Anthropic’s Mythos leak is a wake-up call: Phishing 3.0 is already here
Anthropic’s leaked model made headlines this week. But the real story is what current AI models can already do to your inbox.
Anthropic’s Mythos leak is a wake-up call: Phishing 3.0 is already here
Anthropic’s leaked model made headlines this week. But the real story is what current AI models can already do to your inbox.
What happened
On March 27, Fortune reported that Anthropic accidentally exposed internal documents about an unreleased AI model called Claude Mythos. Their own draft blog post described it as posing “unprecedented cybersecurity risks” and being “far ahead of any other AI model in cyber capabilities.”
Cybersecurity stocks sold off immediately (CNBC). CrowdStrike and Palo Alto both dropped 7%. Tenable fell 11%. Anthropic has since confirmed the model exists and is in early testing with a small group of customers, with initial access restricted to cyber defense organizations (Techzine).
Whether Mythos ships or not, today’s models are already enough
Here’s what I keep coming back to: the conversation about Mythos is speculative. It’s based on a leaked draft. The model might ship next month or it might not ship for a year. But the debate about whether Mythos is real is missing the bigger point. What the leak actually did is compress how close the threat feels. It made something that security teams could comfortably file under “future problem” feel like a present one.
Current AI models, the ones available right now, are already powerful enough to change how phishing works.
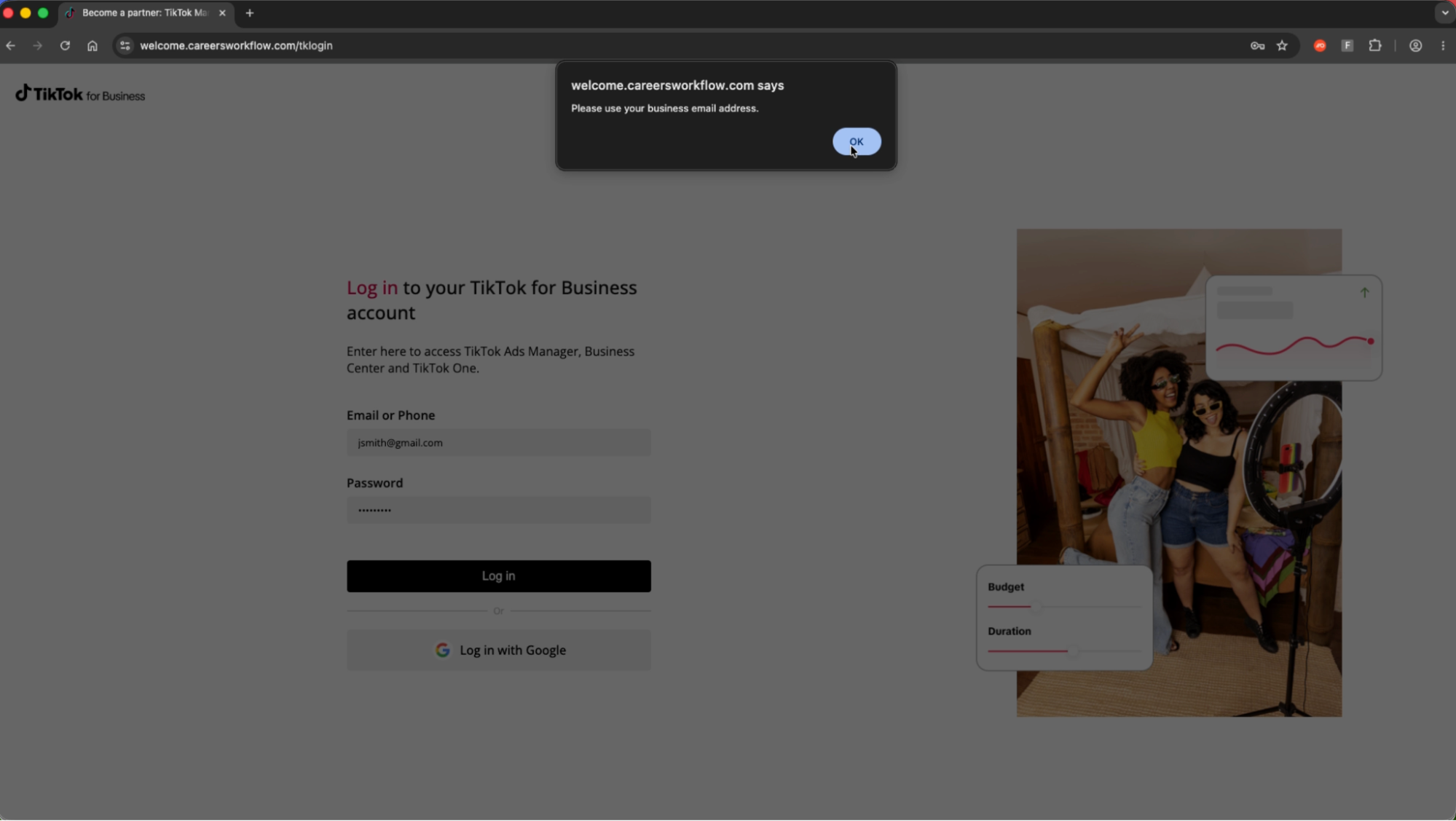
Today’s publicly available models can research a target organization by pulling context from LinkedIn, public filings, and company websites. They can generate phishing emails that match the tone and style of real internal communications. They can do this at scale, producing unique content for every recipient so there’s no repeating pattern for signature-based tools to catch. They can coordinate attacks across email, messaging, and voice channels simultaneously.
