Common ecommerce security vulnerabilities and testing strategies
March 5, 2026
Adam King
Director
Ecommerce platforms represent one of the most consistently targeted areas of the modern digital estate.

Common ecommerce security vulnerabilities and testing strategies
March 5, 2026
Adam King
Director
Ecommerce platforms represent one of the most consistently targeted areas of the modern digital estate. They process payment data, store personal information, integrate with logistics and marketing systems, and underpin revenue for many large businesses. The combination of financial value and sensitive data makes ecommerce security vulnerabilities an attractive target for attackers.
From a security perspective, ecommerce environments are complex. Platforms often combine a customer facing web application, mobile and third-party integrations, applets and scripts for digital marketing, and a cloud infrastructure layer supporting databases, storage, and content delivery. Each layer introduces its own risks, therefore understanding ecommerce security vulnerabilities requires a view across the full stack.
This article outlines the types of weaknesses typically identified during a web application penetration test, API assessment, and cloud infrastructure review, and explains why a layered testing approach is essential.
Web application vulnerabilities in ecommerce platforms
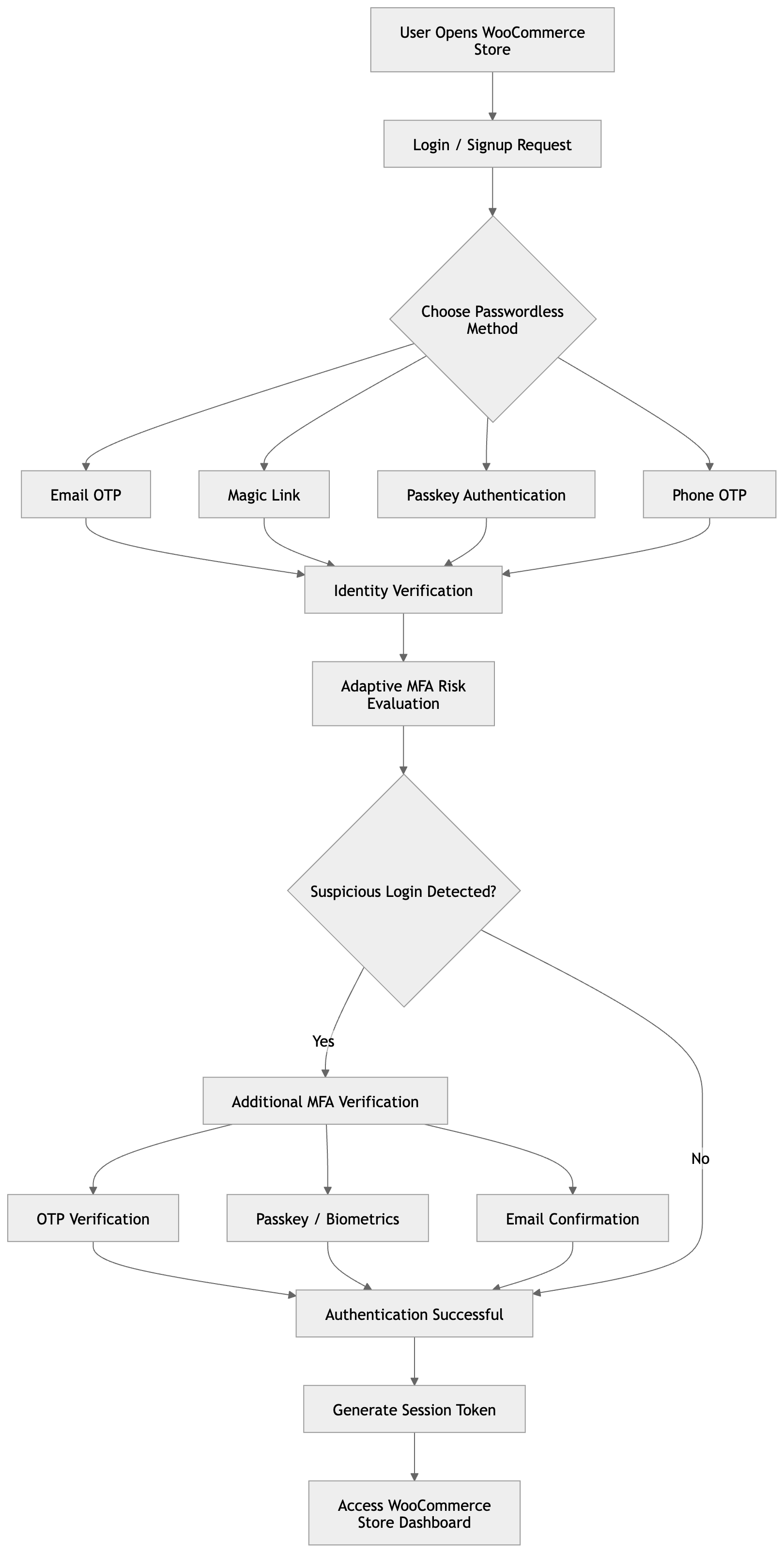
The web application layer remains the most visible part of an ecommerce platform. It handles account registration, authentication, product browsing, basket management, checkout workflows, and customer self service. These functions create a broad attack surface.
