AndyC
Global coalition dismantles Tycoon 2FA phishing kit
Tycoon 2FA, a major phishing kit and platform that allowed low-skilled cybercriminals to bypass multifactor authentication and conduct large-scale adversary-in-the-middle...
FBI Investigates Suspicious Activity in Surveillance Platform
Image: halfpoint/Envato The Federal Bureau of Investigation (FBI) is investigating suspicious cyber activity involving systems used to process surveillance and...
USENIX Security ’25 (Enigma Track) – Please (Don’t) Stop The Music: Adversarial Red-Teaming Of AI Music Generation Models
Author, Creator & Presenter: Jannis Kirschner, Niantic Inc. Our thanks to USENIX Security ’25 (Enigma Track) (USENIX ’25 for...
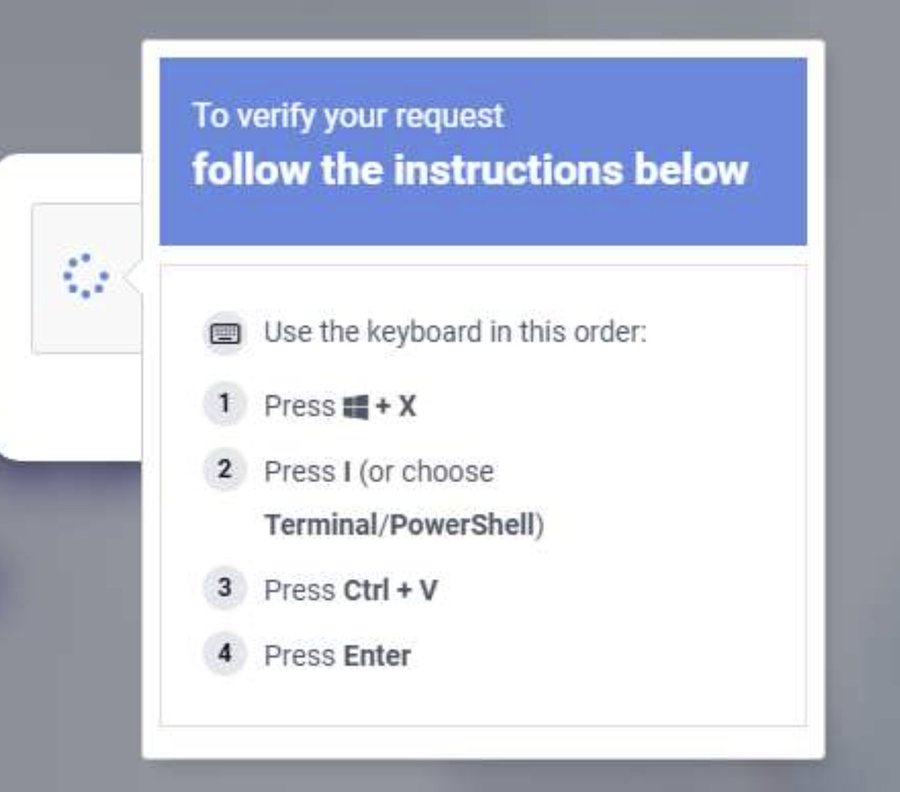
ClickFix attackers using new tactic to evade detection, says Microsoft
“And all Windows computers should already be restricted so that random, unsigned (not signed by the organization), PowerShell commands should...
Cisco flags ongoing exploitation of two recently patched Catalyst SD-WAN flaws
Cisco flags ongoing exploitation of two recently patched Catalyst SD-WAN flaws Pierluigi Paganini March 06, 2026 Cisco warns that two...
Microsoft warns of ClickFix campaign exploiting Windows Terminal to deliver Lumma Stealer
Microsoft warns of ClickFix campaign exploiting Windows Terminal to deliver Lumma Stealer Pierluigi Paganini March 06, 2026 Microsoft warns of...
How hackers bypassed MFA with a $120 phishing kit – until a global takedown shut it down
In a co-ordinated public-private operation between law enforcement agencies and cybersecurity industry partners one of the world's most prolific phishing-as-a-service...
5 Actions Critical for Cybersecurity Leadership During International Conflicts
The recent military attacks involving Iran in the Middle East are a stark reminder that cybersecurity leadership must...
Randall Munroe’s XKCD ‘Binary Star’
via the comic artistry and dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security...
European consumers ask EU to put a stop to digital enshittification
Online rights campaigners have come together to complain about the propensity of IT companies to make life more difficult for...
Leaked Mac benchmarks show that Apple offers tomorrow’s AI PCs today
In this day and age, it means how well your systems run artificial intelligence. We know that every single one...
Transparent Tribe Uses AI to Mass-Produce Malware Implants in Campaign Targeting India
Ravie LakshmananMar 06, 2026Threat Intelligence / Cyber Espionage The Pakistan-aligned threat actor known as Transparent Tribe has become the latest...
Multi-Stage VOID#GEIST Malware Delivering XWorm, AsyncRAT, and Xeno RAT
Cybersecurity researchers have disclosed details of a multi-stage malware campaign that uses batch scripts as a pathway to deliver various...
LexisNexis Hack Exposes 3.9M Records Through Unpatched React Vulnerability
Image: BleepingComputer A simple unpatched bug has led to a major breach, exposing millions of LexisNexis records. According to BleepingComputer,...