We know this isn’t hypothetical because it’s already happening. In November 2025, Anthropic disclosed that a Chinese state-sponsored group used Claude’s agentic capabilities to infiltrate roughly 30 organizations, including tech companies, financial institutions, and government agencies. That wasn’t Mythos. That was a model you can use today.
Now imagine what the next generation will allow.
This is what we mean by Phishing 3.0
At IRONSCALES, we’ve been tracking this shift for two years. We call it Phishing 3.0: the move from static, payload-based attacks (Phishing 1.0) and social engineering with no malicious payload (Phishing 2.0) to AI-powered, multi-channel attacks that adapt in real time and are unique to each recipient.
Legacy secure email gateways were built for Phishing 1.0. They apply static rules to known threat signatures. That approach was already struggling against Phishing 2.0. Against AI-generated attacks, these tools simply weren’t designed for what they’re now facing. Across 1,921 IRONSCALES customers, we catch an average of 67.5 phishing emails per 100 mailboxes per month that bypass existing defenses, including Microsoft 365 and legacy SEGs. Those are today’s numbers, against today’s attacks.
How we’re preparing
Our agentic AI capabilities, launching this month, were built for the class of threat the Mythos leak brings into focus. Not for one specific model, but for the broader reality that AI-powered attacks are here and getting more capable.
Red Teaming Agent
Our Red Teaming Agent researches your organization the way an attacker would. It identifies your most vulnerable employees, maps communication patterns, and generates realistic attack simulations that harden your detection before a real attack lands. If attackers are going to use Mythos-class models for reconnaissance, your defenses need to be tested against the same level of intelligence.
Phishing SOC Agent
When AI-powered attacks hit inboxes, your SOC team won’t have 30 minutes per incident to investigate manually. Themis, our agentic AI virtual SOC, classifies, clusters, and remediates threats autonomously. We’ve taken incident response from 30 minutes to 30 seconds. Over 99% of threats are handled without a human touching them.
Phishing Simulation Agent
Generic phishing simulations were already inadequate before Mythos. When attackers use AI reconnaissance to personalize every attack, training based on off-the-shelf templates doesn’t prepare your employees for what’s coming. Our Simulation Agent generates training scenarios based on real reconnaissance of your organization, so employees practice against the specific tactics they’ll actually face.
The Mythos leak got everyone’s attention this week. Good. It crystallized something defenders can no longer afford to dismiss. The attacks a model like Mythos would enable are already being tested with the tools available today. The question isn’t whether this class of threat is real. It’s how much time you have left to prepare.
See where you stand
Take an IRONSCALES Assessment to see how many phishing threats are bypassing your current defenses right now. Three clicks to deploy. The results will tell you whether your stack is ready for what’s already here, let alone what’s coming.
See what you’re missing >
Frequently asked questions
What is Claude Mythos?
Claude Mythos is an unreleased AI model from Anthropic that was accidentally revealed through a data leak on March 27, 2026. Anthropic confirmed it is in testing and described it as “a step change” in AI capability and “the most capable we’ve built to date.” The model sits in a new tier above Anthropic’s existing Opus line.
How does Claude Mythos affect email security?
Models with advanced reasoning and cybersecurity capabilities can generate personalized phishing emails at scale, coordinate attacks across email, messaging, and voice channels simultaneously, and identify zero-day vulnerabilities to embed in payloads. This increases both the volume and sophistication of email-based threats beyond what legacy detection tools can handle.
What is Phishing 3.0?
Phishing 3.0 is a term developed by IRONSCALES to describe the current era of AI-powered, multi-channel phishing attacks. Unlike Phishing 1.0 (malicious links and attachments) or Phishing 2.0 (BEC and social engineering), Phishing 3.0 involves generative AI creating unique, personalized attacks for each recipient, often spanning email, collaboration tools, and deepfake voice or video.
How do you protect against AI-powered phishing?
With agentic AI that red-teams your organization proactively, automates SOC-level incident response in seconds instead of minutes, and trains employees using reconnaissance-based simulations rather than generic templates. IRONSCALES’ platform combines adaptive AI, agentic automation, and crowdsourced human intelligence from 35,000+ security professionals to detect and remediate threats that bypass legacy tools.
Can legacy email gateways stop AI-generated phishing?
No. Secure email gateways were designed for known threat signatures and static content rules. AI-generated phishing produces unique content every time, so there is no signature to match. Behavioral AI that learns normal communication patterns and flags anomalies is the only reliable detection method for this category of attack. Across 1,921 IRONSCALES customers, legacy tools miss an average of 67.5 phishing emails per 100 mailboxes per month. (Explore the date here)
*** This is a Security Bloggers Network syndicated blog from Blog authored by Andrew Roehm. Read the original post at: https://ironscales.com/blog/anthropics-mythos-leak-is-a-wake-up-call-phishing-3.0-is-already-here