Everyone Is Deploying AI Agents. Almost Nobody Knows What They’re Doing.
One constant I hear from CISOs I speak with is that AI agents are not coming. They are already inside organizations, reasoning through goals, selecting tools, and taking action through the same APIs that connect your most sensitive systems.
Everyone Is Deploying AI Agents. Almost Nobody Knows What They’re Doing.
One constant I hear from CISOs I speak with is that AI agents are not coming. They are already inside organizations, reasoning through goals, selecting tools, and taking action through the same APIs that connect your most sensitive systems.
And most security teams have no idea what those agents are doing.
The problem Is not just the model
The industry has fixated on prompts, jailbreaks, and LLM guardrails. Those matter. But they are only one layer of a much larger stack.
Think of an AI agent as a digital employee. The LLM is the brain, responsible for reasoning and decisions. MCP servers are the hands, connecting the agent to the services and tools it needs to operate. APIs are the action layer, the buttons and levers that allow agents to actually interact with your data, your infrastructure, and your workflows.
Most AI security stops at the brain. The hands and the action layer are left almost entirely unguarded.
Here is the consequence: every gateway, WAF, and proxy in your environment sits at the perimeter. But the vast majority of agentic traffic never crosses a boundary. It moves internally, agent to database, MCP server to workflow, service to service. Edge tools see roughly 20% of agentic API traffic. The other 80% is invisible to them.
We saw this exact vulnerability play out recently at McKinsey when an autonomous agent compromised an AI platform in under two hours, with no credentials and no humans in the loop. The action layer was the entry point. It always is.
Securing all three layers
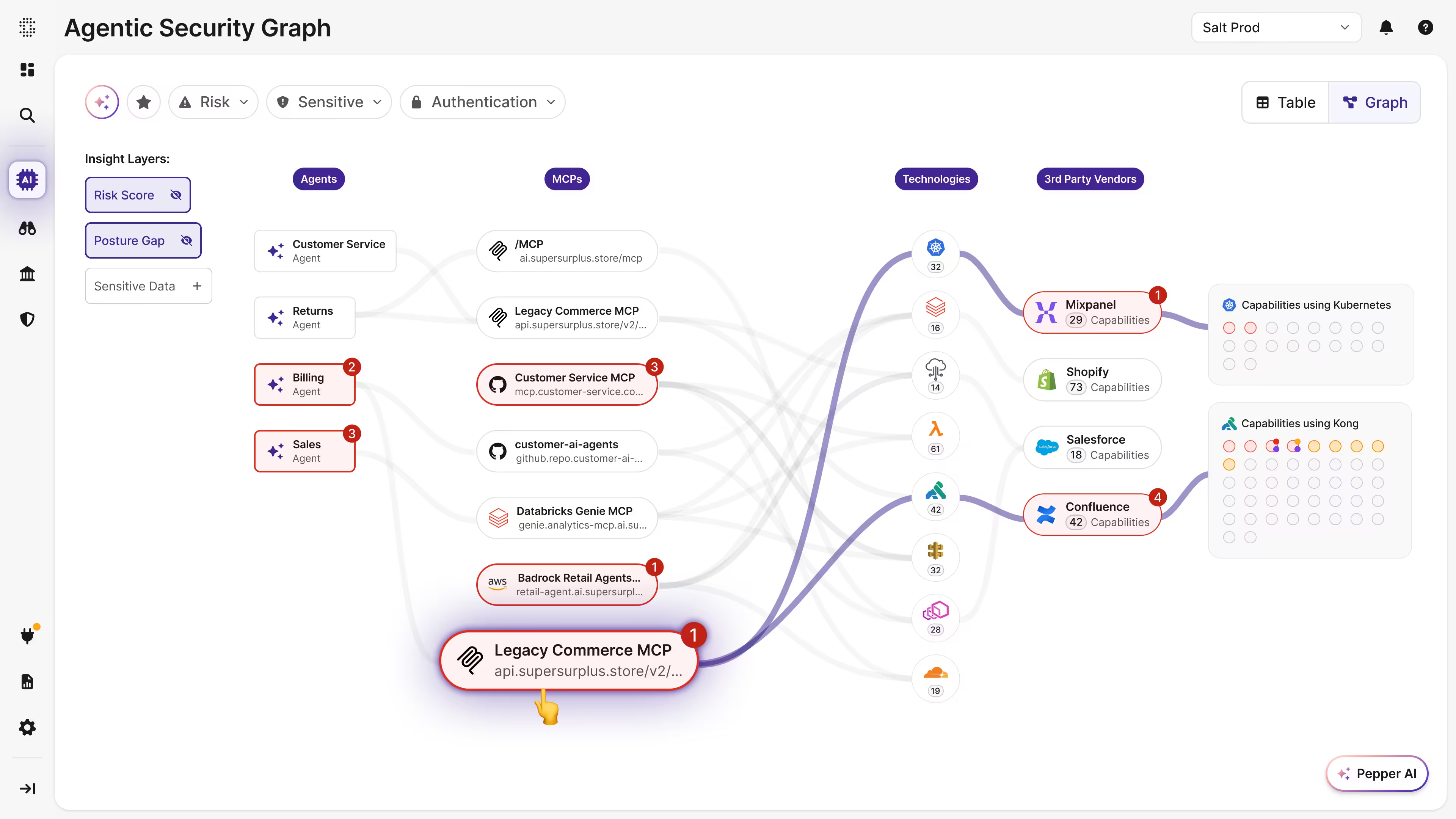
To secure the agentic enterprise, you need visibility across the entire stack: the LLMs making decisions, the MCP servers executing them, and the APIs carrying them out. Together, these form what we call the Agentic Security Graph, the full interconnected web through which agents reason, act, and interact with your enterprise.
Most vendors see one layer, maybe two. Salt sees all three, including the internal east-west traffic that edge tools miss entirely.
That means knowing which LLMs are connected to your enterprise and what they can access. It means mapping every MCP server, managed or shadow, and understanding what actions they enable. And it means continuous visibility into every API your agents can reach, from internal services to third-party connectors, from code to runtime.