Access control weaknesses remain one of the most significant and widespread security vulnerabilities. Broken access controls can allow customers to access other users’ accounts, view order histories, or modify personal details. In more serious cases, weaknesses in user portals or administrative interfaces may enable privilege escalation providing access to sensitive actions. Even minor flaws in authorisation logic can have material impact where customer data and order processing are involved.
Business logic vulnerabilities are also common. Ecommerce applications implement complex pricing, discounting, and fulfilment rules. If these controls are not rigorously validated, attackers may manipulate parameters within checkout flows, abuse promotional codes, bypass purchase limits, or interfere with payment confirmation processes. These issues are rarely detected through automated scanning and typically require specialist testing to identify how workflows can be subverted.
Traditional injection vulnerabilities remain relevant. SQL injection, cross site scripting, and server-side request forgery continue to appear in bespoke functionality and poorly implemented integrations. In ecommerce contexts, such vulnerabilities can expose customer records, modify transactional data, or provide a foothold into backend systems.
Regular web application penetration testing is a key mechanism for identifying these issues before they are exploited in production environments.
Ecommerce API security weaknesses
Modern ecommerce platforms are heavily API driven. Single page applications, mobile apps, payment gateways, inventory systems, and external partners often communicate through REST or GraphQL APIs. While this architecture supports flexibility and scalability, it introduces additional exposure.
Broken object level authorisation is one of the most frequently observed API related ecommerce security vulnerabilities. This occurs when an API relies on predictable identifiers without verifying that the requesting user is entitled to access the referenced resource. In practice, this can allow attackers to enumerate order numbers or account identifiers and retrieve other customers’ information.
Excessive data exposure is another common issue. APIs often return more information than is required for the client interface. Fields not displayed in the user interface may still be present in responses. These can include internal identifiers, pricing structures, or operational metadata. Over time, such information can support further compromise.
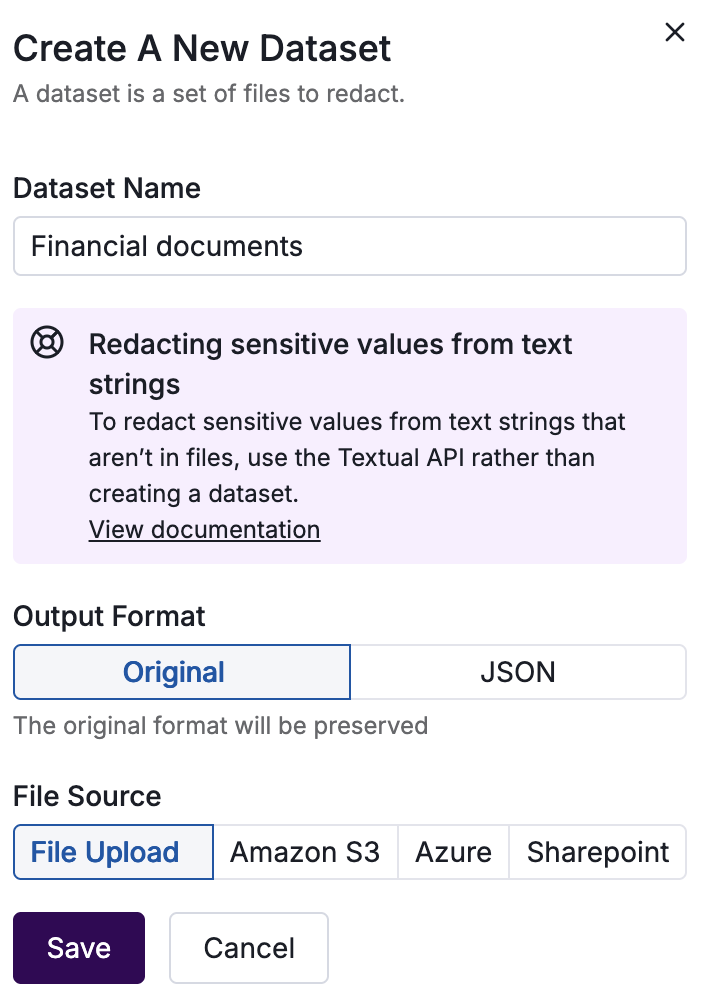
Authentication and token handling weaknesses are also prevalent. Poorly configured JSON Web Tokens, long lived API keys, or insufficient rate limiting can allow attackers to automate requests or replay credentials. In ecommerce environments with high transaction volumes, this can enable account takeover or large-scale data harvesting.
Dedicated API security testing helps ensure that authorisation logic, token validation, and response handling are robust across all exposed endpoints.
