own.
What you should do
For most of us, the advice remains the same: head to your Windows Update settings and click “Check for updates.” If you can’t update your Office apps immediately, security experts suggest disabling the Preview Pane in your file explorer as a temporary shield against those malicious document attacks.
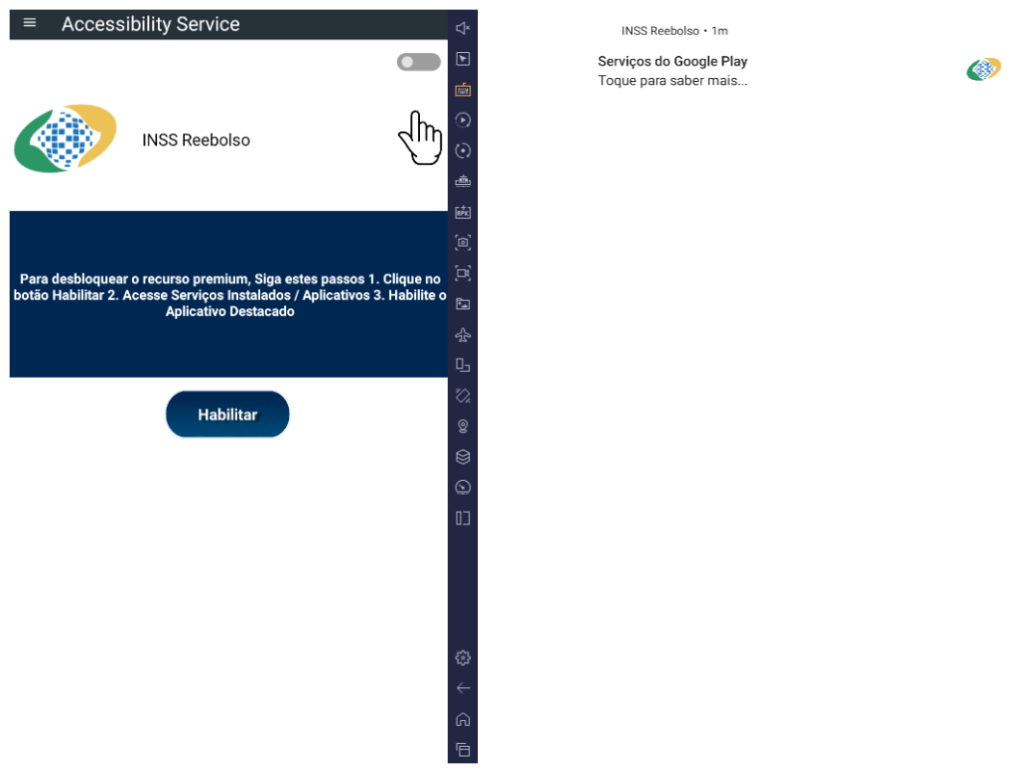
Also read: In another emerging threat, hackers are impersonating IT staff on Microsoft Teams to trick employees into installing malware and gain stealthy access to corporate networks.