Microsoft’s Patch Tuesday Update Targets 120 Security Flaws

Microsoft’s Patch Tuesday Update Targets 120 Security Flaws
Microsoft’s May Patch Tuesday is a large one, even without a zero-day fire drill.
The company patched 120 vulnerabilities across Windows and other Microsoft products, including 31 remote code execution flaws and 61 privilege escalation flaws. Microsoft did not list any of the vulnerabilities as actively exploited at the time of release, but IT teams should still treat the update as a priority.
That matters because attackers often move quickly after patches land, using the fixes themselves as a map to build working exploits against unpatched systems.
Details of May’s Patch Tuesday
Microsoft released both security and feature updates for Windows 11 versions 24H2/25H2 (KB5089549) and 23H2 (KB5087420), while eligible Windows 10 devices received only security updates.
In general, Microsoft’s May cumulative updates include a mix of security patches, reliability improvements, and user-facing changes. Among the additions are File Explorer improvements, expanded archive format support, voice typing refinements, and the emergence of Xbox Mode on Desktops for gaming-focused experiences on Windows PCs.
The Windows 10 update focused on Remote Desktop warnings, Secure Boot, and a Daylight Saving Time update for users in Egypt.
Microsoft also says the update improves startup app performance and haptic feedback support for compatible pen accessories. Alongside these feature changes, the company patched 120 security flaws, organized into the following broader vulnerability types:
- Privilege Elevation Flaws (61): The highest in this month’s Patch Tuesday. Successful exploitation of this vulnerability will allow an attacker to execute malicious activities as admin, further increasing the exploit’s scope.
- Remote Code Execution, or RCEs (31): An RCE allows an attacker to control and run commands on a victim’s device remotely.
- Information Disclosure Vulnerabilities (14): This flaw could allow a threat actor to conduct stealthy reconnaissance and exfiltrate data from a victim’s device.
- Spoofing Flaws (13): Exploiting this flaw can allow a threat actor to impersonate a trusted user or service.
- Denial of Service (DoS) Vulnerabilities (8): A DoS exploit can render a Windows computer or service unavailable to legitimate users, which can significantly impact business continuity.
- Security Feature Bypass Vulnerabilities (6): Successfully exploiting this flaw can enable a threat actor to circumvent security systems such as SmartScreen or Windows Defender and run malicious software.
More Microsoft news
The highest-risk vulnerabilities to watch
Of the 120 fixed flaws, BleepingComputer highlights three that it says “could lead to remote code execution.” Users who interact with files are especially vulnerable to these three, as they can be executed by simply previewing a file, making them highly dangerous.
- CVE-2026-35421: A flaw that affects Windows Graphics Device Interface (GDI), the component used to render graphics and image formats. An attacker can create a specially crafted Enhanced Metafile (EMF) and then trick the target into opening it in Windows Paint.
- CVE-2026-40365: A Microsoft SharePoint Server RCE flaw that allows an authenticated attacker to send special requests to a SharePoint server, allowing the attacker to remotely execute code and move deeper inside the network of organizations using SharePoint, stealing data, and compromising more systems as they traverse.
- CVE-2026-41096: This one targets the Windows service responsible for DNS translations by sending a malicious response to a flawed Windows system, corrupting memory and enabling remote code execution on the affected system.
For a comprehensive list of all 120 patched vulnerabilities, see BleepingComputer’s full report.
Advertisement
No zero-days reported, but patching still matters
A zero-day exploit is the exploitation of a vulnerability in the wild before it becomes known and patched. That means that as of the time of release, all 120 vulnerabilities fixed in this month’s Patch Tuesday have no evidence of wild exploitation.
Although none of the 120 vulnerabilities are being actively exploited at this time, security experts generally warn that attackers tend to move quickly, either by reverse-engineering patched flaws to build new exploits or by targeting users and organizations that are slow to deploy updates.
As a result, Users and IT Admins should immediately patch all unpatched Windows systems. If automatic updates are enabled, your device should download the updates on its own. To manually check and install the updates, go to Settings > Windows Update > Check for Updates. This should download the available updates.
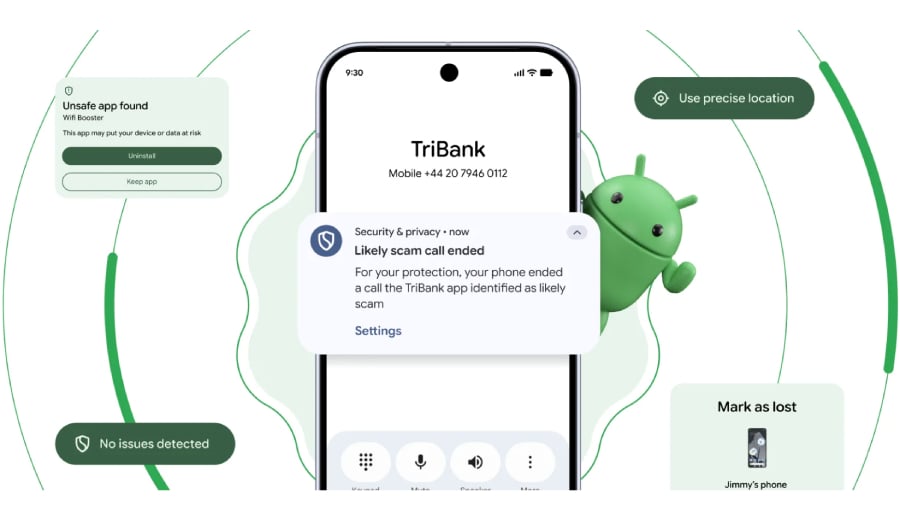
Also read: Google’s Android zero-click RCE patch gives IT teams another reminder to prioritize fast updates across high-risk devices.