Secure cloud configuration for ecommerce environments
Behind the application and API layers, ecommerce platforms typically rely on cloud infrastructure. This may include virtual machines, containerised services, managed databases, object storage, and content delivery networks. Misconfigurations at this layer can expose sensitive endpoints and data even where the application itself is secure.
Publicly accessible storage remains a recurring issue. Object storage buckets and backup repositories sometimes contain database exports, customer records, or log files. If access controls are misconfigured, attackers may retrieve data directly without interacting with the application.
Overly permissive identity and access management policies are another common concern. Cloud roles granted excessive privileges can allow lateral movement if an attacker compromises a single component. For example, a vulnerable application server with broad permissions may be able to access databases or storage accounts beyond its intended scope.
Exposed management interfaces can also present risk. Administrative consoles, container orchestration dashboards, or database management endpoints are occasionally left accessible from the internet or other untrusted networks.
A structured cloud security assessment provides visibility into these infrastructure level weaknesses and helps ensure that access controls, network segmentation, and identity policies align with least privilege principles.
Third-party integrations and supply chain exposure
Ecommerce platforms are rarely self contained. Payment processors, marketing tools, analytics services, fulfilment providers, and customer engagement platforms are commonly integrated. Each connection introduces additional trust relationships, create new exposure points which need careful management.
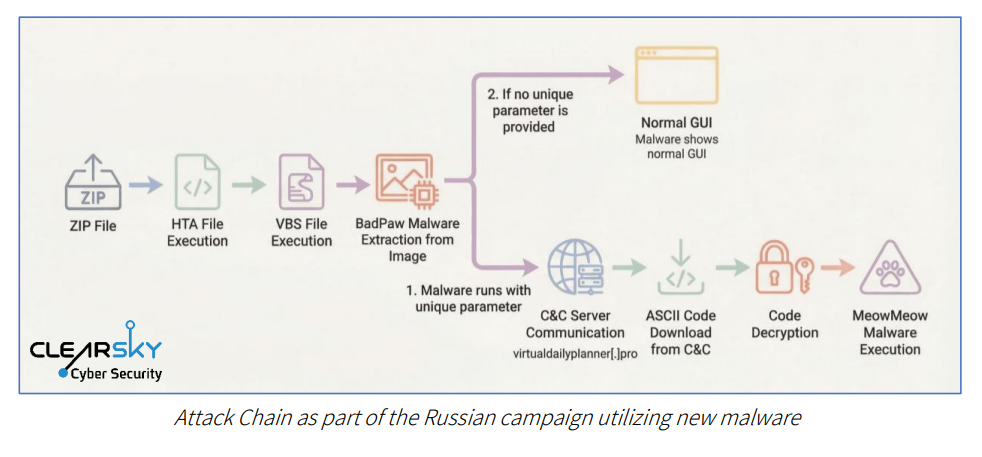
Weak validation of third-party callbacks, insecure webhook handling, or outdated plugins can all become entry points. In platforms built on widely used ecommerce frameworks, vulnerabilities within extensions or themes can have a substantial effect on large ecommerce environments.
From a risk management perspective, these integrations extend the definition of ecommerce security vulnerabilities beyond the primary codebases. They require consideration of dependency management, patching processes, and supplier assurance.
A balanced approach to ecommerce security testing
Given the complexity of modern ecommerce environments, isolated testing activities are rarely sufficient. A web application assessment may identify front end issues, injections, and logic flaws, while API vulnerabilities or cloud misconfigurations go undetected. Conversely, infrastructure assessments can overlook vulnerabilities in application workflows.
A layered approach to testing and control validation is therefore essential. Combining web application penetration testing, API security testing, and cloud security assessment activities provides a more complete view of exposure. Together, these disciplines address vulnerabilities in user interaction, system integration, and infrastructure configuration.
For organisations seeking to reduce ecommerce security vulnerabilities, the objective is not simply to identify individual flaws. It is to understand how weaknesses across different layers could be combined to create material impact.
How can Sentrium help?
Ecommerce platforms combine financial transactions, personal data, and operational dependencies within a single environment. This concentration of value ensures they are considered a priority target for attackers.
Common ecommerce security vulnerabilities span access control weaknesses, business logic flaws, API authorisation issues, cloud misconfigurations, and third party integration risks. Addressing these exposures requires a comprehensive and structured security strategy that reflects the nature of modern ecommerce architectures.
By taking a holistic view across application, API, and infrastructure components, organisations can strengthen resilience, reduce the risk of breaches, and maintain the trust that underpins online commerce.
Our team provides a range of penetration testing services that address the wide range of testing applicable to ecommerce businesses. Get in touch with our team to find out how we can help address your testing needs.
*** This is a Security Bloggers Network syndicated blog from Cyber security insights & penetration testing advice authored by Adam King. Read the original post at: https://www.sentrium.co.uk/insights/common-ecommerce-security-vulnerabilities-and-testing-strategies




.jpg)