But visibility alone is not enough. Salt also contextualizes risk across the entire graph. Not every agent carries the same risk. An agent that can read a public knowledge base is fundamentally different from one that can write to a production database, trigger financial transactions, or access customer records. By contextualizing risk across the Agentic Security Graph, Salt separates the agents that can cause real damage from those that cannot, so your security team knows exactly where to focus. That is the holistic view no other platform can give you.
The questions you should be asking
Stop asking only: is the model safe?
Start asking:
What agents, MCP servers and APIs exist in my environment?
Which MCP servers and APIs are internet exposed?
What actions can agents perform through MCP servers and APIs, and which are high risk?
What sensitive data can agents access through MCP servers and APIs?
What gaps, misconfigurations and vulnerabilities exist across my APIs and MCP servers?
If you don’t have clear answers, you are operating AI systems you do not fully understand.
Eight years building for this moment
Salt made a bet eight years ago that APIs would become the backbone of the modern enterprise, and that no one was securing them properly. We were right.
We did not plan to become The agentic security company. The world came to us. Because agents communicate through APIs, authenticate through APIs, and exfiltrate data through APIs. The deep API security foundation we built over nearly a decade turns out to be exactly what securing the full Agentic Security Graph requires.
No company has a deeper foundation in this space. No company can give you a more complete picture of your agentic attack surface.
The future of AI will not be defined only by how intelligent our systems become. It will be defined by how safely we allow them to act. Security should not be the thing that slows AI down. With the right foundation, it is the thing that makes scale possible.
Salt Security exists to make that possible.
Map Your Agentic Security Graph at RSA Conference. A limited number of sessions are available, revealing in minutes how LLMs, MCP servers, and APIs connect across your enterprise, including the traffic your current tools cannot see.
events.salt.security/rsacmeetings
Roey Eliyahu is Co-Founder and CEO of Salt Security.
*** This is a Security Bloggers Network syndicated blog from Salt Security blog authored by Roey Eliyahu. Read the original post at: https://salt.security/blog/everyone-is-deploying-ai-agents-almost-nobody-knows-what-theyre-doing